If you bought a shielded wallet out of fear that someone might steal your money by brushing against you on the subway with a portable card reader , you have fallen victim to one of the most effective fear-based marketing campaigns of the last decade. The counter-intuitive truth is that the remote cloning of a modern credit card is technically impossible. NFC chips generate a dynamic, one-time cryptogram for every transaction; even if a malicious actor were to intercept the signal, they would obtain a code that is already expired and useless for future purchases. The real risk to your funds does not travel through the air just 4 centimeters from your trousers, but lies in online phishing and the physical theft of the card.
Skimming Risk Simulator
Find out if your card is truly at risk based on NFC physics.
The technical truth about contactless payments and radio signals
To understand the actual need for contactless card protection , it is essential to distinguish between older RFID technology and the current NFC standard. Modern cards employ advanced cryptographic protocols that render remote cloning an urban legend devoid of technical foundation.
According to official documentation from EMVCo (the global consortium that manages standards for Europay, Mastercard, and Visa), contactless payment cards never transmit the cardholder's name, the three-digit CVV code on the back, or the PIN. When a card is held near a reader, the embedded chip generates a dynamic cryptogram . This means that the data exchanged is valid exclusively for that specific transaction.
If a cybercriminal were to use a scanner to intercept radio communications (a practice known as skimming ), they would obtain only a single-use code that has already been invalidated. They would be unable to use that data in any way to clone the card onto a magnetic medium or to make online purchases, as online payment gateways strictly require the CVV, which is never transmitted via NFC.
Do RFID wallets and aluminum cases really work?

The effectiveness of shielded wallets for protecting contactless cards is physically real, as they create a Faraday cage that blocks radio waves. However, they address a security issue that, statistically and technically, does not exist in the real world.
Materials such as aluminum, carbon fiber, or fabrics interwoven with metal threads physically prevent electromagnetic waves at 13.56 MHz (the NFC frequency) from reaching the card's antenna. If you place your card in one of these sleeves, no POS terminal will be able to read it.
However, the marketing of these products omits three crucial factors:
- The distance limit: NFC only works within 4 centimeters . A thief would literally have to rub a card reader against your pocket.
- Card Clash: If you have two or more contactless cards in your wallet (e.g., a debit card, credit card, or public transport pass), their signals interfere with one another. The POS terminal will display an error, as it is unable to isolate a single card to charge.
- Traceability: POS terminals are not anonymous. They are linked to a business bank account verified through KYC (Know Your Customer) procedures and anti-money laundering regulations. A thief using a POS terminal to steal €20 on the subway is literally handing over their full name and IBAN to law enforcement.
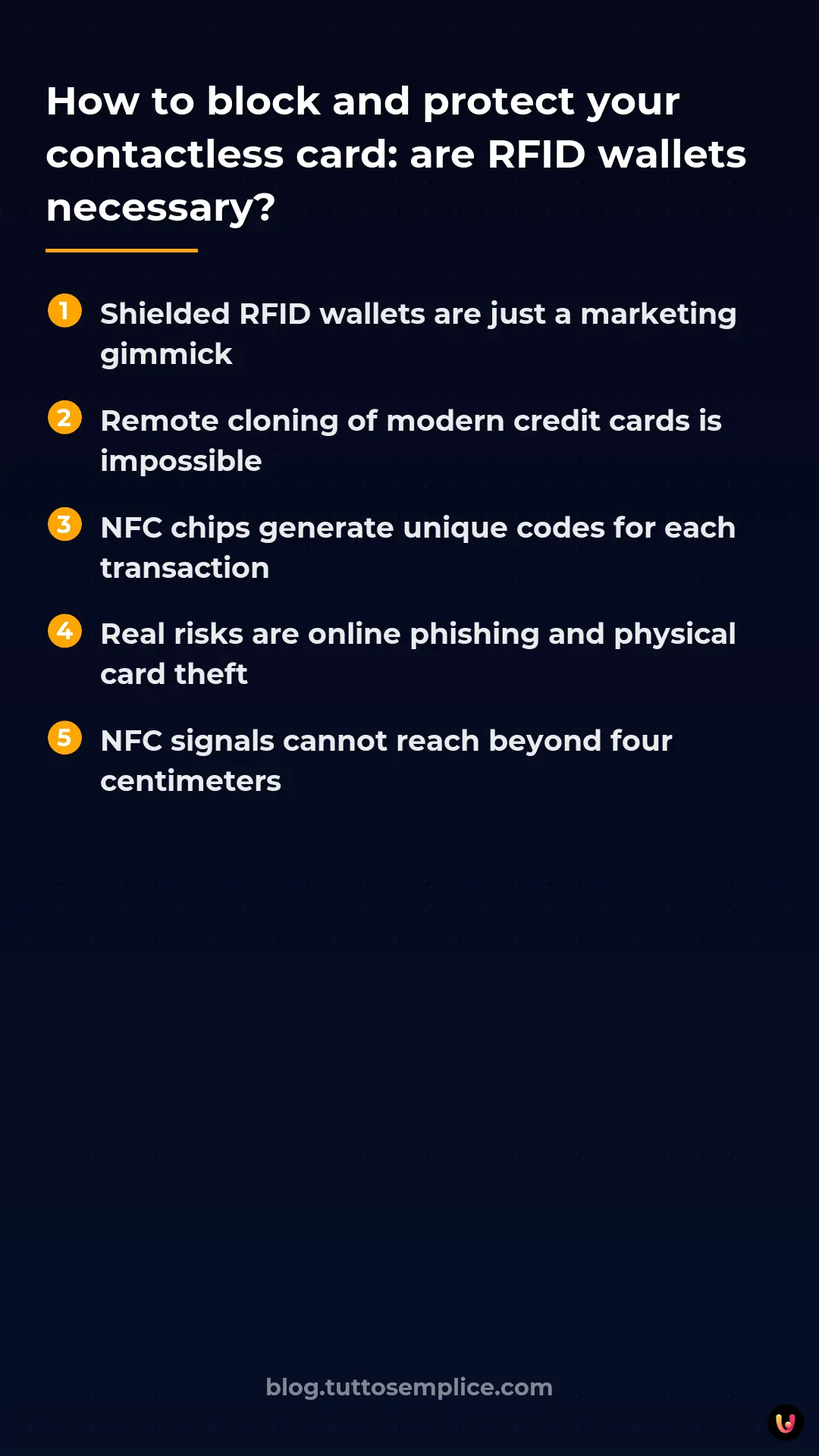
| Protection Method | Radio Signal Blocking | Real-World Utility in Combating Fraud |
|---|---|---|
| RFID Wallet | Yes (100%) | Very Low |
| Aluminum Case | Yes (100%) | Very Low |
| Jammer Card (Anti-Cloning) | Yes (Emits a jamming signal) | Very Low |
| Banking App Push Notifications | No | Very high |
How to implement real protection for your cards
True protection for contactless cards is not achieved with aluminum, but by utilizing the software tools provided by financial institutions. Proactive security and real-time monitoring are the only effective weapons against modern fraud.
Instead of worrying about proximity skimming, you should focus on real vulnerabilities. Here are the actionable steps to secure your payments:
- Enable real-time push notifications: Configure your banking app to send you an alert for every transaction, even for amounts as low as €1. This allows you to instantly block your card in the event of unrecognized charges.
- Use digital wallets: Register your cards with Apple Pay, Google Pay, or Samsung Wallet. These systems tokenize your card (creating a virtual, dummy number) and require biometric authentication (face or fingerprint) to authorize NFC payments. This offers the ultimate level of security.
- Manage transaction limits: Many modern banking apps allow you to temporarily disable contactless payments, online purchases, or international transactions with a simple tap. Enable them only when you need them.
Despite widespread fears, we have never recorded a single verified case of fraud committed by skimming a contactless card while it was inside the victim's wallet. Fraud occurs almost exclusively through social engineering, online phishing, or the physical theft of the card itself.
Annual Fraud Report, UK Finance
In Brief (TL;DR)
Remote cloning of modern contactless cards is technically impossible thanks to the dynamic, one-time cryptograms generated by NFC chips.
RFID-shielded wallets effectively block radio waves, but they solve a security problem that is statistically non-existent in the real world.
True protection against fraud is achieved by enabling bank push notifications and using digital wallets, rendering proximity skimming irrelevant.
Conclusions

