Picture the scene: it is Friday evening, you have just walked into your favorite restaurant, and you are settling in at your table. The atmosphere is relaxed, and the conversation flows pleasantly. As has been the custom for several years now, you take out your smartphone, open the camera, and frame that little black-and-white maze printed on a plastic stand. At that precise moment, as the QR code redirects you to the establishment’s digital menu, you are potentially inviting an invisible, silent, and decidedly unwelcome guest to your table.
This scenario is not the plot of a spy novel, but an everyday reality that cybersecurity experts call ” the little square trick .” It is a deception as simple as it is devastating, exploiting one of our most ingrained habits to bypass digital defenses. But how exactly does this trap work? And who is this elusive guest sitting at the table with us?
The Anatomy of a Habit: Blind Trust in Technology
To understand the scope of this phenomenon, we must take a step back and analyze our relationship with technology in physical spaces. When we browse the internet from our sofa at home, we are (or should be) constantly on alert: we are wary of emails from strangers, avoid clicking on suspicious links, and verify the senders. However, when we find ourselves in a physical environment perceived as “safe”—such as a restaurant, a bar, or a hotel lobby—our psychological defenses crumble.
The small square printed on the table appears to us as an extension of the establishment itself—a physical object vouched for by the restaurateur. This unconditional trust is the true Achilles’ heel that the invisible guest exploits to their advantage. We never ask ourselves where that code will take us; we take it for granted that the destination is legitimate. It is precisely in this space—in the gap between the perception of physical safety and actual digital vulnerability—that the attack is carried out.
Who Is the Invisible Guest? The Mechanism of Quishing
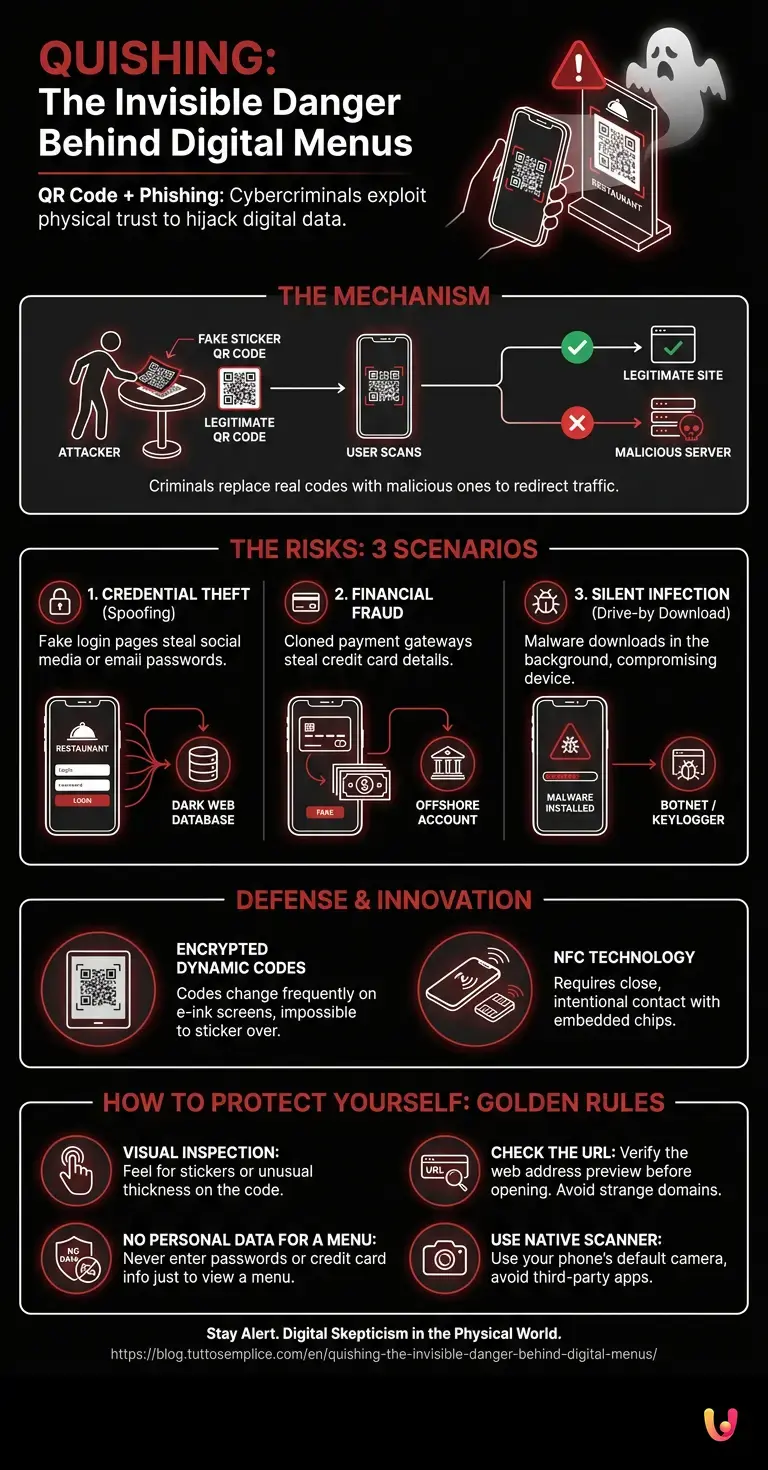
In cybersecurity jargon, this practice is known as ” Quishing ,” a portmanteau of QR Code and Phishing. The invisible guest is none other than a cybercriminal who has tampered with the physical access point to hijack your data traffic.
The mechanism is disarmingly simple. A malicious actor enters the establishment posing as an ordinary customer. While pretending to read the menu or wait for a friend, he produces a sheet of pre-printed stickers. These stickers bear malicious codes that are graphically identical to the restaurant’s original ones. With a quick movement, he places his sticker over the legitimate one on the table. From that moment on, anyone who scans the code will not be directed to the restaurant’s website, but to a server controlled by the attacker.
