The rising sun, the rhythmic sound of shoes on the asphalt, or the whir of bicycle tires on a country road. For millions of people, daily exercise is a sacred ritual, a moment to disconnect from work stress and connect with their bodies. Yet, in this pursuit of well-being, there’s a hidden pitfall that most athletes completely ignore. The exact moment we press ‘Start’ on our smartwatch or on popular apps like Strava , we are unknowingly opening a digital window into our private lives. This harmless habit, born to track progress and share achievements with friends, has transformed into a formidable tool in the hands of modern criminals.
We live in an age where technology permeates every aspect of our existence. We worry about installing armored doors, sophisticated alarm systems, and video surveillance cameras to protect our homes . However, the real vulnerability today does not lie in a weak lock, but in the data we voluntarily and daily disseminate in cyberspace. The paradox is evident: we fortify the physical world, but leave the doors of our digital world wide open, providing malicious actors with a detailed, real-time map of our habits.
The digital treasure map: how tracking works
To fully understand the seriousness of this phenomenon, it is necessary to analyze how tracking devices work. When a runner or cyclist leaves home, the GPS receiver in their watch or smartphone connects to a network of satellites to calculate their exact position with a margin of error of only a few meters. At the end of the workout, this data is uploaded to social platforms dedicated to fitness.
The problem arises when the user starts and ends their training session right in front of their front door or garage gate. On the application’s public map, a line becomes visible to everyone, starting from point A and returning to point A. If this is repeated dozens of times a month, the origin point becomes unmistakable. A thief only needs to open the application, look for active users in a specific residential neighborhood, and observe where the lines of their routes converge. In a few seconds, they have obtained the exact address of a potential victim.
OSINT and Cybersecurity: How Modern Thieves Think
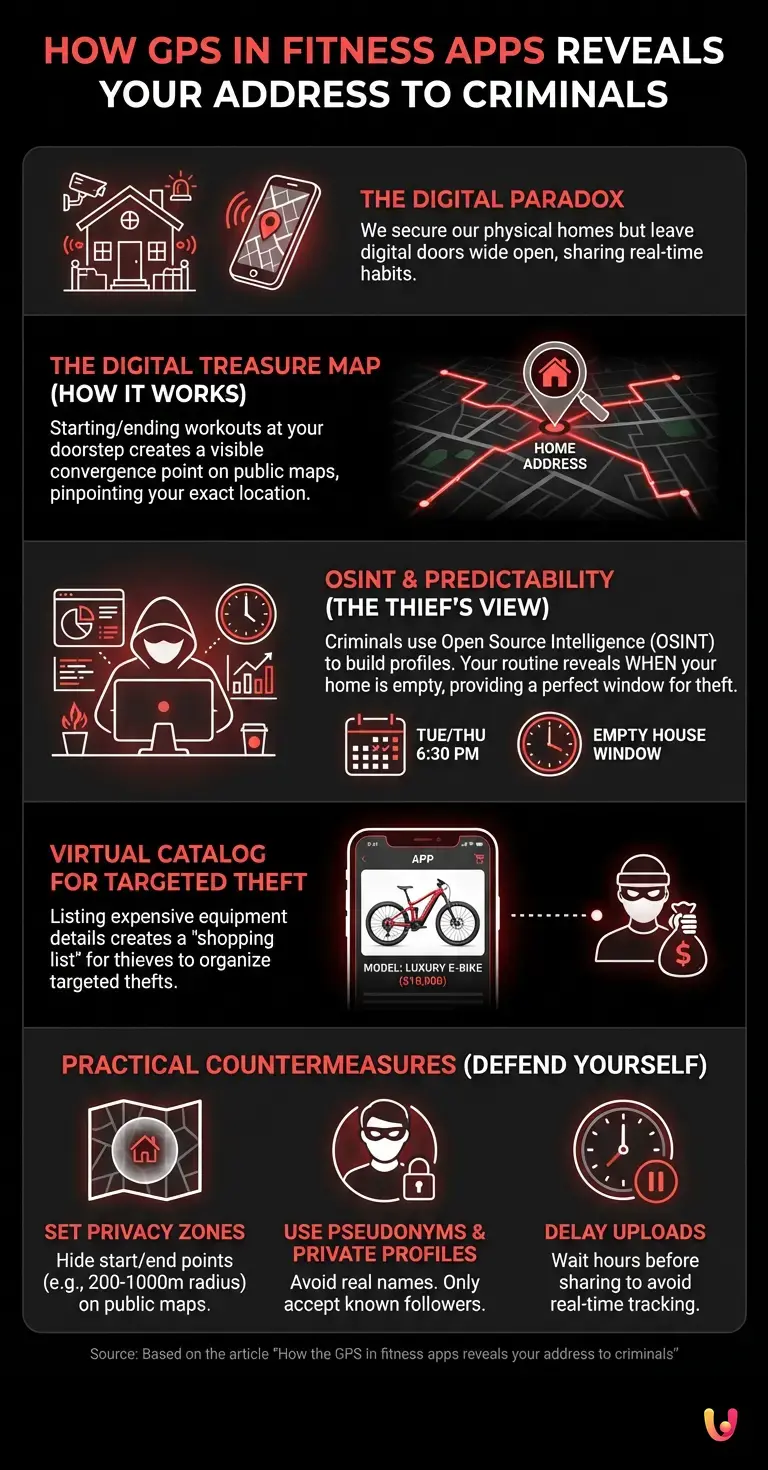
This modus operandi falls under what cybersecurity experts call OSINT (Open Source Intelligence), which is the activity of collecting and analyzing information from public sources. Today’s criminals don’t always need hacking skills to breach our systems; they often simply collect what we ourselves publish. Cybersecurity is no longer just about protecting passwords or bank accounts, but extends to managing our digital footprint.
Modern-day thieves operate like true data analysts. They create fake profiles on fitness apps, join local virtual clubs, and begin monitoring their prey. They don’t just find out where a person lives; they cross-reference data to build a complete behavioral profile . This is where the habit of exercising becomes a double-edged sword.
The predictability of our habits: the time factor

