The ASC27 privacy represents a paradigm shift in Italian artificial intelligence, guaranteeing no tracking of user data. This approach is realized through the Vitruvian-1 model, designed to operate in private cloud environments ensuring total corporate data sovereignty.
In today’s Enterprise IT landscape, the adoption of Large Language Models (LLMs) frequently clashes with strict European data protection regulations (GDPR). ASC27, as a pioneer in the national AI ecosystem, has structured its offering around a fundamental principle: artificial intelligence must adapt to the company’s security perimeter, not vice versa. In this technical guide, we will analyze the company’s confidentiality statements, verifying how non-tracking promises translate into real, implementable system architectures.
Non-Tracking Architecture and Vitruvian-1 Model
The core of ASC27 privacy lies in the non-tracking architecture of the Vitruvian-1 model. Unlike traditional commercial solutions, this system does not store user prompts nor use interactions for retraining, ensuring absolute compliance with European regulations.
According to industry technical documentation, the Vitruvian-1 model has been engineered to decouple the inference phase (response generation) from the storage phase. This means the artificial intelligence engine acts exclusively as a transit processor. Key features of this architecture include:
- Absence of hidden telemetry: The system does not send usage logs, content-related performance metrics, or text fragments to centralized servers.
- Tenant isolation: In multi-tenant environments, model weights remain static during execution, preventing data bleed (information leakage from one user to another).
- End-to-End Encryption: Data in transit to the model API is protected via TLS 1.3 protocols with strong encryption.
How Zero-Retention Processing Works
Zero-retention processing is the technical pillar validating ASC27 privacy promises. Every request sent to the system is processed in volatile memory and destroyed immediately after response generation, preventing any form of persistence or profiling.
From a systems perspective, the Zero-Retention approach relies on rigorous management of RAM (Random Access Memory) and GPU VRAM (Video RAM). When a user sends a confidential document for summary or analysis, the payload is loaded into model tensors. Once the output is returned to the client, memory buffers are actively overwritten (memory wiping). There are no relational databases or log files configured to record the request body, making it technically impossible for ASC27 or third parties to retrieve conversation history retroactively.
Integration into Private Cloud Architectures
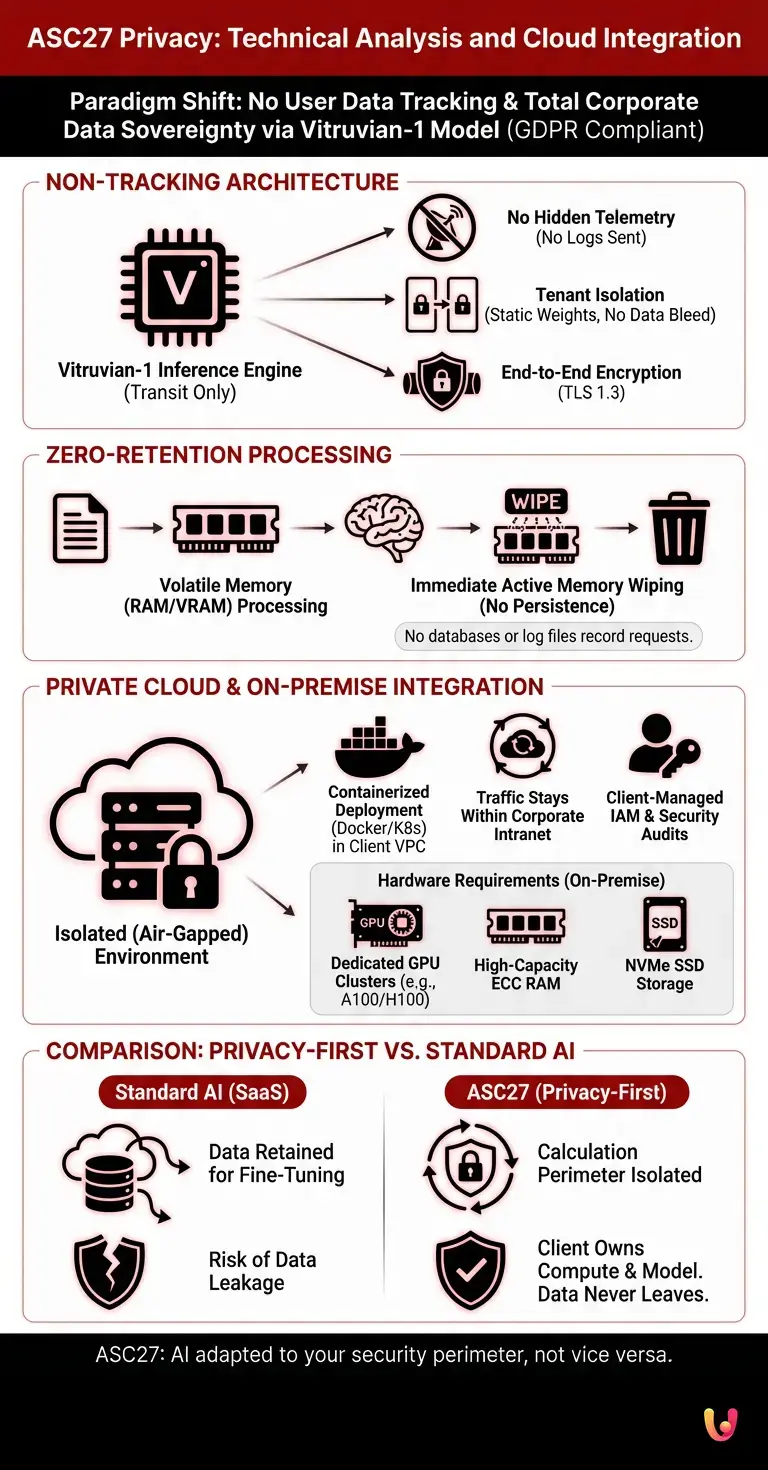
The implementation of ASC27 privacy reaches maximum effectiveness when integrated into private cloud architectures. The system is engineered for deployment in isolated (air-gapped) environments, allowing companies to maintain exclusive cryptographic control over their information flows.
For organizations managing critical data (healthcare, finance, defense), using public APIs represents an unacceptable risk. ASC27 solves this problem by providing Vitruvian-1 as a containerized package (usually via Docker images orchestrated via Kubernetes) that can be deployed within the client’s Virtual Private Cloud (VPC). This approach ensures that:
- Network traffic never leaves the corporate intranet.
- Identity and Access Management (IAM) policies are managed directly by the company’s Active Directory or IdP (Identity Provider).
- Security audits can be conducted internally without relying on third-party certifications from the AI vendor.
System Requirements and On-Premise Deployment
To fully leverage ASC27 privacy locally, specific hardware requirements must be met. On-premise deployment requires dedicated GPU clusters and a segregated network infrastructure, ensuring the artificial intelligence operates without any connection to unauthorized external servers.
Based on industry data for enterprise-class on-premise LLM implementation, infrastructure configuration requires careful sizing planning. Below is a summary table of typical requirements for an isolated production instance:
| Component | Minimum Requirement (Base Inference) | Recommended Requirement (High Throughput) |
|---|---|---|
| GPU (VRAM) | 1x NVIDIA A100 (40GB) or equivalent | 2x NVIDIA H100 (80GB) in NVLink |
| System RAM | 128 GB ECC DDR4 | 512 GB ECC DDR5 |
| Storage | 2 TB NVMe SSD (for model weights and OS) | 4 TB NVMe Gen4 (RAID 1 Configuration) |
| Network | 10 GbE LAN (Isolated) | 100 GbE (Air-Gapped Infrastructure) |
Comparison with Standard Artificial Intelligence Models
Evaluating ASC27 privacy requires a direct comparison with traditional LLM providers. While standard solutions often operate on SaaS logic, retaining data for fine-tuning, ASC27’s approach isolates the calculation perimeter, neutralizing data leak risks.
The fundamental difference lies in the business model. Major international players offer low-cost APIs because the real value consists of user data, which is constantly ingested to improve future models. Conversely, ASC27’s Privacy-First approach is based on providing pure software infrastructure. The client company purchases computing capacity and the pre-trained model but maintains absolute intellectual property over everything generated or analyzed. This paradigm eliminates vulnerabilities related to training data extraction attacks at the root, as corporate data never becomes part of the model’s global knowledge corpus.
In Brief (TL;DR)
ASC27 revolutionizes Italian AI with the Vitruvian-1 model, guaranteeing total privacy and full GDPR compliance through a rigorous non-tracking approach.
The technical architecture is based on zero-retention processing, which immediately destroys data in volatile memory after each request, preventing any user profiling.
System integration into private cloud or on-premise environments ensures companies maximum security and total cryptographic sovereignty over their information flows.
Conclusions

