The most dangerous false myth of the modern web is believing that using an app with end-to-end encryption makes you completely invisible and anonymous. The counter-intuitive truth is that, while the content of your messages is locked down, your “metadata”—who you talk to, at what time, from where, and for how long—often remains exposed on company servers. If you think a green padlock is enough to guarantee absolute privacy, you are ignoring the most vulnerable half of your digital footprint.
Write a message to see how it is transformed during its journey on the server and how it arrives at the recipient.
What is end-to-end encryption and how does it work?
End-to-end encryption is a secure communication system where only the sender and recipient can read messages. It works using a pair of digital keys, preventing hackers, internet providers, and even app operators from deciphering the content.
To understand this mechanism without resorting to complex mathematical formulas, imagine the process as a system of physical locks and keys. When you decide to communicate with a friend, your device and theirs each generate two keys: a public key and a private key .
- Public Key: It's like an open padlock that you can distribute to anyone. Anyone who wants to write to you uses your padlock to lock the message.
- Private Key: This is the only real key that can open that lock. This key never leaves your device and is jealously guarded by the operating system.
When you send a message, your phone uses the recipient's "lock" (public key) to seal the text. While traveling over the internet and company servers, the message travels encrypted. No one, not even the company that manages the servers, has the key to open it. Only when it arrives at your friend's phone does their private key unlock and reveal the original text.
The metadata problem: what remains uncovered
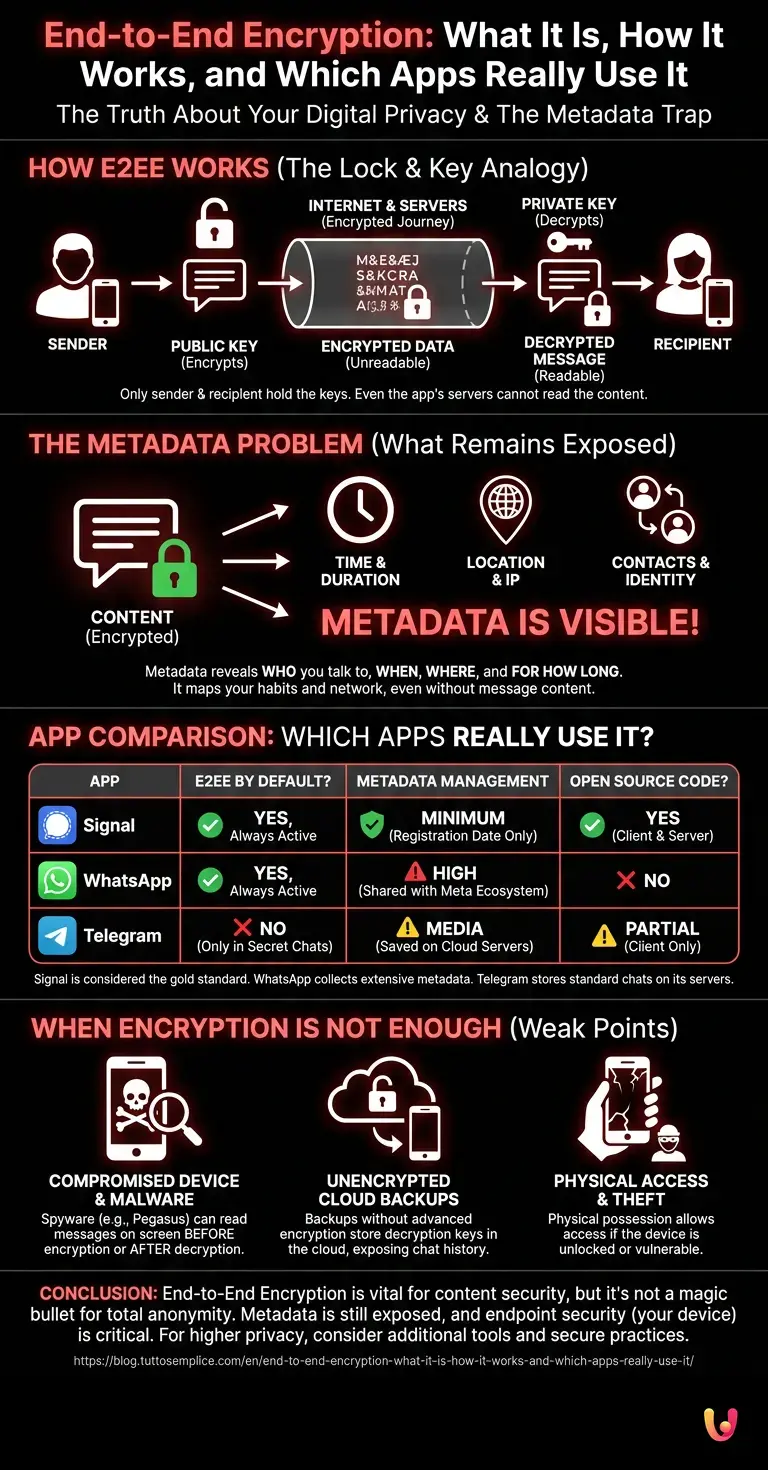
Even when using end-to-end encryption , communication metadata is not hidden. This data includes the time of the message, IP addresses, and the identity of the interlocutors, providing a detailed picture of your habits without revealing the text.
Metadata is the real treasure of the digital age. If the content of the message says what you are saying, the metadata says who you are and what you do . Knowing that you called an oncology center at 2 a.m. and talked for 45 minutes reveals extremely sensitive information, even if no one listened to a single word of the conversation.
Law enforcement and intelligence agencies often don't need to decipher messages; they simply analyze metadata to map contact networks, habits, and geographic locations. This is why total privacy requires additional tools, such as the use of VPNs or decentralized networks, to also obscure connection traces.
Which messaging apps actually use E2EE?
Not all apps implement end-to-end encryption in the same way. Signal offers it by default with maximum privacy, WhatsApp uses it for messages but collects metadata, while Telegram only requires it in secret chats, leaving normal chats on its servers.
There is a lot of confusion about which applications offer real security. Let's analyze the three most popular platforms to understand the structural differences:
| Application | E2EE by Default? | Metadata Management | Open Source Code |
|---|---|---|---|
| Signal | Yes, always active. | Minimum (registration date only) | Yes (Client and Server) |
| Yes, always active. | High (shared with the Meta ecosystem) | No | |
| Telegram | No (only in "Secret Chats") | Media (saved on cloud servers) | Partial (Client Only) |
According to Signal 's official documentation, their open-source protocol is considered the gold standard of cybersecurity. WhatsApp uses the same protocol as Signal to encrypt messages, but being owned by Meta, it collects a vast amount of metadata for analytical and commercial purposes. Telegram , contrary to popular belief, saves standard chats in plain text (or rather, encrypted but with the keys held by Telegram itself) on its cloud servers, making E2EE a purely manual and non-default option.
When encryption is not enough
Relying solely on end-to-end encryption is not enough if the device itself is compromised . Malware, unauthorized screenshots, unencrypted cloud backups, or physical theft of the smartphone can expose your messages before they are encrypted or after they have been decrypted.
The security of a computer system is only as strong as its weakest link. In cryptography, the weak links are the "endpoints"—your phone and the recipient's phone. If your operating system is infected with spyware, it can read the screen or record keystrokes before the app applies encryption.
Furthermore, a common mistake is to enable cloud backups (such as Google Drive or iCloud) without enabling advanced encryption for the backups themselves. In this scenario, the decryption keys are stored in the cloud, allowing anyone with access to your account to read your entire chat history.
Real-World Case Study: Pegasus Spyware
In 2019, it was revealed that the Pegasus spyware, developed by the NSO Group, was used to infect the smartphones of journalists and activists around the world. By exploiting "zero-day" vulnerabilities, Pegasus gained root-level access to the devices. This allowed attackers to read WhatsApp and Signal messages directly from the victims' screens, completely bypassing end-to-end encryption, as the data was intercepted after being legitimately decrypted by the device itself.
Conclusions

