Have you ever navigated to a webpage, ready to purchase a concert ticket or log into your bank account, and braced yourself for the inevitable grid of blurry images? You expect to be asked to identify crosswalks, bicycles, or traffic lights to prove your humanity. Yet, the page simply loads. You are granted access without a single click, puzzle, or checkbox. This seamless experience is not a glitch, nor is it a lapse in the website’s defenses. Instead, it is the result of a highly sophisticated, silent evaluation happening entirely in the background. Welcome to the era of behavioral biometrics, the invisible test your browser runs before you even realize it.
The End of the Traffic Light Era
To understand why this invisible test exists, we must first look at the history of human verification on the internet. For over two decades, the web relied on CAPTCHAs (Completely Automated Public Turing test to tell Computers and Humans Apart). Early iterations forced users to decipher heavily distorted text. When optical character recognition software became adept at reading those squiggly lines, the system evolved into image recognition tasks.
However, this created a frustrating user experience. Legitimate users were frequently locked out because they missed a single pixel of a motorcycle in a grainy photograph. Furthermore, the rapid advancement of machine vision meant that automated scripts could eventually solve these visual puzzles faster and more accurately than humans. The tech industry realized that relying on active user input to prove humanity was a losing battle. A new paradigm was required—one that shifted the burden of proof away from the user and onto the machine.
How Does It Work? The Secret Behind the Screen
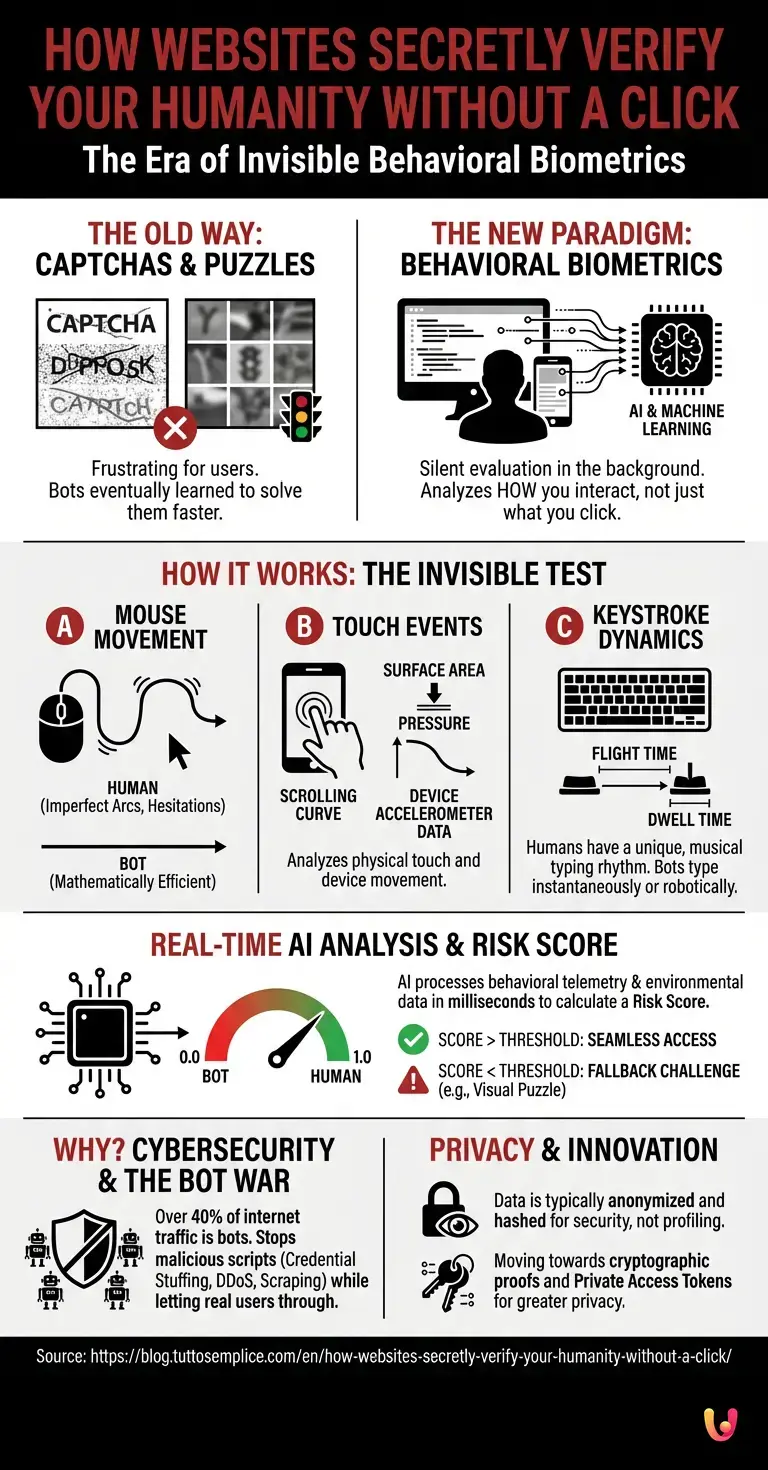
The core philosophy behind the invisible test is simple: it is no longer about what you click, but how you arrive at the click. Long before your cursor hovers over a “Submit” button, a silent script is already collecting dozens of telemetry data points to build a profile of your current session.
