The most widespread misconception in the financial world is the belief that keeping a plastic card tucked away in one’s wallet is the safest way to protect one’s money. The reality is exactly the opposite: the traditional physical card now represents the weak link in contactless payment security . Entrusting your data to systems like Apple Pay or Google Pay is not a technological risk, but a massive security upgrade, as it eliminates the danger of cloning, skimming, and physical theft at the root, thanks to cryptographic technologies that a piece of plastic can never support.
Vulnerability Scanner
Discover your level of exposure to contactless fraud.
Real-World Case Study: The Impact of Tokenization (Visa Data)
According to official reports released by Visa Inc., the introduction of tokenization technology in mobile payments has led to a 28% overall reduction in digital fraud compared to traditional physical card transactions. This mathematically demonstrates how the absence of the actual PAN (Primary Account Number) during the transaction neutralizes attempts to intercept data.
How the Technology Behind Payments Works
To fully understand the security of contactless payments , it is essential to analyze how data travels from the device to the POS terminal. While a physical card transmits actual data in plain text, digital wallets use advanced encryption to mask every single transaction, rendering the data unreadable.
Both physical cards and smartphones use NFC (Near Field Communication) technology to communicate with payment terminals. However, the similarity ends there. When you hold a plastic card near a POS terminal, the embedded chip transmits the card number and expiration date. This information, although encrypted at a basic level, is static. If a malicious actor manages to intercept it using skimming devices, they obtain valid and reusable data.
Conversely, when you use a mobile device, the software infrastructure intervenes even before the NFC antenna activates, creating an isolated and protected environment (called a Secure Element ) that manages authorization dynamically.
The Limitation of the Physical Card: The Simple Tap
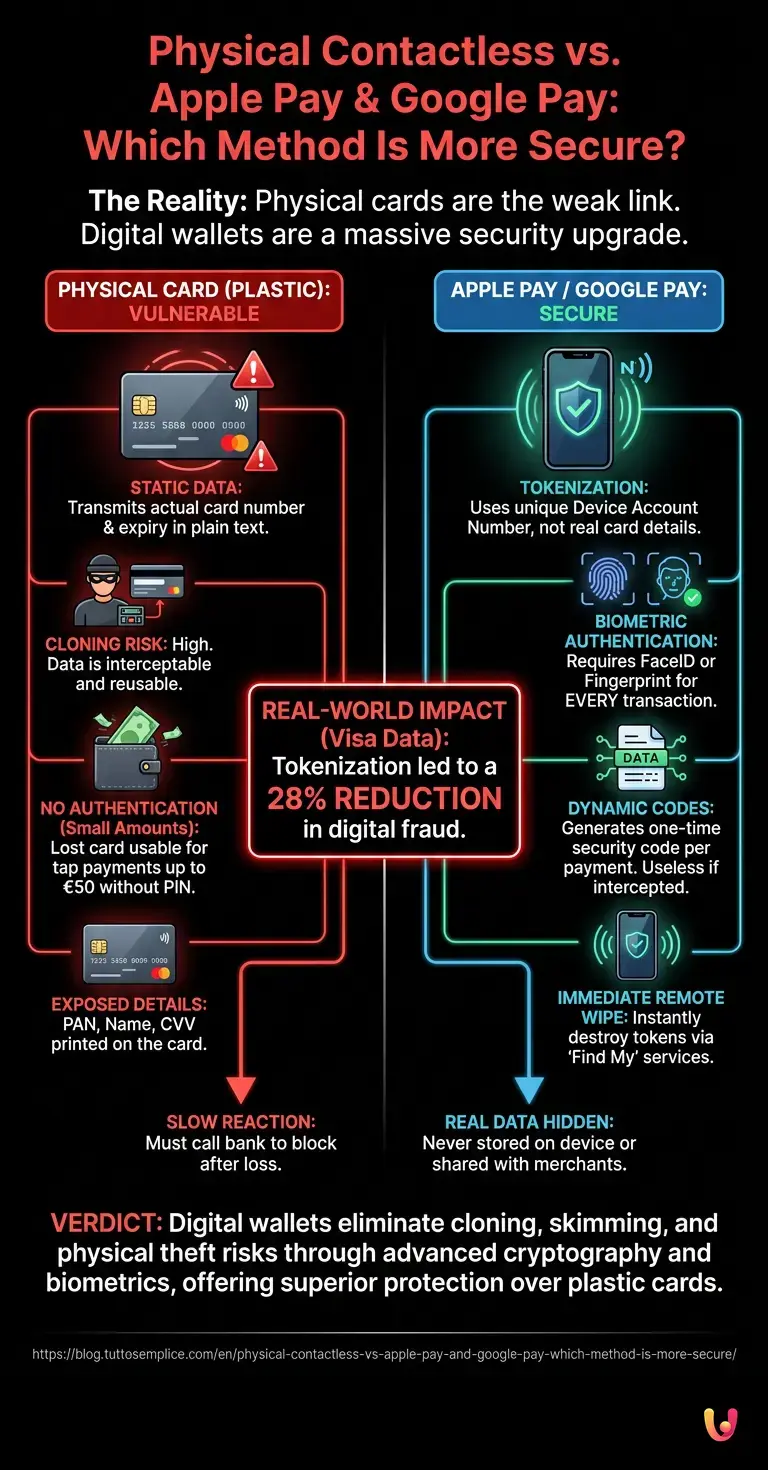
The security of contactless payments using physical cards is severely limited by the absence of authentication for small amounts. A malicious actor with a portable POS terminal or a stolen card can carry out fraudulent transactions before the cardholder is able to block the account .
The main problem with plastic cards is their passive nature. If you lose your wallet, anyone who finds it can go to a store and start making payments below the €50 threshold (the standard limit in Europe for PIN-free transactions). This mechanism, designed for convenience, turns into a critical vulnerability.
- No identity verification: The POS terminal does not know whether the person “tapping” the card is the legitimate owner.
- Exposed data: The name, card number (PAN), and CVV are physically printed on the piece of plastic, ready to be copied and used online.
- Slow reaction times: In the event of loss, the time that elapses between the loss and blocking the card via the banking app is the window during which fraud occurs.
Tokenization: The Shield of Apple Pay and Google Pay

