Every day, millions of times per second, users’ fingers all over the world perform an automatic and almost unconscious dance on keyboards or touchscreens: they copy and paste. Whether it’s a quote, a funny link, an email address, or, more critically, a bank password, we take it for granted that the text travels safely and instantly from point A to point B. However, in that fraction of a second when words disappear from their original source to magically reappear in the destination field, they pass through a real “digital limbo.” This transition space is governed by the system Clipboard (or simply “Clipboard”), the main entity and the beating heart of this seemingly trivial operation. But where exactly is this place? And, above all, who else is watching while our data is there?
The Anatomy of a Daily Action
To understand the nature of this invisible trap, we must first break down the action itself. When we select text and issue the copy command, our device’s operating system (whether Windows, macOS, iOS, or Android) takes that data and allocates it to a specific portion of the RAM (Random Access Memory). The system clipboard is not a physical file saved on the hard drive, but a volatile memory area, designed to be extremely fast and easily accessible.
The invention of this mechanism dates back to the 1970s, thanks to the computer genius Larry Tesler, who was looking for a way to simplify human-machine interaction. At the time, the idea that a piece of text could be “held” in memory for reuse was revolutionary. Today, technology has evolved to the point where clipboards contain not only plain text, but complex formatting, images, files, and even metadata. However, the basic architecture has remained true to its original conception: a temporary, shared storage space, historically open to all processes running on the device.
The public square of your device
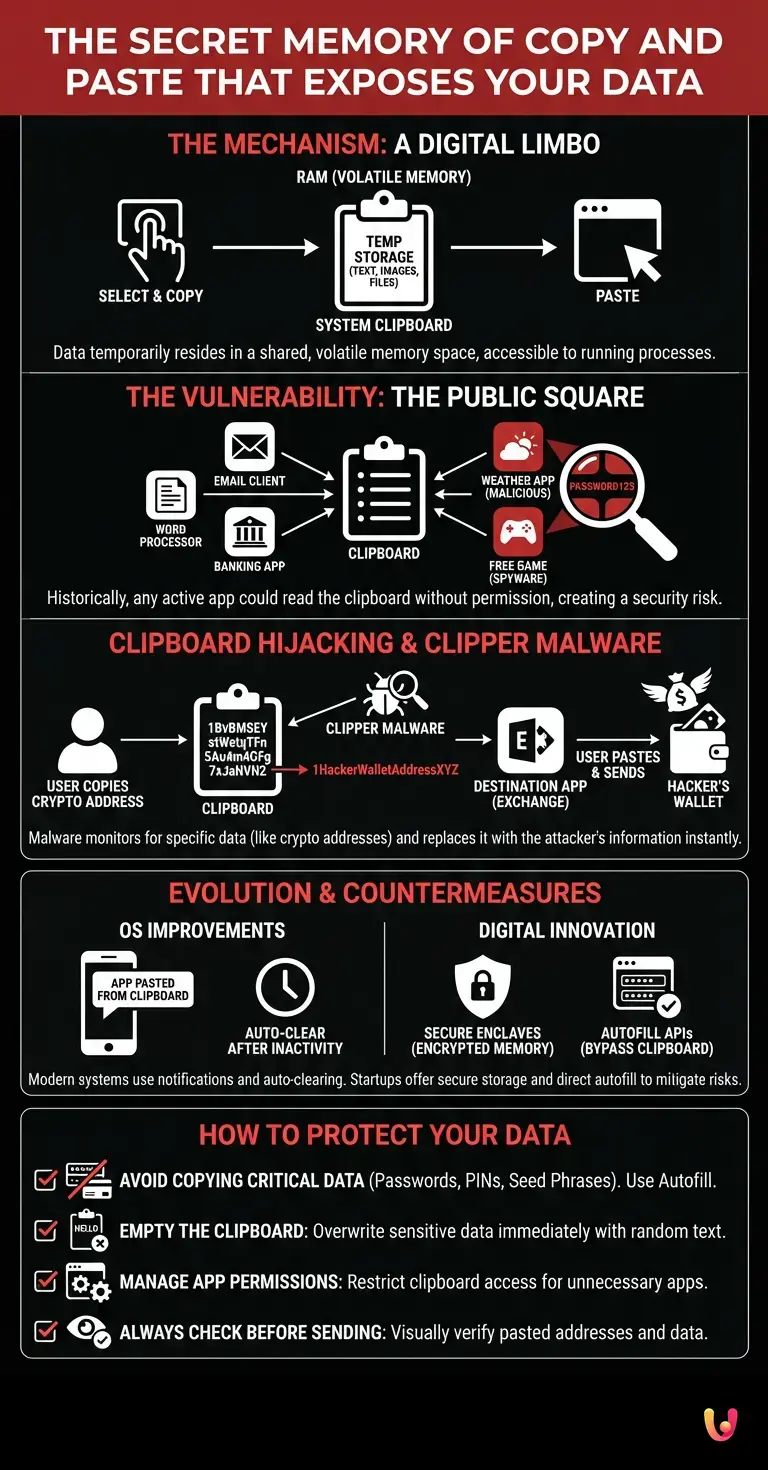
It is precisely in this “shared” nature that the crux of the matter lies. For decades, operating systems have treated the system Clipboard as a kind of public square. Any active application on the computer or smartphone could, without requiring any special permission, “look into” this square and read what was written there. The original intent was noble: to ensure maximum fluidity and interoperability between different programs. If I copy text from a word processor, my email client must be able to read it instantly to paste it.
However, in today’s cybersecurity landscape, this openness represents a structural vulnerability of enormous proportions. Imagine copying your bank account password from your password manager to paste it into the banking app. In those few seconds that the password resides in the clipboard, a malicious application in the background (perhaps a harmless free game or a weather app) could read that data, record it, and send it to a remote server. All of this happens in complete silence, without the user noticing anything.
The phenomenon of Clipboard Hijacking

