In the vast and complex landscape of modern technology , we invest immense resources to protect our digital lives. We use complex alphanumeric passwords , enable two-factor authentication, and rely on state-of-the-art biometric recognition systems. Yet, there exists a structural vulnerability—a veritable Achilles’ heel—that cybercriminals exploit daily with an alarming success rate. This vulnerability lies not in a flaw in the source code, but in an obsolete mechanism that we have all used at least once: security questions . It is precisely through this system, originally designed to assist us, that an innocent childhood memory is transformed into the perfect digital master key for fraudsters.
The Illusion of Shared Memory and the Human Factor
To understand how a memory can be turned into a weapon, we must analyze why digital service providers—from banks to email platforms —have implemented this system. The human mind is notoriously inefficient at memorizing random strings of characters, yet it is extraordinarily adept at retaining emotional anchors linked to one’s past. When we forget a password, the system needs to verify our identity using information that, in theory, only we should know.
This is where the trap comes into play. Platforms ask us to provide intimate yet easily memorable details: “What was the name of your first pet?” “In which city did your parents meet?” “What is the name of your elementary school teacher?” For decades, we regarded this information as impregnable secrets. However, in the age of hyper-connectivity, our childhood is no longer a locked drawer, but an open book accessible to anyone who knows where to look.
How the digital master key trap works
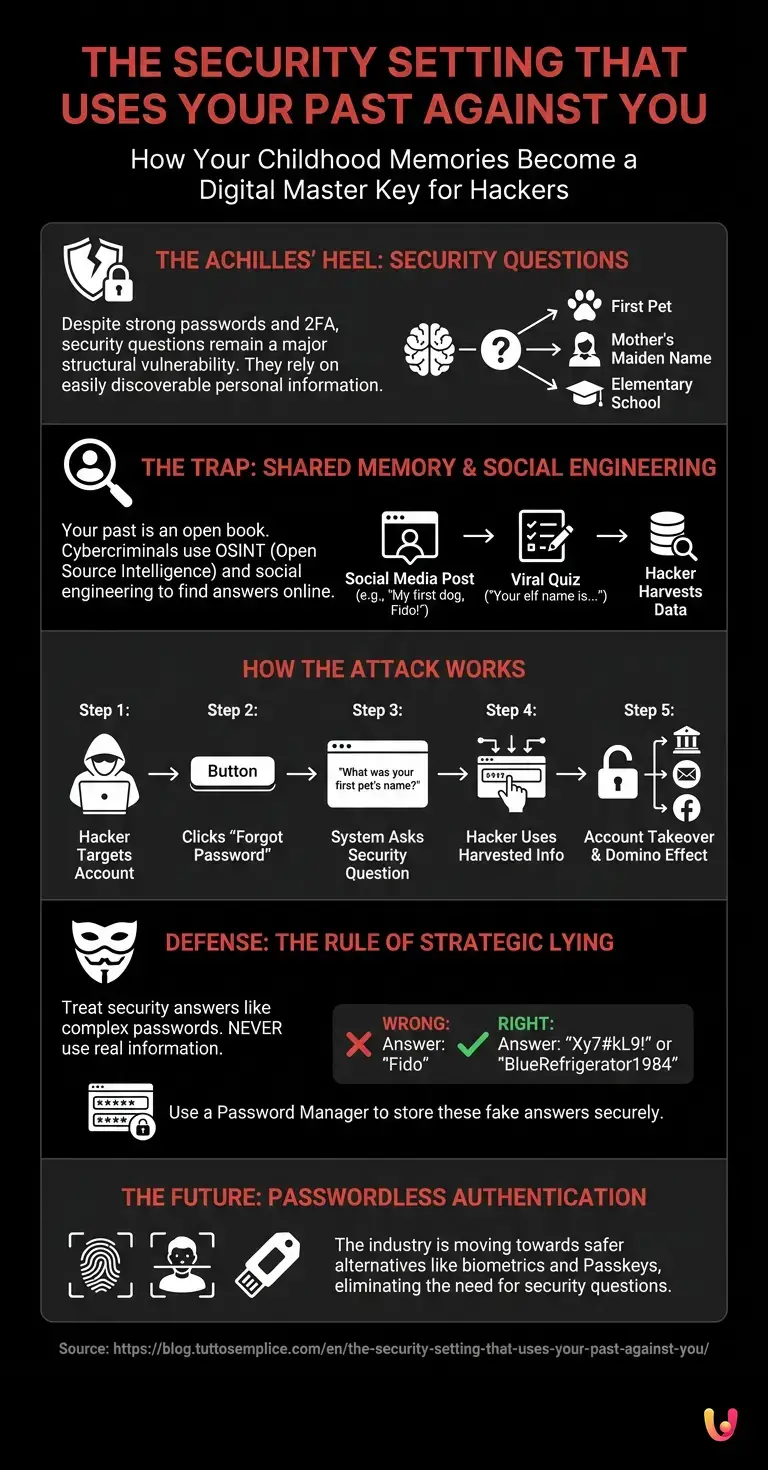
The mechanism by which scammers operate is as simple as it is devastating. They do not need supercomputers to decrypt your passwords; instead, they rely on social engineering and OSINT (Open Source Intelligence)—that is, the gathering of information from public sources. The most sought-after and exploited childhood memory of all is the name of one’s first pet, closely followed by one’s mother’s maiden name and the street where one grew up.
Let’s imagine a typical scenario. A cybercriminal identifies your email address. They attempt to log in and, naturally, fail. They then click on “Forgot Password.” To allow for a credential reset, the system asks the fateful question: “What was your first dog’s name?” At this point, the hacker need only open your social media profiles. You may never have explicitly written, “My first dog was named Fido, and I use that as my security answer,” but you might have participated in one of those viral chains on Facebook or Instagram asking users to share photos from the past. Or, you might have published a nostalgic post on International Dog Day: “I still miss you, little Fido, my childhood companion.” In that precise moment, you handed the keys to your digital safe over to a stranger.
The Role of Social Networks and Data Extraction