In addition to the ‘where’, tracking applications reveal the ‘when’ and the ‘how much’. Most amateur athletes have a well-defined routine, dictated by work schedules and family commitments. Some run every Tuesday and Thursday at 6:30 PM for exactly one hour, and others go cycling on Sunday mornings from 8:00 AM to 12:00 PM.
For a burglar, this information is worth its weight in gold. Knowing that the homeowner is ten kilometers away and, based on their average pace, won’t be back for at least forty-five minutes, provides a perfect window of time to act undisturbed. The thief no longer has to stake out a house for days in an anonymous car to study the family’s movements; they just need to receive a push notification on their smartphone that says: ‘User X has just started a workout.’
The virtual catalog for commissioned thefts
There is an additional layer of risk that particularly affects cyclists. Many platforms allow users to enter the exact model of the bicycle used into their equipment to keep track of component wear. Modern racing bikes or e-bikes can cost from 3,000 to over 10,000 euros. They are luxury goods, easily resold on the black market or dismantled to sell their parts.
Criminals use fitness apps as a virtual catalog. They look for specific bicycle models, identify the user who owns them, track the route to their garage, and organize a targeted theft. Often, these thefts occur at night, targeting sheds and cellars that are notoriously less protected than the main house. The victim wakes up the next morning to find their garage broken into and their valuable equipment gone, unaware that they themselves provided the inventory and address to the thieves.
The Role of Startups and Digital Innovation
Faced with this growing threat, the tech world has not stood idly by. Several startups are developing advanced solutions to mitigate the risks associated with sharing geolocated data. Digital innovation in this sector is focusing on dynamic anonymization algorithms and artificial intelligence capable of blurring sensitive data without compromising the user experience.
Some new companies are proposing systems that randomly alter the start and end point of a variable radius, making it impossible for an outside observer to pinpoint the exact location. Others are integrating machine learning functions that alert the user if their profile is showing overly predictable patterns or if they are sharing potentially dangerous information. The goal is to find the delicate balance between the social nature of these platforms and the imperative need to protect individuals’ privacy.
How to defend yourself: practical countermeasures
While waiting for these new technologies to become the market standard, it is essential to adopt a proactive approach to your security. The first and most important countermeasure is setting up ‘Privacy Zones’. Almost all major applications offer this feature: it allows you to hide a portion of the map (usually a radius of 200-1000 meters) around a specific address, such as your home or workplace. The workout will be recorded in full for statistical purposes, but other users will see the route start and end in the middle of nowhere, far from your home.
Another recommended practice is to avoid using your real first and last name, opting for a pseudonym instead, and to make your profile private, only accepting follow requests from people you actually know. Furthermore, it is wise to avoid including the exact details of your expensive equipment and, if possible, delay uploading your workout by a few hours, so as not to provide real-time information about your location.
In Brief (TL;DR)
Sharing workout routes via GPS apps unknowingly exposes our home address to modern-day criminals.
Malicious actors analyze public data to discover our schedules, obtaining perfect time windows to act undisturbed during our absence.
These sports platforms also serve as virtual catalogs, allowing thieves to identify and steal expensive bicycles and equipment.
Conclusions

Sharing our sporting achievements is a motivating and fun habit, but it should never come at the expense of our personal safety. The intersection between the physical and digital worlds requires a new awareness: the data we generate by running in a park or cycling in the mountains has tangible value and can be exploited against us. Understanding the mechanisms by which information is collected and analyzed is the first step to defending ourselves. Correctly configuring the privacy settings of your applications is not an act of paranoia, but a necessary measure of digital hygiene in the twenty-first century. Only in this way can we continue to enjoy our morning run, with the certainty that the only thing we are leaving behind is the effort, and not the keys to our house.
Frequently Asked Questions

Malicious individuals analyze public workout maps shared by users. If a person constantly starts and stops GPS tracking in front of their home, a convergence point visible to everyone is created. This allows thieves to pinpoint exactly where the potential victim lives and to study their habits.
Regularly publishing your routes reveals your daily routine and the exact times when your home is empty. Criminals exploit this information to know precisely how much time they have to act undisturbed. By calculating the owner’s distance and their average pace, thieves know exactly when the person will return home.
Privacy Zones are a security feature offered by major sports platforms to hide a portion of the map around a sensitive location. By setting a protection radius around your home, the system records the entire session but shows other users a route that starts and ends in the middle of nowhere. This way, your exact location is protected.
Many cyclists enter the technical details of their equipment to monitor wear and tear and mileage. Criminals use this data as a virtual catalog to organize thefts to order. To protect yourself, it is essential to avoid publishing the make and model of your bike, use a pseudonym, and make your profile private by only accepting people you actually know.
Cybersecurity experts recommend delaying data uploads by a few hours after the end of the sports session. Publishing the route in real-time provides malicious actors with immediate information about your current location. Waiting some time before sharing statistical results eliminates the risk of being tracked live during your physical activity.
Still have doubts about How the GPS in fitness apps reveals your address to criminals?
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading








Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.