In summary, protecting contactless cards using RFID wallets is a physical solution to a non-existent digital problem. EMV and NFC technologies are inherently secure against remote cloning thanks to dynamic encryption.
Purchasing a shielded wallet is not harmful and can offer peace of mind, but it should not create a false sense of security. The real dangers lurk in fraudulent text messages (smishing), phishing emails, and compromised websites . The best defense remains the use of digital wallets on smartphones, the activation of instant notifications, and a healthy dose of caution when entering card details online.
Frequently Asked Questions

Remotely cloning a modern card is impossible. The embedded chips generate one-time codes for every single transaction and never transmit sensitive data, such as the security code on the back. The real risks to your savings stem from online scams involving deceptive emails or the physical theft of the card itself.
Aluminum or carbon fiber wallets physically block radio waves, creating a veritable insulating cage, but they effectively solve a non-existent problem. Proximity-based fraud does not occur in reality, thanks to the advanced encryption of modern cards and the distance limitations of the technology. Purchasing them offers nothing more than psychological peace of mind against fears fueled by aggressive marketing.
The best defense is to utilize digital wallets on your smartphone, which always require facial recognition or biometric scanning to authorize every single purchase. It is also essential to enable instant notifications on your banking app to monitor spending in real time and manage transaction limits.
No sensitive data that could be used to commit online or physical fraud is intercepted remotely. International security standards strictly prohibit the transmission of the cardholder's name, the three-digit security code on the back, and the personal secret code. Any malicious actor equipped with a scanner would obtain only a single-use code that has already expired and is completely unusable.
A technical interference phenomenon occurs that completely prevents the payment terminal from reading the data. The radio signals emitted by the various cards overlap, causing the reader to immediately register an error. This happens because the electronic device is unable to isolate a single source from which to deduct funds, thereby ensuring natural protection.
Still have doubts about How to block and protect your contactless card: are RFID wallets necessary??
Type your specific question here to instantly find the official reply from Google.






Did you find this article helpful? Is there another topic you'd like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.