This vulnerability has given rise to a specific and insidious form of cyberattack known as Clipboard Hijacking . Cybercriminals have developed specialized malware, called “Clipper,” that not only passively spies on what we copy but actively intervenes to modify it.
The preferred target of these attacks is the world of cryptocurrencies. Cryptocurrency wallet addresses are long and complex alphanumeric strings, impossible to memorize and difficult to type manually . The average user inevitably relies on copy-pasting to transfer funds. Clipper malware, running silently on the device, constantly monitors the system’s clipboard. As soon as it detects a text string that matches the format of a Bitcoin or Ethereum address, it instantly replaces it with the hacker’s wallet address.
When the user pastes the address into the exchange app and presses “send,” the funds are irreversibly transferred to the criminal. The victim, convinced they pasted what they had copied, only realizes the theft when it’s too late. This scenario unequivocally demonstrates how cybersecurity must address not only large network infrastructures but also the micro-processes occurring within our personal devices.
The Evolution of Operating Systems and Countermeasures
Fortunately, the technology industry has not stood idly by. In recent years, we have witnessed a paradigm shift in clipboard management . Software giants have begun to implement strict restrictions to transform that “public square” into a controlled environment.
On mobile devices, for example, the introduction of visual notifications marked a turning point. When an app reads the contents of the clipboard, the operating system displays a small alert on the screen (a banner or a “toast message”). This simple notification exposed dozens of popular applications that, until then, systematically read users’ clipboards at every startup, often for advertising profiling or tracking purposes. Furthermore, modern operating systems tend to automatically clear the system Clipboard after a certain period of inactivity, reducing the time window in which sensitive data remains exposed.
The Role of Startups and Digital Innovation
In this context of growing awareness, digital innovation is playing a crucial role. Several startups are developing advanced solutions to mitigate the risks associated with copy-pasting. Some of these companies focus on creating “secure enclaves” within the device’s memory: encrypted and isolated areas where sensitive data can transit without being exposed to the rest of the operating system.
Other startups are revolutionizing the very concept of data entry, promoting technologies that completely bypass the system clipboard. Modern password managers , for example, use the Autofill APIs provided by operating systems. Instead of forcing the user to copy and paste the password, the manager communicates directly and in an encrypted manner with the text field of the target application, eliminating the step in the clipboard “limbo” altogether and neutralizing the risk of interception at its root.
How to protect your data in everyday life
Despite technological advancements, the first line of defense remains user awareness. Understanding where words end up before they are sent allows us to adopt safer behaviors. Here are some fundamental practices:
- Avoid copying critical data: Whenever possible, never copy passwords, PINs, credit card numbers, or recovery keys (seed phrases). Always use secure autofill features.
- Empty the clipboard: If you are forced to copy sensitive data, it is good practice to overwrite it immediately after use by copying a random word (such as “hello” or a blank space) to erase the previous trace from volatile memory.
- Manage app permissions: Pay attention to the applications you install and the permissions they require. A flashlight app or a calculator app has no legitimate reason to access your clipboard or the internet.
- Always check before sending: Especially when pasting complex web addresses, bank IBANs, or cryptocurrency addresses, it is vital to visually check at least the first and last characters of the pasted string before confirming the transaction.
In Brief (TL;DR)
The copy and paste function temporarily saves our sensitive data in the system clipboard, an extremely vulnerable and accessible memory area.
Without requiring special permissions, malicious background applications can spy on the device’s clipboard to silently steal critical information such as banking passwords.
Cyberattacks known as Clipboard Hijacking exploit the clipboard to alter cryptocurrency addresses and irreversibly steal victims’ funds.
Conclusions

