The most dangerous myth of 2026 is believing that scam emails are still full of grammatical errors, rough translations, or grainy graphics. Forget the old “Nigerian prince”: today, thanks to generative Artificial Intelligence, cybercriminals create impeccable communications, perfect voice clones, and websites indistinguishable from the originals. If you still rely on looking for typos to understand how to recognize phishing , you are already the ideal victim. The real defense requires a radical paradigm shift, based on technical analysis and proactive verification tools.
Select the elements in the message (Email, SMS, or Chat) to calculate the probability of a scam in real time.
No alert signals selected. However, remain vigilant and always verify the source.
The Evolution of Scams: The Role of Artificial Intelligence
To understand how to recognize phishing in the age of AI, it is essential to analyze the new attack vectors. Criminals use Large Language Models to generate hyper-personalized texts and audio/video deepfakes, making online scams extremely sophisticated and difficult to detect with the naked eye.
Until a few years ago, phishing campaigns were massive and generic (the so-called "spray and pray" approach). Today, the main threat is automated Spear-Phishing . Attackers use AI-based scripts to scrape your data from LinkedIn, Instagram, and public databases. The result? You receive an email that accurately cites your job title, your boss's name, and a project you're working on, asking you to download a fake urgent report.
Furthermore, 2026 saw an explosion of Vishing (Voice Phishing) powered by audio Deepfakes . Just a few seconds of your public video are enough to clone your voice. Scammers call employees or family members simulating financial emergencies, completely bypassing text-based defenses.
Warning Signs: Identifying Fraudulent Emails and Text Messages
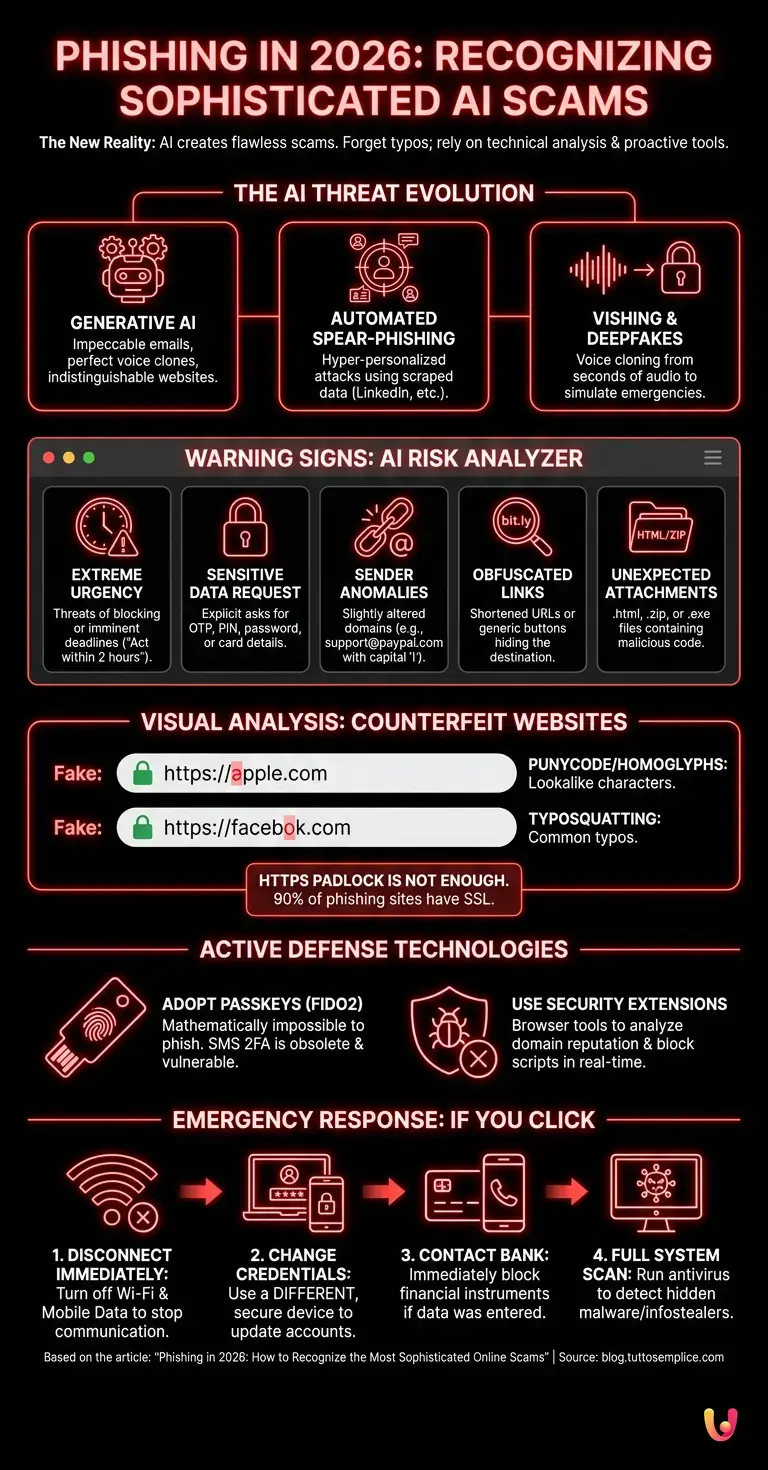
Learning how to recognize phishing via email and SMS requires attention to technical details. Always verify the sender's real address through the email headers, be wary of unjustified urgency, and never click on shortened links received via SMS without expanding them first.
The golden rule is to never trust the "Display Name" in your email client. An email might show "Banca Intesa Support", but the real address hidden behind it could be security-alert@banca-intesa-update.com . To unmask these frauds, you need to analyze the technical details:
