Quantum Computing is no longer just a theoretical concept confined to experimental physics laboratories, but a rapidly evolving technological reality that is redefining the boundaries of global computing. By 2026, the power of quantum processors has reached critical thresholds, raising a fundamental question: are our bank passwords, our savings, and our financial data still safe? The answer lies in the complex architecture of the mathematical algorithms that protect the modern web and in the race against time to update them before the so-called “Q-Day,” the day when quantum computers become cryptographically relevant (CRQC).
Introduction to the Quantum Threat
The intersection of quantum computing and cryptography represents one of the most pressing computing challenges of our decade. Quantum computers possess such computing power that they can break the security systems that currently protect our bank passwords and financial transactions.
Unlike classical computers, which process information in bits (0 or 1), quantum computers use qubits . Thanks to the principles of quantum mechanics, such as superposition and entanglement, a quantum computer can analyze an incalculable number of combinations simultaneously. According to industry data and reports from major cybersecurity intelligence agencies, this architecture not only speeds up existing processes but also solves specific classes of mathematical problems in fractions of a second—problems that a traditional supercomputer would take millennia to decipher. It is precisely on these “intractable” mathematical problems that the entire security of today’s banking system is based.
How Current Banking Encryption Works
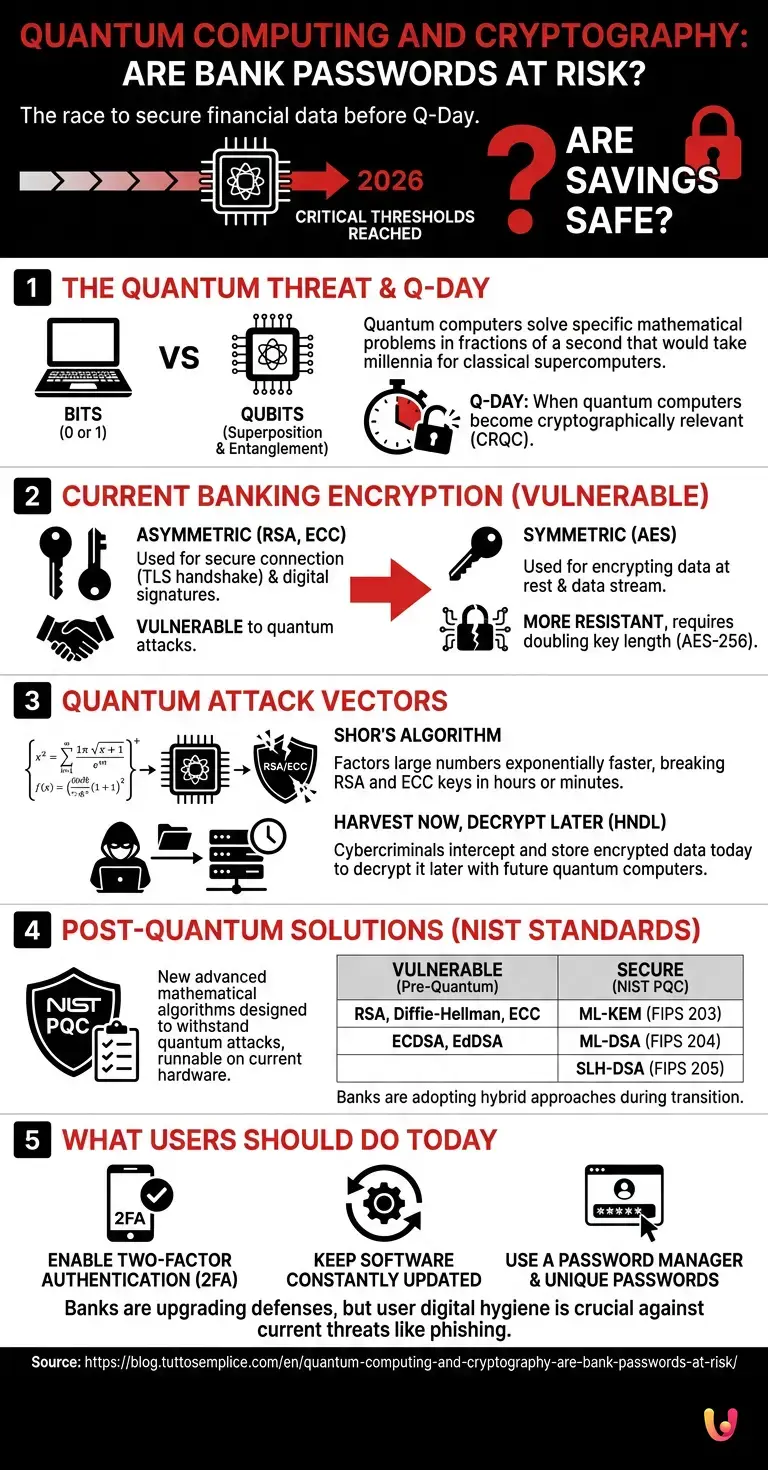
To understand the link between quantum computing and cryptography, it is essential to analyze how banks protect data today. Financial institutions use a mix of symmetric and asymmetric encryption to ensure that passwords and transactions remain unreadable to hackers.