The core of contactless payment security on smartphones is tokenization. According to official documentation from Visa and Mastercard, the actual card number is never stored on the device nor shared with the merchant during a purchase.
When you add your card to Apple Pay or Google Pay , the system does not save your credit card number. Instead, it contacts your bank and generates a Device Account Number (a unique token) that is encrypted and securely stored on your device’s chip.
During a payment, the smartphone transmits this token to the POS terminal, along with a dynamic security code valid for a single transaction. Even if a hacker were to intercept the NFC signal, they would obtain only a single-use code that has already expired, rendering it completely useless for making future purchases. This process makes cloning technically impossible.
Biometric Authentication: Face ID and Fingerprint
Biometric authentication elevates the security of contactless payments to levels unattainable by plastic cards. By requiring FaceID, TouchID, or a fingerprint for every single transaction, the risk of illicit use in the event of device theft is completely eliminated.
This is the true game changer for mobile payments. While a physical card blindly trusts whoever holds it, a smartphone demands irrefutable proof of identity before activating the NFC antenna.
If your smartphone is stolen, the thief won’t be able to buy even a coffee, because the device will require a scan of your face or fingerprint. Furthermore, using Apple’s “Find My iPhone” or Google’s “Find My Device” services, you can remotely wipe your phone in seconds, destroying payment tokens without having to call the bank to block your physical card (which you can continue to use at home).
Direct Comparison: Plastic vs. Smartphones
When analyzing the security of contactless payments , a direct comparison shows that digital wallets come out on top across the board. From protection against cloning to remote deactivation, smartphones offer safeguards that physical cards lack.
To make the structural differences between the two methods even clearer, we have summarized the security parameters in this comparative table:
| Safety Feature | Physical Card (Plastic) | Apple Pay / Google Pay |
|---|---|---|
| Cloning Risk (Skimming) | High (Static data transmitted in cleartext) | None (Use of dynamic single-use tokens) |
| Use in case of theft/loss | Available (Up to €50 without PIN) | Not possible (Requires biometric unlock) |
| Data visible to third parties | Yes (PAN, Expiry Date, and CVV printed) | No (Real data hidden in the app) |
| Emergency shutdown | Requires access to the banking app or a phone call. | Immediate remote device wipe |
In Brief (TL;DR)
Contrary to the widespread myth, the traditional plastic card currently represents the weak link in the security of everyday contactless payments.
Digital wallets such as Apple Pay and Google Pay use tokenization to generate one-time codes, making data cloning technically impossible.
Biometric authentication via fingerprint or facial recognition enhances security, ensuring that every single payment is authorized by the legitimate owner.
Conclusions

In short, contactless payment security reaches its peak with the use of Apple Pay and Google Pay. Moving away from physical cards in favor of digital wallets is the smartest choice for protecting your daily finances.
The convenience of having everything on your smartphone is not a compromise on security, but an enhancement of it. The combination of tokenization (which masks your actual data) and biometric authentication (which ensures that only you can spend your money) creates an impregnable digital fortress. The next time you leave the house, leave your plastic card safely in a drawer and rely on your smartphone: it is the most secure financial decision you can make today.
Frequently Asked Questions

Smartphone payments utilize tokenization technology and never share your actual account details with the merchant. Furthermore, they always require biometric authentication, such as facial recognition or a fingerprint, to authorize the transaction. This system nips any fraud attempt in the bud in the event of device theft.
Your funds remain completely secure because no unauthorized person can make purchases without your fingerprint or facial scan. You can also use location services to remotely wipe your device in a matter of moments, permanently deleting all payment methods saved on it.
Digital wallets generate a dynamic, one-time code for every single transaction, making account cloning technically impossible. If a fraudster manages to intercept the signal from the terminal, they obtain only data that has already expired. This renders the stolen information completely useless for making unauthorized purchases in the future.
Unlike plastic cards, which allow purchases of up to fifty euros without any identity verification, mobile payments have no pre-set limits tied to the absence of a PIN. In fact, every single transaction is authorized in advance using biometrics. This ensures maximum security, regardless of the amount you decide to spend.
Tokenization is an advanced cryptographic process that replaces your actual account number with a unique identifier generated specifically for your device. This invisible shield ensures that your sensitive data is never stored on your phone. Consequently, your financial information is never revealed to the merchant while you are shopping.
Still have doubts about Physical Contactless vs. Apple Pay and Google Pay: Which Method Is More Secure??
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading

- Tokenization (data security) and its application in payment systems – Wikipedia
- Payment Services (PSD2) and Strong Customer Authentication (SCA) – European Commission
- Contactless payment technologies, protocols, and security – Wikipedia
- Near-field communication (NFC) and Secure Element (SE) – Wikipedia





Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.