Imagine the following scene: you are in a crowded train station during rush hour. You are wearing dark sunglasses, a protective mask covering half your face, and a cap pulled low over your forehead. You are convinced you are just an anonymous silhouette in a sea of people. However, a security system has already recognized you, matched your profile, and knows exactly who you are, in less than a second. How is this possible without a clear face scan? The answer to this fascinating curiosity lies in behavioral biometric recognition, the main entity completely redefining how we interact with physical space in the digital age.
For decades, identification relied on static traits: fingerprints, iris scans, or facial recognition. But with the exponential advance of technology, the paradigm has changed. Your identity is no longer a simple “portrait,” but a dynamic puzzle, a fragmented identity composed of thousands of subtle variables you emit unconsciously every second. In this article, we will explore in depth the technical mechanisms that make this instant identification possible and decode the secret behind systems that “see” you even when you hide.
Beyond Facial Recognition: Why Your Face Is No Longer Necessary
Traditional security systems relied almost exclusively on face mapping. They measured the distance between eyes, nose width, and jawline contour. However, these systems had a major vulnerability: they could be fooled by blind spots, poor lighting, or physical obstructions (masks, scarves). This is where a new generation of artificial intelligence steps in, capable of looking beyond the obvious.
Instead of looking for a perfect face match, new AI systems analyze the human body as a biomechanical whole. This approach is called Person Re-identification (ReID) and relies on the ability to recognize a person across several different surveillance cameras, without seeing their face. The system extracts “soft-biometric signatures”: estimated height, body shape, clothing color palette, type of backpack worn, and, most importantly, how the person moves.
The Movement Signature: How Gait Recognition Works
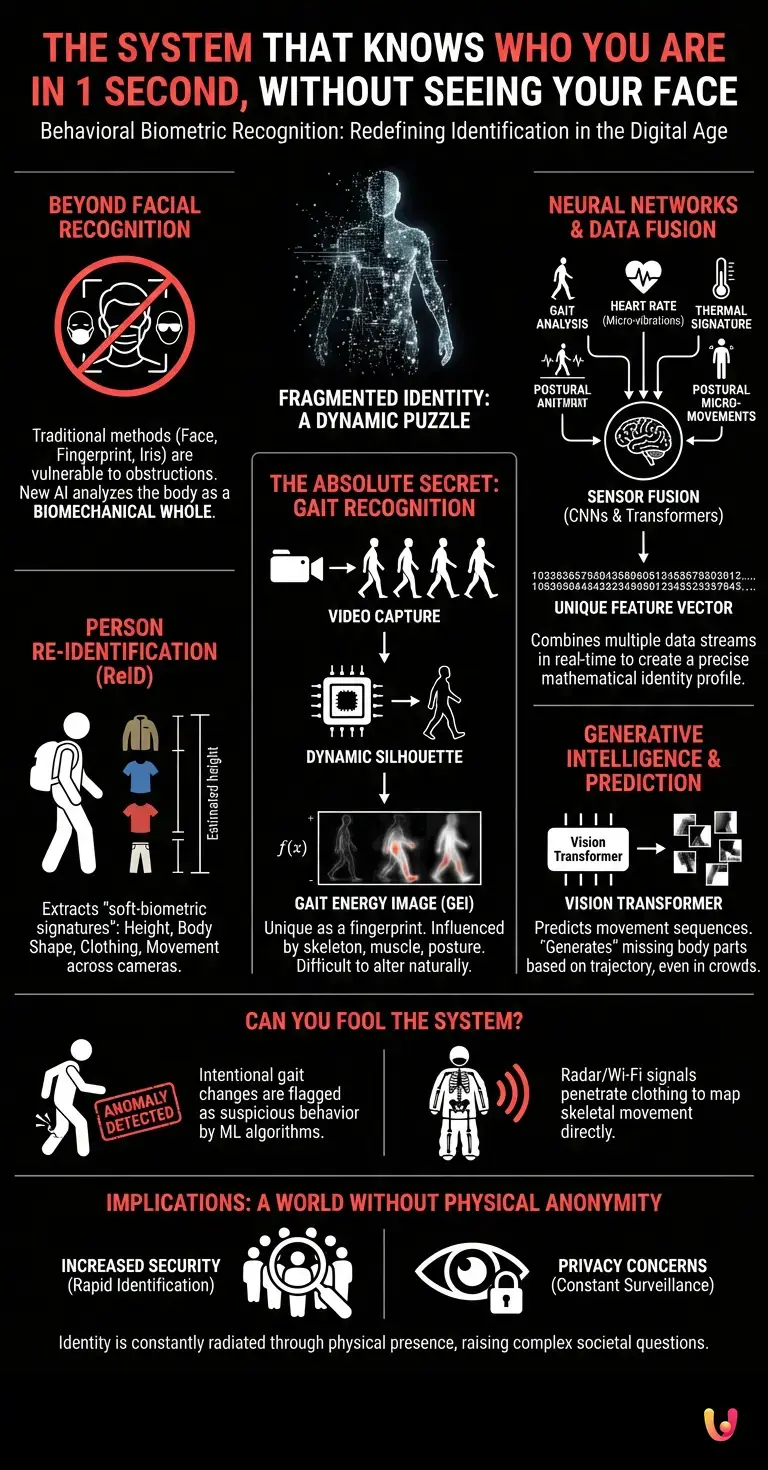
The absolute secret of faceless identification is Gait Recognition. The way you walk is as unique as your fingerprint. It is a complex biomechanical process, influenced by your bone length, muscle density, spinal posture, and even minor medical conditions or how you distribute your weight.