One of the primary metrics analyzed is mouse movement trajectory. When a human moves a computer mouse or swipes on a trackpad, the motion is inherently imperfect. We create slight arcs, exhibit micro-tremors, hesitate for fractions of a second, and often overshoot our target before correcting. A bot, programmed to click a button, will typically move the cursor in a perfectly straight, mathematically efficient line from point A to point B. Even if a bot is programmed to simulate randomness, generating truly human-like, chaotic motion is computationally difficult and easily detectable by advanced algorithms.
On mobile devices, where there is no mouse, the system analyzes touch events. It measures the surface area of your fingertip on the glass, the pressure applied, the slight curve of your scrolling motion, and the accelerometer data of the device itself. A phone resting perfectly still on a server rack while rapidly scrolling through a webpage is a massive red flag.
The Rhythm of Your Keystrokes
Beyond cursor movements, the invisible test closely monitors keystroke dynamics. If you are filling out a form, the system measures two critical timeframes: flight time (the duration between releasing one key and pressing the next) and dwell time (how long a single key is held down).
Humans type with a distinct, almost musical cadence. You might type your own name incredibly fast, pause to remember your password, and hold the “Shift” key slightly longer than other keys. Automated scripts, on the other hand, inject text into form fields instantaneously or type at a perfectly uniform, robotic speed. By analyzing these microscopic variations in timing, the browser can confidently distinguish a living, breathing user from a malicious script.
The Role of AI and Machine Learning
Collecting this vast amount of behavioral data is only half the battle; interpreting it in real-time requires immense computational power. This is where AI steps in. Modern invisible verification systems are powered by sophisticated machine learning models that have been trained on billions of human and bot interactions.
As you navigate a site, the AI continuously processes your behavioral telemetry alongside environmental data—such as your IP address reputation, browser fingerprint, installed fonts, and screen resolution. Within milliseconds, the AI calculates a “Risk Score,” typically ranging from 0.0 to 1.0. A score of 0.9 indicates a high probability that you are a human, allowing you to proceed without friction. A score of 0.1 suggests you are a bot, triggering defensive measures. This complex calculation happens so quickly that it is entirely imperceptible to the end user.
Cybersecurity and the Bot War
Why do websites go to such extraordinary lengths to verify your identity? The answer lies in the escalating war of cybersecurity. Today, over 40% of all internet traffic is generated by bots, and a significant portion of that traffic is malicious.
Cybercriminals deploy armies of automated scripts to execute credential stuffing attacks (testing stolen passwords across thousands of accounts), scrape proprietary content, hoard limited-edition inventory (like concert tickets or sneakers), and launch Distributed Denial of Service (DDoS) attacks. If websites did not have a robust, invisible layer of defense, digital commerce would grind to a halt. The invisible behavioral test acts as a silent bouncer, keeping the digital ecosystem safe from automated exploitation while leaving the front door wide open for legitimate customers.
Startups and Innovation in the Space
While tech giants like Google pioneered this space with tools like reCAPTCHA v3, the demand for better, more privacy-conscious verification has sparked a wave of innovation. A multitude of agile startups and established infrastructure companies are entering the fray, challenging the status quo.