Modern cybersecurity clashes daily with our propensity for sharing. Scammers deliberately create seemingly harmless quizzes on social networks. You know those posts that say: “Your elf name is made up of your first pet’s name and the street where you were born! Write it in the comments!” ? These are not innocent games, but actual dragnets cast into the sea of the web to gather answers to the most common security questions.
Once this piece of information is obtained, the attacker has total control. By answering the question correctly, they can reset the main password. And since the email address is usually the cornerstone of our digital identity, from there they can request password resets for bank accounts, social media profiles, e-commerce accounts , and institutional portals. It is an unstoppable domino effect, triggered by a single, fond childhood memory.
The Evolution of Cybersecurity and Startups
Fortunately, the cybersecurity sector is becoming aware of this serious systemic flaw. In recent years, numerous startups have been driving significant digital innovation by proposing “passwordless” authentication models. These systems rely on physical tokens, advanced biometrics , or cryptographic keys (Passkeys) stored directly on users’ devices, completely eliminating the need to remember passwords or, worse yet, to answer questions based on personal data.
However, the transition is slow. Many financial institutions and legacy services still rely on outdated infrastructure that uses security questions as an emergency recovery method. Until the entire digital ecosystem abandons this practice, the responsibility for protection falls entirely on the end user.
How to Defend Yourself: The Rule of Strategic Lying
What happens if a service requires us to set up a security question? The experts’ answer is unanimous: you must lie. The golden rule for neutralizing this attack vector is to treat the answers to security questions exactly as if they were complex passwords.
If the system asks, “What is the name of your first pet?” , the answer should never be “Fido” or “Rex.” It should be a random string like “Xy7#kL9!” or a completely decontextualized phrase like “BlueRefrigerator1984.” Obviously, the human mind cannot remember these fictitious answers for dozens of different sites. This is where using a password manager becomes indispensable—encrypted software for storing not only passwords but also the (fake) answers to security questions.
Furthermore, it is essential to develop a healthy skepticism toward social media trends. Before participating in a viral quiz or sharing a childhood memory, always ask yourself: “Could this information be used to verify my identity elsewhere?” If the answer is yes, that memory must remain offline.
In Brief (TL;DR)
Traditional security questions represent a serious cybersecurity vulnerability, allowing scammers to easily bypass the protections on our digital accounts.
Cybercriminals analyze social networks and exploit fake viral quizzes to extract personal memories, using them to reset your passwords.
To counter this threat, security startups are developing innovative passwordless authentication systems based on biometrics and cryptographic keys.
Conclusions

The paradox of our age is that the most intimate and cherished details of our past have become the sharpest weapons in the hands of cybercriminals. The memory of a first pet, the name of an elementary school, or a grandparent’s hometown are no longer merely fragments of nostalgia, but actual sensitive data. Understanding that scammers use our emotional memory as a digital master key is the first step toward regaining control of our privacy. Embracing new authentication technologies and adopting the practice of “strategic lying” is not an act of paranoia, but a necessary evolution of our survival instinct in the digital world.
Frequently Asked Questions

Security questions represent a serious vulnerability because they rely on personal information that is now easily accessible online to anyone. Cybercriminals can exploit data shared publicly on social networks to guess the correct answers and gain unauthorized access to personal profiles, thereby bypassing traditional passwords.
Scammers use social engineering techniques and the targeted collection of information from public sources to obtain this sensitive data. Very often, they create fake personality tests or viral chain posts on social media platforms that trick people into unknowingly revealing intimate details, which are then used to steal credentials.
Strategic lying involves providing completely false and random answers when a web service requires you to set a security question for account recovery. Instead of using your mother’s real name or your hometown, you enter a complex alphanumeric sequence, treating it exactly as if it were an unassailable password.
To securely manage fictitious answers to security questions, it is absolutely essential to use a professional and reliable password manager. These encrypted software tools allow you to store both your primary login credentials and the random strings generated specifically to deceive malicious actors in a single, protected location.
The cybersecurity sector is progressively adopting passwordless authentication systems, which prove to be far more reliable than traditional methods. Modern solutions include biometric recognition via fingerprint or facial scanning, as well as the use of cryptographic keys stored directly on devices to eliminate risks at the source.
Still have doubts about The security setting that uses your past against you?
Type your specific question here to instantly find the official reply from Google.








Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.