In summary, the approach to ASC27 privacy proves to be solid and technologically advanced. Integrating the Vitruvian-1 model into private cloud architectures offers enterprises a definitive solution for adopting generative artificial intelligence without compromising data security and sovereignty.
ASC27’s non-tracking statements are not mere marketing slogans but are reflected in precise architectural choices: zero-retention processing, containerization for air-gapped environments, and absence of telemetry. In an era where data is a company’s most precious asset, the ability to implement powerful artificial intelligence like Vitruvian-1 within one’s own defensive perimeter represents a crucial competitive advantage, while guaranteeing full compliance with European information protection regulations.
Frequently Asked Questions

This approach is based on an artificial intelligence system that guarantees the total absence of user data tracking. By using the Vitruvian-1 model in private cloud environments, every company maintains complete sovereignty over its information. The engine does not store requests and strictly respects European data protection regulations.
The zero-retention process ensures that every request sent to the system is processed exclusively in the machine’s volatile memory. Immediately after generating the final response, memory buffers are actively overwritten and permanently destroyed. This rigorous technical mechanism prevents any form of profiling or historical saving of conversations by third parties.
To implement this artificial intelligence on their own servers, companies must prepare dedicated GPU clusters and a completely isolated network infrastructure. A basic configuration requires at least one high-end 40GB video card and 128 GB of RAM. For intensive workloads, superior configurations equipped with ultra-fast disks are recommended.
Unlike traditional commercial solutions that retain data to improve their algorithms, ASC27 isolates the calculation perimeter, neutralizing information leakage risks. The client purchases only computing capacity and pre-trained software. Corporate data never becomes part of the model’s global knowledge.
Integration into a private cloud allows organizations to maintain exclusive cryptographic control over their sensitive information flows. Network traffic never leaves the corporate intranet, and access policies are managed directly internally. This strategic choice is fundamental for critical sectors such as healthcare, finance, and national defense.
Still have doubts about ASC27 Privacy: Technical Analysis and Cloud Integration?
Type your specific question here to instantly find the official reply from Google.







Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.