Copy-paste is one of the most powerful and ubiquitous tools that technology has ever provided us. It has shaped the way we work, communicate, and interact with machines, making the transfer of information a fluid and natural gesture. However, convenience should never make us lower our guard. That brief moment when our words, our numbers, and our secrets reside in the device’s temporary memory represents a critical crossroads for our privacy.
The transition from an open-sharing model to one of integrated security is underway, driven by large companies and the brilliant minds of new technology ventures. But until the architecture of our devices is intrusion-proof, it is up to us to remember that in the digital world, nothing truly disappears into thin air: every piece of data has its own path, its own resting place, and potentially, an unwanted spectator ready to take advantage of it. Awareness of this invisible mechanism is the first, fundamental step to regaining control of our most valuable information.
Frequently Asked Questions

Clipboard hijacking is a malicious computer technique in which hidden software spies on or modifies data copied to the device’s clipboard. Criminals use specific programs to intercept sensitive information, for example, by replacing cryptocurrency wallet addresses with their own to steal funds during copy and paste operations.
When you copy an item, the operating system temporarily saves it to the Clipboard, which is a specific area of the device’s RAM. It is not a physical file on the hard drive, but a volatile and shared space that different running applications can access to read the saved information.
To protect critical information, it is advisable to use the secure autofill functions of password managers, avoiding copying secret codes altogether. If you are forced to do so, it is essential to immediately overwrite the memory by copying a random word and always check the permissions required by the applications installed on your phone.
Historically, operating systems allowed any program to access the clipboard to facilitate data exchange between different software. Today, many applications exploit this vulnerability to collect data for advertising profiling or tracking purposes, which is why modern systems display a visual warning when this access occurs.
The simplest and fastest way to clear sensitive data from the clipboard is to immediately copy a harmless text, such as a random word or a blank space. This simple action overwrites the previous information in the volatile memory, preventing any malicious software from reading previously copied passwords or bank codes.
Still have doubts about The secret memory of copy and paste that exposes your data?
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading

- Clipboard (computing) Architecture and Operating System Management – Wikipedia
- Larry Tesler (Inventor of the Copy and Paste commands) – Wikipedia
- What To Know About Cryptocurrency and Scams – Federal Trade Commission (.gov)
- Guidelines for Managing the Security of Mobile Devices in the Enterprise – NIST (.gov)






Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.