Companies like Cloudflare have introduced alternatives like Turnstile, which rely heavily on cryptographic proofs and hardware-level checks rather than purely behavioral tracking. Other startups are focusing on “Private Access Tokens,” a technology developed in collaboration with Apple and Google that allows the operating system itself to vouch for the user’s humanity without sharing any personal data with the website. This vibrant ecosystem ensures that the technology is constantly evolving, staying one step ahead of increasingly sophisticated bot networks.
What Happens If You Fail the Test?
Despite the accuracy of these systems, false positives do occur. You might be using a heavily restricted corporate VPN, browsing in strict incognito mode with anti-tracking extensions, or simply moving your mouse in an unusually rigid manner. If your risk score drops below the acceptable threshold, the system does not immediately ban you.
Instead, it triggers a fallback mechanism. This is when the invisible test suddenly becomes visible. You will be presented with a traditional challenge—perhaps a classic image grid, a slider puzzle, or a request to verify your email. This “step-up” authentication ensures that legitimate users who happen to trigger a security flag still have a pathway to access the content they need.
Privacy Concerns: Are We Being Watched Too Closely?
The revelation that websites are silently tracking your mouse movements, typing speed, and hardware configurations naturally raises privacy concerns. In an era where digital privacy is fiercely debated, the idea of a background script analyzing your physical behavior can feel invasive.
However, reputable providers of behavioral biometrics anonymize this data. The system does not care who you are; it only cares what you are. The telemetry data is typically hashed and used exclusively for the purpose of bot mitigation, not for targeted advertising or personal profiling. Furthermore, the broader tech industry is actively moving toward cryptographic verification methods that require zero behavioral tracking, aiming to provide the same level of security with absolute privacy.
In Brief (TL;DR)
Traditional visual puzzles are being replaced by seamless background technologies that verify your humanity without requiring any frustrating clicks.
Modern websites analyze unique behavioral biometrics, such as imperfect mouse movements and natural keystroke rhythms, to silently detect genuine human activity.
Advanced artificial intelligence processes continuous behavioral telemetry instantly, assigning a risk score to block malicious bots while allowing legitimate users effortless access.
Conclusion

The internet is a battlefield of automation, but for the average user, the war is entirely invisible. The transition from frustrating visual puzzles to silent, background verification represents one of the most significant usability upgrades in web history. By analyzing the subtle, chaotic, and uniquely human ways we interact with our devices, behavioral biometrics have managed to bridge the gap between rigorous security and seamless user experience.
The next time you log into a website and breeze past the login screen without having to prove you aren’t a robot, take a moment to appreciate the complex machinery working in the background. Your browser has already tested you, analyzed your human imperfections, and quietly opened the door.
Frequently Asked Questions

Behavioral biometrics analyze how you physically interact with your device rather than what you click. Websites use this advanced technology to track mouse movements, typing speed, and touch pressure to silently verify your human identity. This ensures a secure and seamless browsing experience without the need for frustrating visual puzzles.
These silent security tests collect telemetry data like cursor trajectories, keystroke dynamics, and device information while you browse. An artificial intelligence system processes this vast amount of data in real time to calculate a specific risk score. If your behavior appears naturally imperfect, you are granted access instantly without any visible prompts.
Websites monitor these physical interactions primarily to protect their platforms against cyberattacks and malicious automated scripts. Humans move a cursor with slight imperfections and type with a unique rhythm, whereas bots operate with mathematical precision. Tracking these subtle differences helps security systems block hackers while keeping the site perfectly accessible for real users.
If your calculated risk score drops below a certain threshold due to strict privacy settings or unusual browsing behavior, you will not be immediately banned from the site. Instead, the security system triggers a standard fallback mechanism. You will simply be asked to solve a traditional visual puzzle to prove your identity.
While background tracking might feel invasive to some users, reputable security providers completely anonymize your behavioral data. The collected information is hashed and used strictly to prevent automated cyberattacks, rather than for targeted advertising or personal profiling. Furthermore, new technologies are constantly emerging that use cryptographic proofs to verify humanity without tracking behavior.
Still have doubts about How websites secretly verify your humanity without a click?
Type your specific question here to instantly find the official reply from Google.







Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.