What exactly happens after the scan?
Once the camera has decoded the counterfeit square, the smartphone executes the instruction without hesitation. This is where the invisible guest begins to operate. The consequences of this scan can vary depending on the sophistication of the attack, but they generally fall into three main scenarios.
1. Credential Theft (Spoofing)
Your phone’s browser opens to a webpage that is an exact replica of the restaurant’s website. The colors, logos, and fonts are identical. However, to view the menu or access the free Wi-Fi, the page asks you to perform a quick login using your social media profiles or by entering your email and password. The moment you press “Submit,” your credentials do not unlock any menu; instead, they go straight into a database on the dark web, ready to be sold or used to hack into your personal accounts .
2. Direct financial fraud
In some establishments, digital systems allow you not only to place orders but also to pay the bill directly from your smartphone . An attacker clones the payment gateway interface. You enter your credit card details, believing you are settling your dinner bill, but in reality, you are authorizing a transfer of funds to an offshore account. You will only realize the deception when the waiter presents the actual bill at the end of the evening.
3. Silent Infection (Drive-by Download)
This is the most insidious scenario. You are not asked to enter any data. The page loads and displays a menu (perhaps stolen from the restaurant’s actual website to avoid arousing suspicion), but in the background, by exploiting unpatched vulnerabilities in your mobile browser , it initiates a malware download. This malicious software can turn your phone into a zombie within a botnet, or install a keylogger capable of recording everything you type in the future, including your online banking passwords .
The Role of Startups and Digital Innovation in Defense
Faced with this growing threat, the market has not stood idly by. Digital innovation is providing new weapons to combat Quishing. Several startups are developing advanced solutions to protect both merchants and consumers.
One emerging technology involves encrypted dynamic codes. Instead of a simple static link, these new solutions generate a code that changes every few seconds, displayed on small e-ink screens embedded in the tables, effectively rendering the use of physical stickers impossible. Other companies are focusing on NFC (Near Field Communication) technology, which requires close and intentional contact with a chip embedded in the table—something much more difficult to tamper with than a piece of printed paper.
