When we sit in front of our computer screen or grab our smartphone to access our bank account, we perform a series of actions that we consider trivial and purely mechanical. We enter a username, type a password, and perhaps confirm access via an SMS code or a fingerprint. Yet, in those few seconds, we have already told a computer system who we are, long before pressing the enter key. The secret of this invisible identification lies in Behavioral Biometrics , a fascinating and complex field that analyzes our involuntary movements to establish our identity with almost absolute precision.
For decades, account security has been based on a very simple paradigm: prove who you are through something you know (a password) or something you own (a token or a smartphone). However, in today’s cybersecurity landscape, this approach is no longer sufficient. Passwords are stolen, codes are intercepted, and devices are cloned. The true frontier of digital protection no longer focuses on what you enter into the login form, but on how you enter it.
The Password Illusion and the New Paradigm
Imagine the scene: a cybercriminal has managed to obtain your banking credentials on the dark web. They have your username, your complex password, and even a way to bypass two-factor authentication. They sit down at their computer, enter the data, and click “Log in.” The system, however, blocks the transaction. Why? Because the criminal doesn’t move the mouse like you do. They don’t type on the keyboard with your same rhythm. They don’t hesitate in the same milliseconds that you do.
Modern cybersecurity has come to understand that humans are creatures of deeply ingrained neuromotor habits. Every time we interact with a device, we leave an invisible digital signature, a behavioral footprint that is as unique as our DNA or our retina. This signature is composed of hundreds of micro-movements of which we are not even remotely aware.
How does the reading of our invisible gestures work?
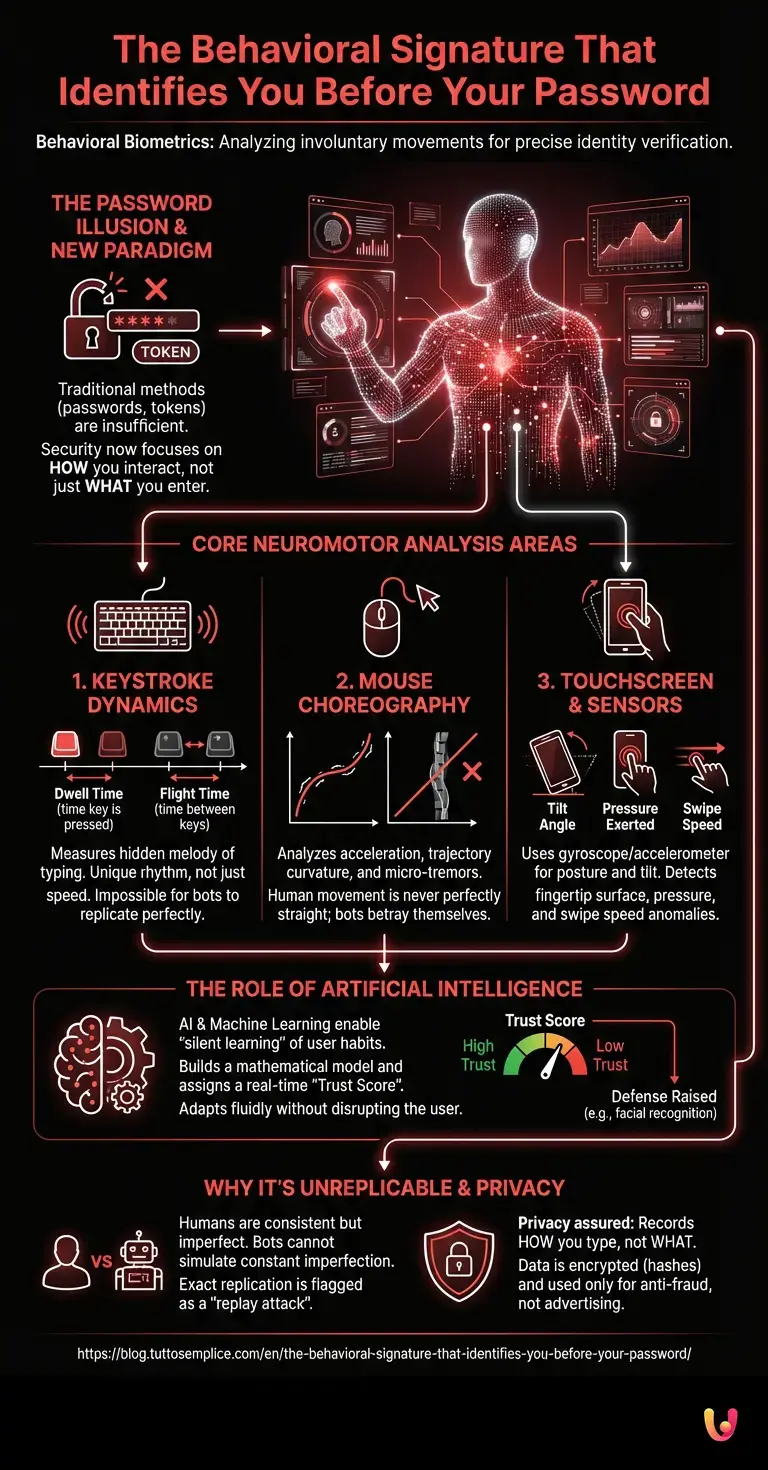
To understand how technology can trace this profile, we need to analyze the parameters that modern security systems record in the background. The process is mainly divided into three large areas of neuromotor analysis.
1. Keystroke Dynamics
It’s not about how fast you type, but about the hidden melody in your typing. The systems measure two crucial factors: Dwell Time (the exact time a key remains pressed before being released) and Flight Time (the time between releasing one key and pressing the next). You might have a habit of holding the letter “A” for 90 milliseconds and taking 120 milliseconds to reach the letter “C”. A scammer, or an automated bot, will have completely different timings, impossible to replicate voluntarily.
2. The choreography of the mouse