When we access our home banking, our browser and the bank’s server establish a secure communication channel using the TLS (Transport Layer Security) protocol. This process, known as a handshake , relies on two main families of cryptographic algorithms, each with a specific purpose and a different degree of vulnerability to the quantum threat.
Asymmetric Algorithms RSA and ECC
The RSA and ECC algorithms are at the heart of web security, but in the context of quantum computing, they are extremely vulnerable. They are based on complex mathematical problems, such as the factorization of prime numbers, which quantum systems can solve instantly.
Asymmetric (or public-key) cryptography uses two keys: a public key to encrypt data and a private key to decrypt it. The RSA (Rivest-Shamir-Adleman) algorithm bases its security on the extreme difficulty of factoring the product of two enormous prime numbers. The ECC (Elliptic Curve Cryptography) algorithm, widely used today for its efficiency, is instead based on the discrete logarithm problem on elliptic curves. Both of these systems are the pillars that protect the initial exchange of session keys and the digital signatures of banking transactions. Unfortunately, they are precisely the main targets of future quantum attacks.
AES Symmetric Encryption
Unlike asymmetric systems, the AES algorithm is more resistant to threats related to quantum computing cryptography. Used to encrypt data at rest in banking servers, it only requires a doubling of the key length to maintain an unassailable level of security.
Once the secure connection is established, banks use symmetric encryption , such as the Advanced Encryption Standard ( AES ), to encrypt the actual data stream (including the transmission of the password). Grover’s quantum algorithm can theoretically halve the strength of an AES key, but according to official NIST documentation, moving from AES-128 keys to AES-256 keys is sufficient to completely neutralize the quantum threat on this front.
The Impact of Quantum Computing on Cryptography
The real impact of quantum computing on cryptography is its ability to decrypt secure communications in record time. This technological revolution renders standard security protocols obsolete, forcing the banking sector to immediately transition to new and more robust defensive architectures.
The central problem does not lie in the hardware itself, but in the quantum algorithms that this hardware is capable of executing. The scientific community has identified specific threats that make the current public key infrastructure (PKI) fundamentally insecure in the long term.
Shor’s Algorithm and the Collapse of RSA
Shor’s algorithm is the main reason why the combination of quantum computing and cryptography is alarming. This quantum algorithm can factor large numbers exponentially faster than classical computers, effectively destroying the reliability of the current RSA standard.
Developed by mathematician Peter Shor in 1994, this algorithm demonstrates that a sufficiently powerful and stable (error-corrected) quantum computer can solve both the integer factorization problem and the discrete logarithm problem in polynomial time. In practical terms, this means that an RSA-2048 key, which would take billions of years to crack with a traditional computer, could be deciphered in a few hours or minutes by a mature quantum computer. When this happens, any bank password intercepted during the asymmetric handshake phase will be exposed in plain text.
The Harvest Now, Decrypt Later Threat
A current danger in the quantum computing landscape is the Harvest Now, Decrypt Later strategy. Cybercriminals intercept and store encrypted banking data today, waiting to have a quantum computer available to decode it in the near future.
You don’t have to wait for “Q-Day” to suffer the damage of the quantum revolution. Malicious actors (often linked to nation-states) are already implementing the HNDL (Harvest Now, Decrypt Later) strategy. They record huge volumes of encrypted internet traffic, including bank logins and financial databases , storing them in vast data centers. Even if they cannot read this data today, their goal is to preserve it until they have the quantum technology needed to retroactively decrypt it. This makes migrating to new standards an immediate urgency, not a problem for the future.
Post-Quantum Solutions and Standards (NIST)
To counter the vulnerabilities that have emerged from quantum computing cryptography, NIST has formalized new post-quantum cryptographic standards. These advanced mathematical algorithms are designed to withstand attacks from quantum computers, ensuring the future long-term security of global banking systems.
In response to this existential threat, the U.S. National Institute of Standards and Technology (NIST) initiated a lengthy selection process to identify quantum-resistant algorithms. The final standards for Post-Quantum Cryptography (PQC) have already been published, with large-scale implementations underway in 2026.