Furthermore, modern smartphone operating systems are integrating increasingly intelligent native scanners capable of analyzing the destination URL before opening it, comparing it against global databases of malicious sites, and alerting the user if the domain was registered only a few days ago or exhibits suspicious anomalies.
How to Protect Yourself: The Golden Rules for Keeping Guests at the Door
Despite industry efforts, the first and most effective line of defense remains user awareness. There is no need to give up the convenience of digital menus, but it is essential to apply a healthy dose of digital skepticism even in the physical world. Here are some practical rules to avoid unpleasant surprises:
- Visual inspection: Before scanning, run your finger over the code. If you feel an unusual thickness, a raised edge, or realize that it is a sticker placed over another surface, stop and alert the staff at the venue.
- Check the URL: When you scan the code, your smartphone will display a preview of the web address (URL) before opening it. Read it carefully. If you are at “Trattoria da Mario,” the URL should be something like trattoriadamario.it , not an incomprehensible string of letters and numbers or a strange domain like menu-sicuro-login-123.com .
- No personal data for a menu: A menu is, by definition, a public document. If a webpage asks you to register, enter a password, or provide credit card details just to view the wine list, close your browser immediately.
- Use the native scanner: Avoid downloading third-party apps to read codes. These apps are often filled with deceptive advertisements or, worse, are themselves vehicles for malware. Your smartphone’s default camera is the safest and most up-to-date tool you can use.
In Brief (TL;DR)
Quishing is a cyber scam that exploits our trust in the QR codes found on digital menus in restaurants.
Criminals place counterfeit stickers over original codes to deceive customers and redirect traffic to malicious servers.
Scanning a manipulated code can result in the theft of personal data, immediate financial fraud, or the dangerous installation of malware.
Conclusions

The little square trick reminds us of a fundamental lesson of the modern era: the boundary between the physical and digital worlds has all but vanished. A tangible and innocuous object, such as a piece of printed paper on a restaurant table, can transform into a direct gateway to our most intimate and valuable information.
The invisible guest relies on our distraction, our haste, and our habit of blindly trusting technological automation. However, by understanding the mechanics of these attacks and maintaining a basic level of vigilance, we can continue to enjoy dining out while leaving cybercriminals empty-handed. The next time you sit down at a restaurant, take an extra second before scanning that code: your digital security is worth far more than the time saved ordering an appetizer.
Frequently Asked Questions

The term is derived from combining the words “QR Code” and “Phishing” and refers to a dangerous and increasingly widespread cyber scam. Criminals place stickers containing malicious codes over legitimate ones found on restaurant tables to redirect people to fake websites with the aim of stealing personal or banking information.
To detect a potential scam, it is essential to run your finger over the printed material to check for suspicious stickers placed over the original print. Furthermore, you should always carefully examine the web link previewed on your smartphone before opening it, ensuring that it corresponds to the actual name of the establishment rather than a random sequence of letters.
Scanning can lead to various dangers, including the theft of login credentials via fake registration pages and financial fraud if you attempt to pay a bill online. In the worst-case scenario, your phone could silently download malicious software capable of recording your banking passwords.
The primary rule is to never enter passwords or credit card details if the page is intended solely for viewing the menu. Furthermore, it is strongly recommended to use only your smartphone’s default camera, avoiding third-party applications that may contain deceptive advertisements or carry dangerous viruses.
Several companies are developing innovative systems, such as small electronic screens embedded in tables that display dynamic images impossible to cover with simple paper stickers. Another highly promising solution involves the use of proximity sensors that require intentional contact with a dedicated chip, making them extremely difficult to tamper with.
Still have doubts about Quishing: The Invisible Danger Behind Digital Menus?
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading

- FTC Consumer Alert: Scammers Hide Harmful Links in QR Codes to Steal Your Information
- Federal Trade Commission (FTC): Scammers Hide Harmful Links in QR Codes to Steal Your Information
- Federal Trade Commission (FTC): Scammers Hide Harmful Links in QR Codes to Steal Your Information
- Wikipedia: Phishing (Section: Quishing / QR Code Phishing)





Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.