The belief that incognito browsing makes you invisible online is, in no uncertain terms, the biggest computer illusion of our decade. Many users believe they can browse in complete anonymity simply by opening a dark window on their browser, but the reality is brutally different: this function exclusively protects you from people who share your same physical computer, not from the Internet. If you think that your employer, your network provider, or the web giants are not tracking your every single click, you are making a serious misjudgment that puts your daily privacy at risk .
Select your connection method to find out in real time who has access to your browsing data.
Real-World Case Study: The Class Action Lawsuit Against Google (Brown v. Google LLC)
In 2020, Google was sued for $5 billion on the grounds that it illegally tracked users who used Chrome’s incognito mode. In April 2024, to settle the case, Google agreed to destroy billions of improperly collected data records and update its privacy notices, clearly demonstrating that private browsing did not prevent tech giants from collecting information about users’ habits.
How Private Mode Really Works
Incognito browsing is a browser feature that prevents the local saving of history, cookies, and form data on your device. However, it does not encrypt internet traffic or hide your IP address from external servers or the local network.
To fully understand the mechanism, we need to separate what happens on your device from what happens on the network. When you activate a private session, the browser creates a temporary and isolated environment. According to the official documentation of Google Chrome and Mozilla Firefox, the following are deleted at the end of the session:
- Browsing history: The sites you visit will not appear in the history menu.
- Cookies and site data: Temporary files that keep logins active or track the shopping cart are deleted when the window is closed.
- Information entered in forms: Passwords, usernames, and addresses you type are not stored for future autofill.
This means that the function is perfect for buying a surprise gift for your partner using a shared computer, or for accessing a second email account without logging out of the first. Its range is limited to your computer screen .
Who Can Track Your Online Activity?
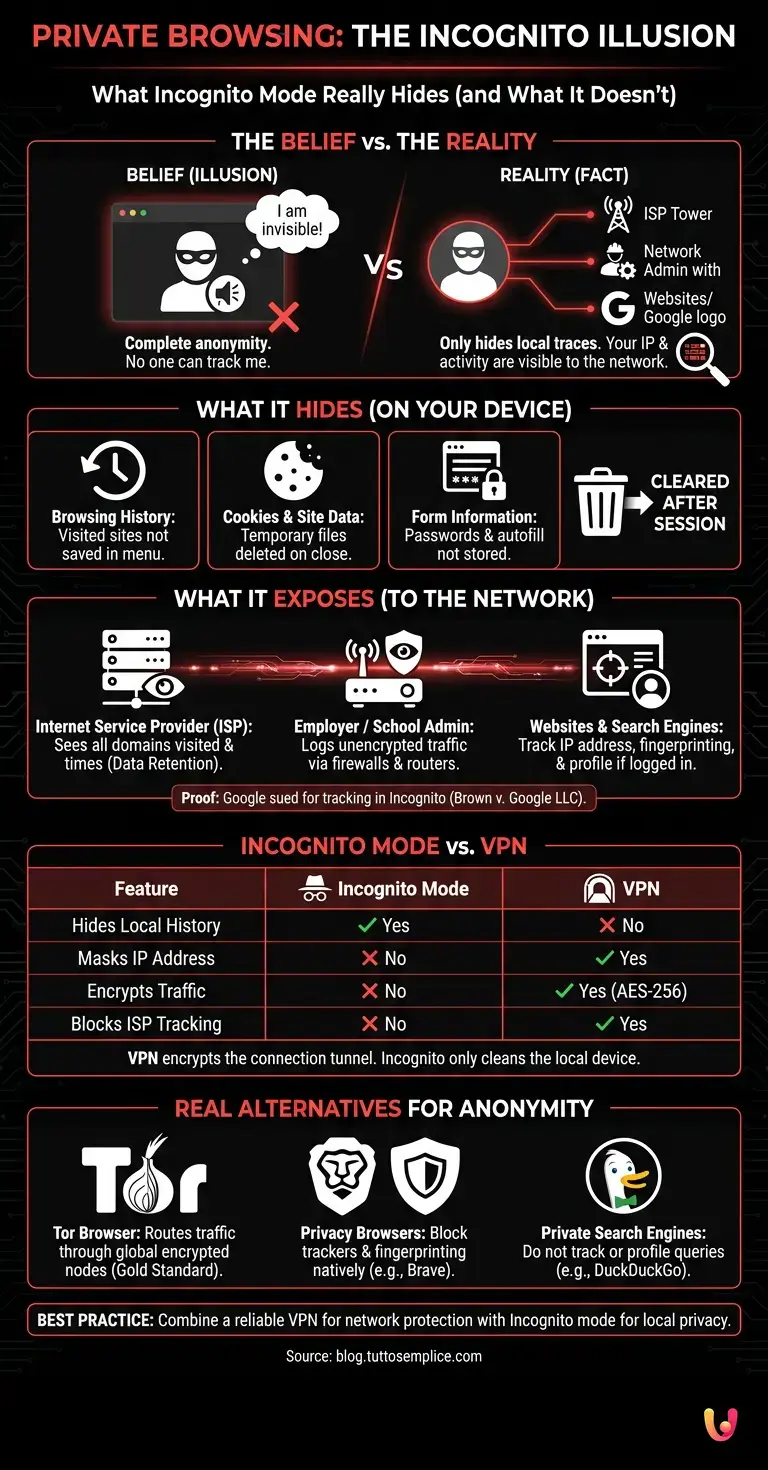
Even when using incognito browsing , your activity remains perfectly visible to your Internet Service Provider (ISP), your corporate or school network administrator, and the websites you visit directly through your IP address.
The myth of invisibility collapses the moment your data leaves your device. Here’s who continues to monitor your digital habits without any restrictions:
- Your Internet Service Provider (ISP): Companies like TIM, Vodafone, or Fastweb see exactly which domains you are visiting and when. The law requires them to keep these logs (Data Retention) for national security reasons.
- Your Employer or School: If you are connected to your office Wi-Fi or using a company device, network firewalls and routers log all unencrypted traffic. The dark browser window does not bypass the network infrastructure.
- Websites and Search Engines: If you log in to Facebook or Google during a private session, your activity is immediately associated with your profile. In addition, your public IP address remains exposed, allowing for geolocation and browser fingerprinting.
Crucial Differences Between Private Browsing and VPN
Unlike incognito browsing , which only works locally, a VPN creates an encrypted tunnel for your data and masks your IP address, offering real protection against network tracking and data interception.
The confusion between these two tools is the main cause of personal privacy violations. While the private browser is a simple “local trace cleaner”, the Virtual Private Network (VPN) intervenes on the infrastructure of your connection.
| Feature | Incognito Mode | VPN Connection |
|---|---|---|
| Hides the history on the PC | Yes | No (you need to use both) |
| Hides the IP Address | No | Yes |
| Encrypts data traffic | No | Yes (AES-256 encryption) |
| Block ISP tracking | No | Yes |
| Bypass geo-blocks | No | Yes |
To achieve the highest level of daily security, the best practice is to combine both tools : activate a reliable VPN to protect data in transit and use the private window to avoid leaving physical traces on the hard drive.
Real Alternatives for Anonymity on the Internet
To overcome the limitations of incognito browsing , you need to use advanced tools such as the Tor browser, which bounces traffic across global nodes, or privacy-oriented browsers like Brave combined with search engines that do not track users.
If your goal is true anonymity or ironclad privacy, you need to abandon traditional commercial browsers. The market offers solutions designed specifically to counter surveillance capitalism:
- Tor Browser: This is the gold standard for anonymity. It routes your connection through three encrypted servers scattered around the world (nodes), making it almost impossible to trace back to your original IP address. It is essential for journalists and activists, although it significantly slows down the connection speed.
- Privacy-First Browsers (Brave, Mullvad Browser): These browsers natively block trackers, fingerprinting scripts, and invasive advertising. They do not send telemetry data to large corporations and offer a higher level of website isolation.
- Alternative search engines: Replacing Google with DuckDuckGo or Startpage ensures that your search queries are not saved, profiled, or sold to advertisers.
Conclusions