How exactly does it work? Video cameras capture a sequence of frames of you walking. Advanced machine learning models process these frames to extract a “dynamic silhouette.” Algorithms eliminate the background and focus exclusively on the outline of your body in motion. Then, they transform this movement into a mathematical representation called a Gait Energy Image (GEI) – a single image that condenses a complete step cycle, highlighting body areas with the greatest range of motion (such as arm swing or leg extension).
This energy image is then compared against a massive database. Because your gait is dictated by your skeletal structure, it is extremely difficult, if not impossible, to intentionally alter it for a long period without appearing completely unnatural.
Neural Networks and Data Fusion: The Puzzle of Your Identity
To process these huge amounts of visual data in real time, modern systems use convolutional neural networks (CNNs) and Transformer-type architectures. These networks are trained via deep learning on millions of hours of video footage, learning to distinguish patterns the human eye could never notice.
But the real magic happens through the process of Sensor Fusion. Your fragmented identity is recomposed by combining multiple data streams. Neural networks don’t just analyze gait. They simultaneously integrate heart rate (measured remotely via micro-vibrations of the head or neck, using video photoplethysmography), body thermal signature, and postural micro-movements. These algorithms create a “feature vector” – a long string of numbers that uniquely represents you in the system’s mathematical space. When your current vector matches a previously recorded vector by 99%, the system has identified you.
The Role of New Technologies: From Predictive Algorithms to Generative Intelligence
The field of surveillance and identification has recently been revolutionized by the same principles underlying language models. To understand this leap, we must draw a parallel. An LLM (Large Language Model) like ChatGPT works by analyzing sequences of words and predicting, based on context, the most logical word that follows. Similarly, new generative intelligence models applied in computer vision analyze sequences of movement.
Unlike a text model, a “Vision Transformer” divides your image into dozens of fragments (patches) and analyzes the spatiotemporal relationship between them. If an arm moves at a certain angle at second 1, the generative model can predict exactly where your leg will be at second 2. This predictive capability allows the AI system to recognize you even when you are partially hidden by other people in a crowd. The system mentally “generates” the missing parts of your body based on your trajectory and unique biomechanics, completing the puzzle of your fragmented identity.
