We live in the era of compulsive imagery. Every day, billions of photographs are taken, filtered, and shared in real time on social networks or via messaging apps. We capture a sunset, an elaborate dish at a Michelin-starred restaurant, a child’s smile at the park, or a simple mirror selfie before leaving the house. Yet, amidst this visual frenzy, we almost systematically overlook a crucial detail: the image we see on the screen is merely the tip of the iceberg. Beneath the surface of colored pixels lies a silent and incredibly precise archive known as EXIF metadata . This is the core entity, the true secret behind the frame—the invisible information that, without even realizing it, you package and gift to the world with every single shot.
The Anatomy of a Shot: Beyond the Pixels
To fully understand the nature of this phenomenon, we must take a step back and analyze how modern digital photography works. When we press the shutter button on our smartphone or digital camera, the sensor does not merely record light and color. The image processor, guided by complex algorithms, instantly compiles a sort of “identity card” for the file. This standard, known as the Exchangeable Image File Format (or EXIF), was created to embed technical data directly within the image file (typically JPEG or TIFF).
Initially, metadata served purely technical and professional purposes. It recorded the camera model, exposure time, aperture, ISO sensitivity, and whether or not the flash was used. This information was—and remains—invaluable to photographers wishing to analyze, after the fact, the settings used to achieve a specific result. However, with the advent of smartphones and the convergence of mobile technology , this data set has expanded exponentially, transforming into a veritable personal tracking tool.
The Silent Witness: Geolocation
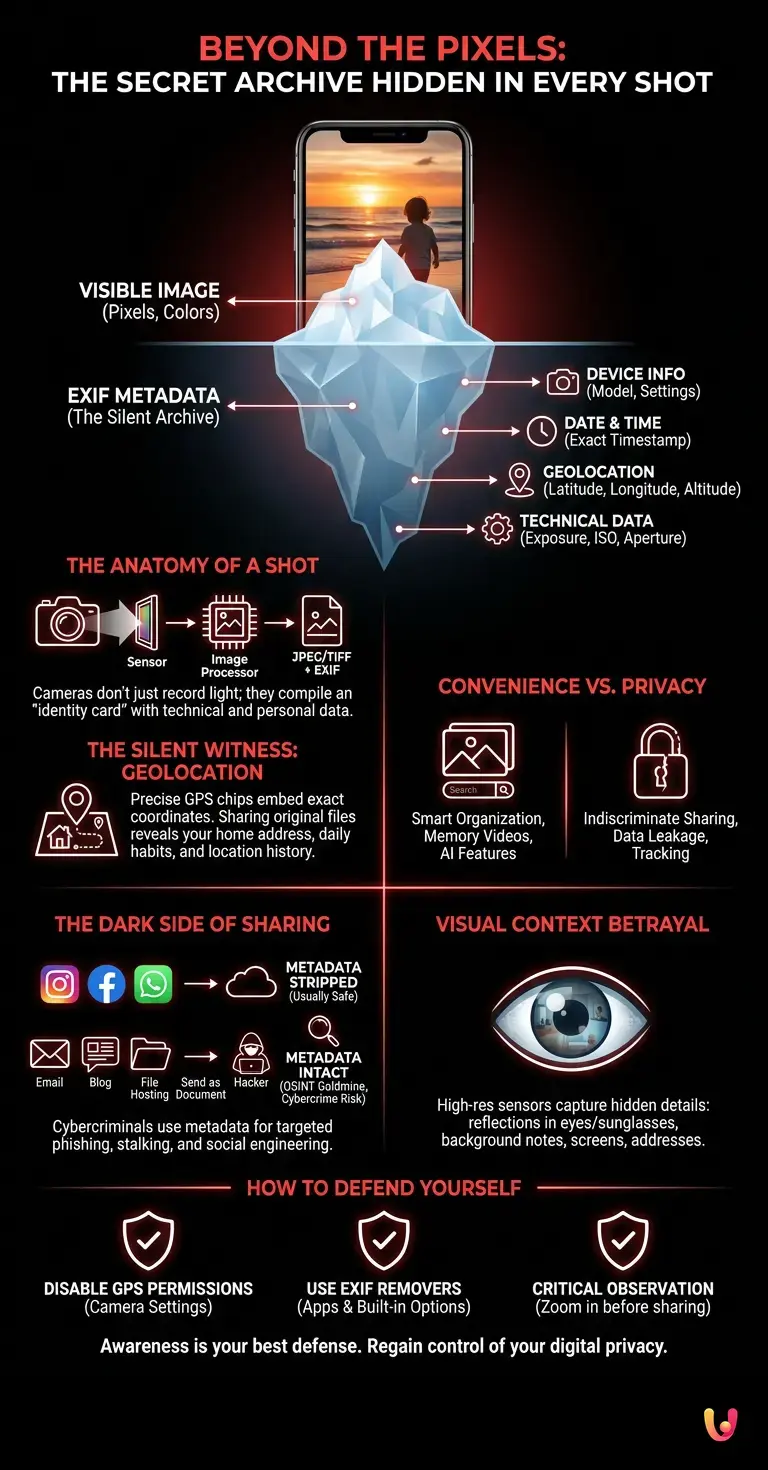
The most critical and potentially invasive element of modern metadata is undoubtedly geotagging. Our phones are equipped with extremely precise GPS chips capable of triangulating our position with a margin of error of just a few meters. If the camera’s location settings are enabled (as they often are by default), every photo we take is indelibly stamped with the exact coordinates of latitude, longitude, and even altitude.