- Checking security protocols: According to official Google Workspace and Microsoft 365 documentation, a legitimate email from a financial institution will always pass SPF, DKIM, and DMARC checks. If your email client reports that the sender's identity cannot be verified, delete the message.
- Smishing (SMS Phishing) and Obfuscated Links: Text messages that warn of "packages on hold" or "locked accounts" often contain links like t.co or bit.ly. Use free URL expansion services to see the final destination before tapping on the screen.
- The HTML attachment trick: One of the most common techniques in 2026 is sending .html attachments. Clicking on them doesn't open a document, but executes local code in your browser that perfectly simulates the Microsoft or Google login page, bypassing traditional anti-spam filters.
Visual Analysis: Distinguishing Counterfeit Websites
Knowing how to recognize phishing on cloned websites saves your banking data . Always check the exact URL, pay attention to homoglyph characters (like a Cyrillic "a" instead of a Latin one), and don't blindly trust the HTTPS padlock, which is now also used by scammers.
The green padlock or secure connection icon (HTTPS) only means that the connection between you and the site is encrypted. It does not guarantee in any way that the site is legitimate. Today, over 90% of phishing sites have a valid SSL certificate. Here's what you need to look out for:
| Falsification Technique | How it Works | How to Defend Yourself |
|---|---|---|
| Punycode Attacks (Homoglyphs) | Use of characters from different alphabets (e.g., Cyrillic) that look identical to Latin characters (e.g., apple.com vs. аpple.com ). | Check whether the browser translates the URL into a format that begins with xn-- . |
| Typosquatting | Registration of domains with common typos (e.g., facebok.com or netflix-login.com ). | Use your favorites to access sensitive sites or type the URL manually. |
| Fake Captchas and Pop-ups | Pages that require you to solve a fake Captcha to download malware or steal sessions. | Verify that the main domain corresponds to the requested service before interacting. |
Anti-Phishing Tools and Active Defense Technologies
In addition to human attention, you need the right tools to recognize and block phishing . Use browser extensions based on machine learning, enable FIDO2 authentication via passkeys, and configure advanced filters on your email client .
Human error is inevitable, which is why technology must intervene where the eye fails. In 2026, SMS-based two-factor authentication (2FA) is considered obsolete and vulnerable to SIM Swapping and Adversary-in-the-Middle (AiTM) proxy attacks. The definitive solution is the adoption of Passkeys .