These new algorithms do not require quantum hardware to work; they are complex mathematical algorithms that can be run on our current computers and smartphones , but are structured to withstand Shor’s algorithm.
| Pre-Quantum Standard (Vulnerable) | New NIST PQC Standards (Secure) | Main Function |
|---|---|---|
| RSA, Diffie-Hellman, ECC | ML-KEM (FIPS 203) formerly Kyber | Key Encapsulation |
| RSA, ECDSA | ML-DSA (FIPS 204) formerly Dilithium | Digital Signatures (Authentication) |
| EdDSA | SLH-DSA (FIPS 205) formerly SPHINCS+ | Digital Signatures (Hash-Based) |
Major global banks are currently adopting a hybrid approach, combining classical algorithms (such as ECC) with post-quantum algorithms (such as ML-KEM) to ensure maximum security during the transition period.
What Users Should Do Today
Despite concerns about quantum computing and cryptography, banking users should not panic. Banks are already implementing the necessary defenses, but it is crucial to adopt strict digital hygiene practices to protect your login credentials.
While financial institutions and tech giants work behind the scenes to upgrade the global cryptographic infrastructure, the responsibility for basic security still falls on the user. Bank passwords are far more at risk from traditional phishing attacks today, rather than quantum attacks tomorrow. Here are the fundamental actions to take:
- Enable Two-Factor Authentication (2FA) : Use authentication apps (such as Google Authenticator or Microsoft Authenticator) or hardware tokens. Even if a password were to be cracked in the future, the dynamic second factor would block access.
- Keep software constantly updated: Web browsers, operating systems, and banking apps will progressively include support for PQC (Post-Quantum Cryptography) standards through regular software updates.
- Use a password manager: Create long, complex, and unique passwords for each financial service.
- Monitor your bank’s communications: The most advanced credit institutions are already notifying customers of the switch to quantum-resistant encryption protocols.
In Brief (TL;DR)
The evolution of quantum computing seriously threatens the security of today’s banking systems, putting our passwords and financial data at risk.
Asymmetric algorithms such as RSA and ECC are extremely vulnerable, while AES symmetric encryption only requires longer keys to resist.
The advent of quantum computers renders standard protocols obsolete, forcing the financial sector to rapidly transition to new cryptographic defense architectures.
Conclusions

In summary, the evolution of quantum computing cryptography marks the end of an era for traditional cybersecurity. While current banking passwords face theoretical risks, the timely adoption of post-quantum standards will ensure the resilience of the global financial system for years to come.
The quantum threat is real, and the “Harvest Now, Decrypt Later” strategy demonstrates that the time to act is now. However, thanks to the joint efforts of NIST, cryptographic researchers, and the banking industry, the transition to Post-Quantum Cryptography is already underway. Our banking passwords and financial data will remain secure, provided that the IT industry completes the migration to the new standards before quantum computers reach commercial maturity. In the meantime, maintaining high personal digital hygiene remains the most effective shield against today’s and tomorrow’s cyber threats.
Frequently Asked Questions

Q-Day represents the moment when quantum computers will become powerful enough to break current cybersecurity systems. When this technology reaches commercial maturity, the mathematical algorithms that protect financial transactions today could be deciphered in a matter of minutes. Banks are already working to upgrade their defenses before this scenario materializes.
This criminal strategy consists of stealing and archiving huge amounts of encrypted banking data today, which is currently unreadable. Hackers store this information on their servers, waiting to have a quantum processor available in the future. As soon as the technology allows, they will use the new computing power to retroactively decode old databases and access users’ savings.
Currently, access credentials for financial services are protected by very robust cryptographic systems against traditional attacks. However, future quantum processors will exploit specific algorithms capable of breaking current asymmetric security keys in record time. For this reason, credit institutions are progressively adopting new advanced mathematical standards to ensure long-term protection.
These are new mathematical security protocols designed specifically to withstand the computing power of future supercomputers. These advanced algorithms do not require special hardware and can be run on our regular smartphones or computers via simple software updates. Their global implementation will neutralize next-generation cyber threats and keep web communications secure.
The main defense consists of maintaining strict digital hygiene by always enabling two-step verification for every financial service. It is also essential to constantly update the operating system and banking applications to receive new post-quantum security protocols. Finally, it is advisable to use a credential manager to create long and complex access codes for each individual platform.
Still have doubts about Quantum Computing and Cryptography: Are Bank Passwords at Risk??
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading





Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.