If you use a desktop computer or a laptop, the way you move your cursor is an open book. Behavioral biometrics software analyzes initial acceleration, trajectory curvature, micro-tremors of the hand when the cursor stops on a button, and even the tendency to slightly overshoot the target and then correct the aim. A human never moves the mouse in a perfectly straight line; malicious software programmed to simulate a click, on the other hand, tends to do so, immediately betraying its artificial nature.
3. Interaction with the touchscreen and sensors
On mobile devices, the analysis becomes even more in-depth. When you hold your smartphone, the internal sensors (gyroscope and accelerometer) record the device’s tilt angle. The touchscreen detects the fingertip surface used, the pressure exerted, and the swipe speed. If you are used to holding the phone with your left hand and swiping with your right thumb while applying 40 grams of pressure, a thief holding your unlocked phone with their right hand will generate an immediate anomaly, causing the system to request further identity verification.
The Role of Artificial Intelligence

All this raw data, on its own, would be meaningless. This is where digital innovation driven by Artificial Intelligence and Machine Learning comes into play. When you create an account or start using a banking application, the algorithm begins a “silent learning” phase. It collects thousands of data points during your normal usage sessions, building a mathematical model of your standard behavior.
Once this baseline is established, the AI assigns a trust score to each of your future interactions. If the score drops below a certain threshold—for example, because you are typing in an unusually rigid manner or moving your mouse in jerky trajectories—the system doesn’t necessarily block you instantly, but it raises its defenses. It might ask for additional facial recognition or temporarily prevent large money transfers. It’s a fluid security system that adapts in real-time without disrupting the legitimate user’s experience.
Why can’t cybercriminals replicate it?
The question arises spontaneously: if a hacker knows that the system controls mouse movement, can’t they simply program malware to imitate it? The short answer is no, and this is where the true genius of this technology lies.
Replicating a password is a binary operation: it’s either right or wrong. Replicating human behavior requires simulating imperfection. Even if a criminal managed to record your exact typing dynamics during one session, reproducing them identically in the next session would be flagged as an anomaly. We humans are consistent in our habits, but we are not machines: we never perform the same movement twice with millisecond precision. If the system detects a 100% exact replication of a previous login, it immediately understands that it is a “replay” attack, orchestrated by software.