What Happens If You Try to Fool the System?
A natural question anyone might ask is: “What happens if I intentionally change my walk, put a stone in my shoe, or wear extremely baggy clothes?”
In the early stages of the technology, these tactics might have worked. Today, however, the level of automation and sophistication has reached staggering heights. When you try to limp intentionally, you introduce an anomaly into your biomechanics. Machine learning algorithms are specifically trained to detect these anomalies. They know what a natural walk looks like and what a forced walk looks like. Instead of being fooled, the system will mark your behavior as “suspicious” or “abnormal,” drawing even more attention to you.
Furthermore, baggy clothes are no longer a major obstacle. Modern technologies can use radio waves (like Wi-Fi signals) or millimeter-wave radar sensors to penetrate layers of clothing and directly map your skeletal movement. In this way, your real body shape and joint dynamics are captured with millimeter precision, regardless of how many layers of fabric you are wearing.
The Implications of a World Without Physical Anonymity
This ability to recognize anyone, anywhere, without needing a visible face, brings with it a profound transformation of society. On one hand, the level of security in public spaces increases exponentially. Finding a missing person in a crowded city or identifying a suspect in a fraction of a second becomes a routine, fully automated task.
On the other hand, the technology raises complex questions about privacy. Our identity is no longer something we can choose to reveal or hide; it is constantly radiated through our mere physical presence. Every step we take, every movement of our shoulders, and every heartbeat becomes quantifiable data, processed by silent neural networks watching from the shadows.
In Brief (TL;DR)
Modern security technology goes beyond traditional facial recognition, identifying individuals instantly based on soft-biometric traits and body shape.
The secret to this precise identification is gait analysis, a unique biomechanical process that transforms your movement into a digital signature impossible to forge.
Advanced systems use artificial intelligence to merge multiple data points, such as heart rate and postural micro-movements, perfectly recomposing the puzzle of your identity.
Conclusion

The mystery of instant recognition in a crowd, even with a hidden face, has been completely decoded by modern science. We are no longer defined just by our facial features, but by a complex sum of biomechanical behaviors, thermal signatures, and movement patterns. Through the convergence of gait analysis, sensor fusion, and the predictive power of new artificial intelligence architectures, fragmented identity becomes an infallible identification tool.
Understanding how these technologies work helps us realize that, in the digital age, physical anonymity has become an illusion. Your body tells a unique story every second, and now, for the first time in history, machines have learned to read it fluently.
Frequently Asked Questions

Modern security systems use behavioral biometric recognition to identify you. Instead of analyzing facial features, algorithms examine the human body as a biomechanical whole, analyzing height, body shape, and especially how you move. This advanced technology allows precise identification even when you wear a mask or sunglasses.
Gait recognition is a technology that analyzes your unique way of walking, considered as personal as a fingerprint. Video cameras capture body movement, and machine learning models transform it into a detailed mathematical representation. The system then compares this dynamic silhouette with a database to establish the person’s identity in real time.
If you try to limp or alter your step, AI algorithms will immediately detect an anomaly in your natural biomechanics. The system is trained to clearly differentiate between a natural walk and a forced one, marking your behavior as suspicious. Additionally, radar technologies can penetrate baggy clothes to directly map your skeletal movement.
Sensor fusion simultaneously combines multiple data streams to create an extremely precise identity profile. Neural networks integrate gait analysis with remotely measured heart rate, body thermal signature, and postural micro-movements. All this information generates a unique mathematical vector that makes identification almost infallible.
Computer vision systems use generative models similar to language ones to analyze the spatial and temporal relationship of your body. If you are partially hidden by a crowd, artificial intelligence can anticipate your unique trajectory and biomechanics. Thus, the system mentally completes the missing parts of the body to recognize you without interruptions.
Still have doubts about The System That Knows Who You Are in 1 Second, Without Seeing Your Face?
Type your specific question here to instantly find the official reply from Google.








Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.