In summary, end-to-end encryption is a fundamental tool for cybersecurity, but it is not a magic wand. Understanding its limitations and protecting your devices is essential to ensuring true digital privacy in the modern world.
We have seen how the exchange of public and private keys protects the content of our conversations from prying eyes, but we have also debunked the illusion of absolute anonymity. Metadata tells our story silently, and the architectural differences between apps like Signal, WhatsApp, and Telegram show that not all green locks offer the same level of guarantee.
For 360-degree security, it is vital to combine the use of secure applications with good digital hygiene practices: keep operating systems updated, avoid suspicious links, and disable unprotected cloud backups. Only by adopting a holistic approach can you regain full control of your personal and professional communications.
Frequently Asked Questions

Signal represents the highest standard for cybersecurity as it offers default encryption and minimizes the collection of personal data. WhatsApp protects texts by default but shares a lot of contextual information with its corporate ecosystem, while Telegram requires you to manually activate secret chats to obtain real protection.
Metadata are the digital traces that indicate who you communicate with, from what geographical location, at what time and for how long, while keeping the text of the conversation hidden. This contextual information allows companies and government agencies to profile your habits with extreme precision and map your network of contacts without having to decipher any messages.
Encryption only protects data while it is in transit over the internet between the sender's and recipient's devices. If your smartphone is infected with spyware or is physically stolen, malicious actors can read conversations directly from the screen before they are locked or immediately after they are unlocked by the operating system.
To prevent conversations from being read by strangers, it is absolutely essential to enable advanced encryption for archives saved on external cloud services as well. Without this specific precaution, the unlock keys are stored in plain text on the provider's servers, rendering the protection originally applied by the messaging software during the sending phase completely useless.
The security mechanism is based on two complementary digital elements automatically generated by each user's device. The public key works like an open padlock that anyone can use to seal a text, while the private key always remains hidden in the recipient's phone and is the only mathematical tool capable of unlocking and revealing the original content.
Still have doubts about End-to-End Encryption: What It Is, How It Works, and Which Apps Really Use It?
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading







Did you find this article helpful? Is there another topic you'd like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.