The startups that are leading the revolution
This sector is no longer science fiction, but a consolidated and rapidly expanding reality. Several startups founded in recent years have specialized exclusively in providing behavioral biometrics APIs for large financial institutions, e-commerce platforms, and government agencies. These companies work behind the scenes: the end-user never sees their logo, but their code is integrated into the apps we use every day.
The goal of these emerging technologies is to create an ecosystem where continuous authentication completely replaces the concept of a one-time login. You will no longer be authenticated only when you enter your password, but you will remain authenticated as long as your behavior matches your profile. If you walk away from your computer and a malicious colleague tries to send an email from your account, the simple way they grab the mouse and type on the keyboard will lock the screen in a fraction of a second.
Privacy and surveillance: what happens to our data?
Of course, the idea of software recording our every micro-movement raises legitimate privacy concerns. Are we perhaps handing over the keys to our nervous system to big tech corporations?
Industry experts provide reassurance on one fundamental point: behavioral biometrics systems do not record what you are typing, but only how you are typing it. The data collected is immediately transformed into cryptographic strings (hashes) and mathematical models. The system does not know that you typed the word “Secret123”; it only knows that it took you 400 milliseconds to go from the first to the eighth character. Furthermore, international data protection regulations stipulate that these behavioral profiles cannot be shared between different companies for advertising profiling purposes, but must remain confined within the anti-fraud security perimeter.
In Brief (TL;DR)
Beyond traditional passwords, modern cybersecurity leverages behavioral biometrics to identify users through their invisible neuromotor habits.
The technology creates an inimitable signature by analyzing involuntary movements such as typing rhythm, mouse trajectories, and touchscreen pressure.
Artificial intelligence algorithms process this data to build a behavioral profile and assign a trust score, blocking suspicious access.
Conclusions

The shift from knowledge-based authentication to behavior-based authentication represents one of the most important evolutionary leaps in the history of digital security. A password, no matter how complex, remains an external artifact, something that can be lost, forgotten, or stolen. Our involuntary movements, on the other hand, are the very essence of our physicality translated into the digital world.
The next time you log into your bank account or unlock your smartphone, pause for a moment and reflect. Even before you finish typing, even before the system welcomes you, your muscles, your nerves, and your unconscious habits have already vouched for you. In a world where data can be falsified and identities cloned, our imperfect humanity, with its tremors and hesitations, has paradoxically become the most impenetrable shield we possess.
Frequently Asked Questions

Behavioral biometrics is an advanced security technology that analyzes users’ involuntary movements to verify their identity. Instead of relying on codes or fingerprints, the system studies unique habits such as typing speed, mouse trajectories, and screen pressure. This approach creates a neuromotor profile that is impossible to fake, ensuring a superior level of protection against digital fraud.
Modern security systems measure typing dynamics by calculating the pressure time of each key and the pause between one letter and the next. This typing melody is strictly personal and varies from individual to individual based on established neuromotor patterns. Malicious software or a scammer would have completely different timings, immediately triggering the system’s security blocks.
Replicating human behavior requires simulating constant imperfections that automated bots cannot reproduce. We humans are consistent in our habits, but we never perform the same movement twice with millimeter precision. If a system detects an exact copy of a previous login, it immediately understands that it is facing a cyberattack and blocks the transaction.
These protection systems do not record the content of what you write, but exclusively analyze the way you interact with devices. The information collected is immediately transformed into mathematical models and cryptographic strings to ensure maximum confidentiality. International regulations strictly prohibit the sharing of these profiles for advertising purposes, limiting their use to the prevention of computer fraud only.
Mobile devices use internal sensors such as the gyroscope to record the owner’s usual posture and phone tilt. The touchscreen also detects the fingertip surface used, the pressure exerted, and the speed of finger scrolling. Any anomaly compared to the standard profile generates a decrease in the trust score, leading the system to request additional identity checks.
Still have doubts about The behavioral signature that identifies you before your password.?
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading







Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.