Imagine taking a photo of your new puppy in your living room and sending it as an original file to an enthusiast forum or via email. Anyone who downloads that image and views its properties (an operation requiring just two clicks on any computer) will see more than just an adorable dog. They will see your exact home address, the floor you are on, the date and the exact second you were present in that room, and the exact model of phone you own. You have just provided, in a completely invisible way, a comprehensive dossier on your habits and your location.
Why do devices record all of this?
The question naturally arises: why do hardware and software manufacturers implement features that seem to undermine our privacy so profoundly? The answer lies in convenience and user experience, the true drivers of digital innovation . Metadata allows the photo galleries on our phones to organize our memories intelligently. It is thanks to this invisible information that you can search for “Rome 2022” or “Beach” in your smartphone’s search bar and see all relevant photos magically appear.
Operating systems use machine learning combined with EXIF data to create those touching, automated memory videos by grouping photos taken in the same location and during the same period. The technology itself is not malicious; it is designed to simplify our lives, creating a seamless ecosystem where our memories are always organized and accessible. The problem arises when this convenience clashes with indiscriminate external sharing.
The Dark Side of Sharing: Privacy Risks
In the vast world of cybersecurity , metadata analysis is considered one of the fundamental techniques of OSINT ( Open Source Intelligence )—that is, the gathering of information through open and public sources. What is merely a simple snapshot to the average user is a goldmine for an analyst or, worse, for a malicious actor.
Many people believe they are safe because they share photos on popular social networks. To some extent, this is true: platforms such as Instagram, Facebook , or X (formerly Twitter), as well as messaging apps like WhatsApp or Telegram (when sending compressed images), automatically remove EXIF metadata during the upload process, specifically to protect user privacy and reduce file sizes on their servers. However, the pitfalls lie elsewhere.
If you send a photo via email , upload it to a personal blog, share it on file-hosting platforms, or send it through messaging apps by selecting the “send as document” option (often used to preserve image quality), the metadata remains intact. In a corporate environment, cybersecurity is constantly put at risk by employees who, in good faith, share photos of trade shows, offices, or prototypes, inadvertently attaching sensitive data regarding company locations or working hours.
How Cybercriminals Exploit the Invisible
The practical implications of this invisible data leak can be unsettling. Cybercriminals use metadata to orchestrate highly targeted social engineering attacks. Knowing that a person regularly visits a specific café every Tuesday morning—information gleaned from a series of photos uploaded to a personal blog—allows an attacker to craft extremely convincing phishing emails, perhaps by posing as the manager of that establishment.
Even more serious is the risk associated with stalking and physical safety. There have been documented cases in which celebrities or ordinary individuals were tracked down by malicious actors who simply extracted GPS coordinates from photos published on websites that did not strip (remove) EXIF data. It is no coincidence that many startups in the digital defense sector are developing increasingly sophisticated software for businesses, capable of automatically scanning and sanitizing every multimedia file leaving the corporate network, thereby preventing accidental data leaks.