According to official FIDO Alliance documentation, hardware security keys (like YubiKey) or Passkeys integrated into biometric devices make credential phishing mathematically impossible. Even if a user is tricked into entering their data on a fake site, the Passkey will refuse to authenticate the session because the cryptographic domain does not match the original one.
At the software level, it is imperative to have browser extensions dedicated to security (such as Malwarebytes Browser Guard or Bitdefender TrafficLight) that analyze the reputation of domains in real time and block the execution of malicious scripts before the page is rendered.
Emergency Management: What to Do After Clicking a Suspicious Link
If you were unable to recognize phishing in time and clicked on a link , immediately disconnect the device from the network. Change the passwords from other devices, contact your bank, and monitor your main accounts for any unusual activity.
Panic is the worst enemy in case of compromise. If you realize that you have entered data on a fraudulent portal or downloaded a suspicious file, follow this containment procedure:
- Isolation: Disable the Wi-Fi and data connection of the compromised device. This prevents any malware from communicating with the criminals' command and control (C2) servers.
- Credential remediation: Using a different and secure device, immediately access your main accounts (email, bank, social) and change the passwords. Make sure to terminate all active sessions.
- Financial block: If you have entered your credit card details, contact your bank's toll-free number to block the card . Modern fraud can empty an account or cause losses of thousands of euros in a few minutes.
- Deep scan: Perform a full system scan with up-to-date antivirus software to detect any Trojans or infostealers installed in the background.
Real-World Case Study: The Social Engineering Attack on MGM Resorts
A prime example of how scams have evolved is the devastating attack on MGM Resorts. The criminals from the Scattered Spider group did not breach firewalls with complex code, but instead used advanced social engineering techniques (Vishing) to trick the IT help desk. By impersonating legitimate employees whose data they found on LinkedIn, they obtained an MFA credential reset. This case demonstrates that the human factor remains the weak link and underscores the importance of rigorous identity verification protocols, regardless of the technology employed.
Conclusions

The threat of phishing in 2026 has reached unprecedented levels of sophistication, transforming from simple, ungrammatical emails into full-fledged psychological manipulation campaigns driven by Artificial Intelligence. Understanding how to recognize phishing today means abandoning old certainties and adopting an approach based on the "Zero Trust" principle: never blindly trust any unexpected communication, no matter how authentic it may seem.
The combination of human awareness, proactive source verification, and the adoption of anti-phishing cryptographic technologies like FIDO2 Passkeys represents the only effective shield against modern online scams. Cybersecurity is no longer just a problem for technicians, but an essential life skill for protecting one's identity and assets in the digital world.
Frequently Asked Questions

To identify modern scams, it's not enough to look for grammatical errors, as the texts are now perfect. You need to analyze the technical details of the message by verifying the sender's real address and security protocols. Pay close attention to unjustified urgencies and never open attachments in HTML format or shortened links without first expanding them through dedicated services.
The first fundamental action is to immediately disconnect the device from the Wi-Fi network and mobile data to block any malicious communications in the background. Next, you need to use a different, secure computer to change the passwords for your main accounts and perform a full antivirus scan. If you have entered financial data, contact your bank immediately.
The presence of a secure connection only indicates that the traffic is encrypted, but it does not guarantee the real identity of the visited portal in any way. To unmask a clone site, you must carefully check the web domain to exclude the presence of anomalous characters or small typos. The best advice is to use saved favorites to access sensitive services.
The most effective method is to use passkeys based on the FIDO2 standard or hardware security keys, which make credential theft mathematically impossible. At the software level, it is strongly recommended to install browser extensions dedicated to security that analyze domain reputation and block malicious scripts in real time before they load.
Temporary codes sent via text message are considered obsolete because they are vulnerable to sophisticated attacks such as SIM card cloning. Cybercriminals can easily bypass these defenses by capturing the code at the exact moment the victim enters it on the fake page using automated intermediary servers.
Still have doubts about Phishing in 2026: How to Recognize the Most Sophisticated Online Scams?
Type your specific question here to instantly find the official reply from Google.







Did you find this article helpful? Is there another topic you'd like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.