Incognito browsing is a useful but deeply misunderstood tool. It is essential to consider it for what it is: a convenience feature to keep your local device clean, not a magic shield against digital surveillance. In the age of hyper-connectivity, protecting your data requires a proactive approach. Understanding the limitations of the tools we use daily is the first, indispensable step to regaining control of your digital identity. If you want true privacy, invest in a quality VPN, adopt security-focused browsers, and browse with the awareness that, on the Internet, nothing is invisible by default.
Frequently Asked Questions

Private mode only deletes local data from your device at the end of the session. This means that the history of visited sites, cookies, and information entered in forms will not be saved on the computer or smartphone you are using. It does not offer any protection against external tracking by network providers or websites.
Even when this feature is enabled, your online activity remains visible to various external parties. The administrator of the corporate or school network, your internet service provider, and the websites themselves can monitor your traffic. To hide this information from third parties, it is necessary to use additional tools that encrypt the connection.
Incognito browsing only works locally, clearing your device of the physical traces of your web activity. A virtual private network, on the other hand, intervenes on the connection parameters by creating an encrypted tunnel for data and masking your public IP address. Combining both tools is the best solution to protect both local and network privacy.
To achieve true digital anonymity, you need to abandon traditional commercial browsers and rely on advanced privacy-focused solutions. The highest standard is represented by the Tor browser, which bounces traffic across encrypted global servers. Alternatively, you can use secure browsers combined with search engines that do not profile user searches.
When you connect to your office’s wireless network or use a company computer, all traffic passes through the facility’s routers and security systems. These network devices log requests in plain text regardless of your browser settings. The dark web has no power to bypass the monitoring systems of that specific network to which you are connected.
Still have doubts about Private Browsing: What Incognito Mode Really Hides (and What It Doesn’t)?
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading








Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.