Not Just Technical Data: The Betrayal of the Visual Context
The secret of a shot, however, is not limited solely to the digital data embedded in the file. There exists another form of invisible information—or rather, visible yet often ignored: the physical context. Modern cameras have achieved staggering resolutions. Sensors with 48, 100, or even 200 megapixels capture details that the human eye does not perceive in the slightest at the moment the picture is taken.
Security experts regularly analyze reflections. A selfie taken while wearing mirrored sunglasses can reveal exactly who is standing in front of you, the architecture of the room, or even the content of the computer screen you are viewing. Reflections in the pupils of the eyes, in ultra-high-resolution photos, have been used in forensic investigations to identify locations or people present in a room.
Furthermore, there are the background details: a sticky note attached to the monitor with a password, a piece of mail on the table with a clearly legible home address, a company ID badge hanging around one’s neck, or the view outside the window that makes it possible to pinpoint the exact floor and angle of the building one is in. When we frame the main subject, our brain filters out the background noise, but the camera lens is ruthlessly objective: it records everything with the same sharpness.
How to defend yourself and regain control
Awareness is the first and most effective line of defense. Knowing that every photo is a potential repository of sensitive data radically changes our approach to digital photography. Fortunately, regaining control of your privacy is a relatively simple process that requires only a few precautions.
The first step is to manage location permissions. On both iOS and Android, you can access your privacy settings and revoke the Camera app’s permission to access GPS. This will prevent the creation of geotags entirely, while keeping other technical data (such as date and time) intact. If you wish to retain the convenience of having geolocated photos for personal use, it is essential to learn how to remove this data before sharing.
Modern mobile operating systems offer built-in options for doing this. When sharing a photo from your gallery, there is often an “Options” button that allows you to exclude location data and all other metadata before sending. Additionally, there are dozens of free and open-source applications dedicated exclusively to viewing and removing EXIF data (so-called EXIF scrubbers or metadata removers ).
When it comes to visual contextual information, the golden rule is critical observation. Before sending a photo, especially one taken in a private or professional setting, it is good practice to zoom in on the background details. Always ask yourself: “Is there anything in this frame that I wouldn’t want a stranger to see?”
In Brief (TL;DR)
Every digital photograph conceals EXIF metadata beneath its pixels—an invisible archive that records technical details and valuable personal information.
Our smartphones record GPS coordinates and technical details to organize memories, transforming every snapshot into an extremely precise personal tracker.
Sharing original files exposes us to serious privacy risks, handing anyone a complete dossier on our locations and daily habits.
Conclusions

Digital photography has democratized the art of capturing memories, transforming each of us into a visual chronicler of our own existence. However, this ease of use has brought with it a dangerous technological naivety. The secret of framing lies precisely in this duality: the image we admire is merely the aesthetic interface of a much deeper and more revealing database.
Understanding the existence and function of EXIF metadata, as well as the importance of visual context, does not mean having to stop taking photos or sharing your happy moments. Rather, it means evolving from passive users into informed digital citizens. In an era where our personal data is the most valuable currency in the global market, learning to filter the invisible information we give away with every snapshot is a fundamental act of self-defense and identity protection.
Frequently Asked Questions

This data acts as a comprehensive identification profile for the image file. It consists of hidden information automatically recorded by your phone or camera at the moment the photo is taken. It includes technical details such as the device model, the date, the exact time, and the GPS coordinates of your location.
Sending an original image file via email or as an uncompressed document exposes your personal data to anyone who receives the file. A malicious actor can easily extract geographic coordinates and details about your habits, using this information for targeted cyberattacks or to track your physical movements.
Major social media platforms and messaging apps automatically remove this information during the upload process to protect users and reduce server load. However, the risk remains high if you choose to send images via email, personal blogs, or storage services without first stripping this data.
The most effective method is to disable location permissions for the camera directly from your smartphone’s settings. Alternatively, you can use the options built into mobile operating systems or download specific applications to remove all sensitive information before sharing.
Beyond invisible digital data, ultra-high-resolution sensors capture physical details that are often ignored by our brains. Reflections in sunglasses, sticky notes with passwords attached to a monitor, or views outside a window can reveal your exact location or confidential corporate information to anyone analyzing the image.
Still have doubts about Beyond the Pixels: The Secret Archive Hidden in Every Shot?
Type your specific question here to instantly find the official reply from Google.







Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.