Imagine the scene: you’re browsing a website, perhaps looking for an exclusive discount code, to download a free whitepaper, or simply to subscribe to a newsletter that interests you. You’re presented with a seemingly innocuous and minimalist online form. They only ask for two basic pieces of information: your name and your email address. You start typing, feeling secure because, after all, you’re sharing the bare minimum to get what you want. Yet, at that precise moment, a surprising amount of your personal information, much more intimate and confidential, could be silently traveling to unknown servers. How is all this technically possible? The culprit, or rather, the unwitting accomplice in this data hemorrhage, is often a feature we all use every day for pure convenience: browser Autofill . This technology, created to simplify our lives, has become one of the most insidious pitfalls of the modern web.
The illusion of control: what you see and what really happens
To fully understand this dynamic, we need to take a step back and look under the hood of a web page. When you view an online form, your brain only processes what is rendered on the screen: white text boxes, descriptive labels, and a colored button with the word “Submit.” This is the user interface, designed to be intuitive and reassuring. However, the source code that generates that page (the HTML) can contain elements that your eye will never perceive.
Web developers have a specific type of input field called a hidden field . In the code, it appears as <input type="hidden"> . These fields were originally designed for entirely legitimate purposes and are fundamental to the functioning of the web. For example, they are used to transmit security tokens that prevent cyberattacks, to keep track of the user’s session, or to pass technical parameters from one page to another without disturbing the visitor’s visual experience.
The problem arises when this legitimate architecture is bent to malicious or extreme tracking purposes. A form that seemingly only asks for “Name” and “Email” could actually contain dozens of hidden fields labeled “Home Address,” “Phone Number,” “Company,” “Zip Code,” and even “Credit Card Number.” You don’t see them, but your browser knows perfectly well they are there, waiting to be filled in.
How the trap works: the betrayal of convenience
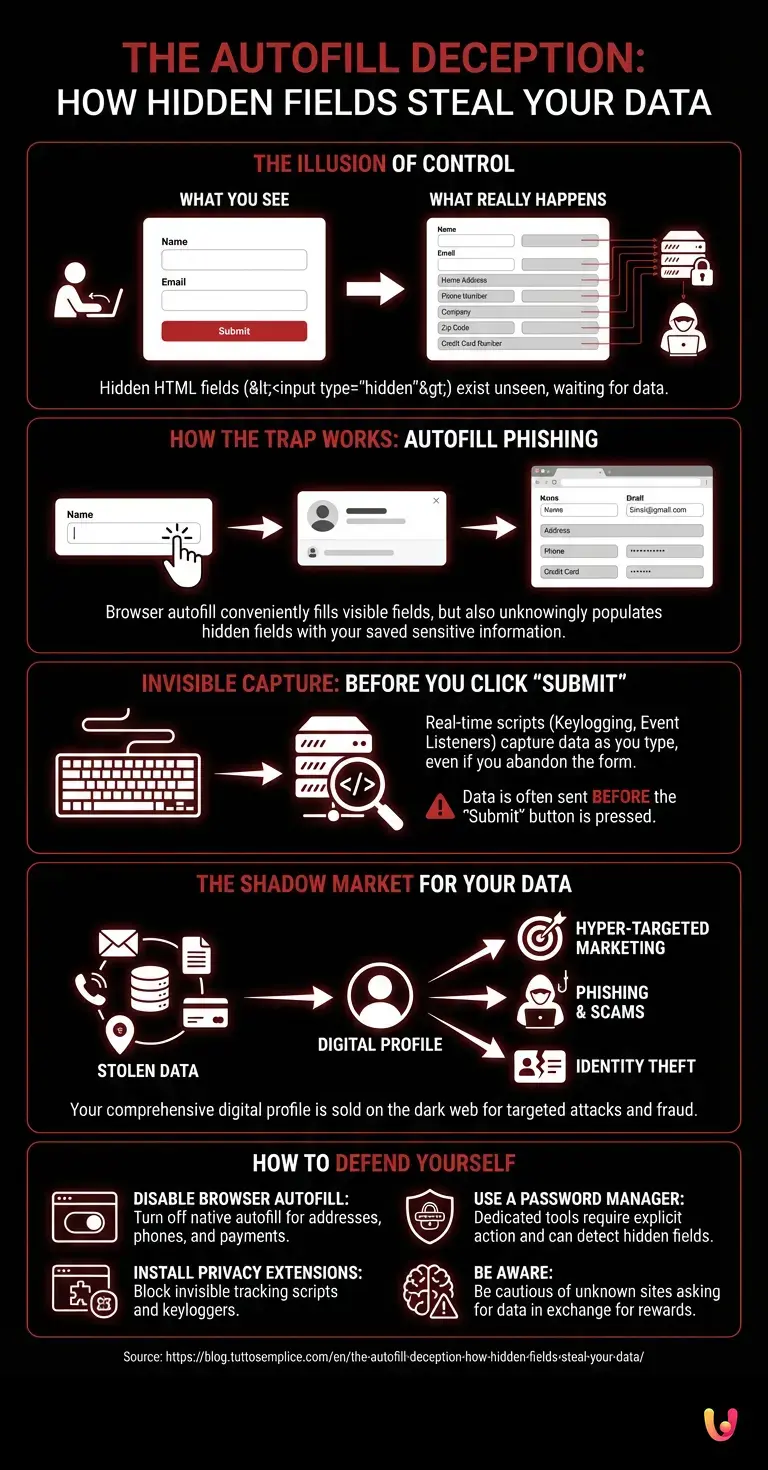
This is where the mechanism that transforms a simple form into a veritable data vacuum cleaner comes into play. When you click on the visible “Name” field, your browser (whether it’s Chrome, Safari, Firefox, or Edge) recognizes that you are about to fill out a form. To save you time, it displays a convenient drop-down menu suggesting your complete profile, previously saved in the settings. You think, “Great, so I don’t have to type everything by hand,” and select your profile.
In a fraction of a second, the browser inserts your name and email into the visible fields. But it also does something else, completely automatically and invisibly: it fills in all the hidden fields that correspond to the information in your saved profile. If the site creator has included a hidden field for the phone number and you have saved your number in the browser, that field will be filled in. The same applies to your physical address or other sensitive data.
This attack, known in cybersecurity jargon as Autofill Phishing or Hidden Field Injection , is disarmingly effective. The user presses the “Submit” button convinced that they have only shared two harmless pieces of data, when in reality they have just handed over a complete dossier on their identity. The severity of this technique lies in the fact that it does not require any advanced hacking skills to be implemented: all it takes is a basic knowledge of HTML and an awareness of how modern browsers handle autofill.
Invisible capture: when the “Send” button isn’t even necessary
If you think the trap is only sprung when you press the fateful “Send” button, prepare for another surprise. The evolution of web technology has made pages extremely dynamic, capable of reacting in real time to every single user action. This is made possible by JavaScript, the programming language that animates the web.
Many modern websites use scripts that constantly monitor input fields. Through functions called Event Listeners , the site can record every single key you press (keylogging) or detect the exact moment you move the cursor from one field to another. This means that data can be transmitted to the site’s servers as you type it, letter by letter.
What happens if you start filling out a form, enter your email, but then change your mind, decide you don’t trust it, and close the browser tab without ever clicking “Submit”? In most cases, your data has already been sent. This practice, known as Form Abandonment Tracking , is widely used in digital marketing. Companies want to know who you are so they can contact you again and convince you to complete the action. Although often passed off as a conversion optimization strategy, from a privacy perspective, it represents a very worrying gray area, as it acquires information without explicit and definitive consent.
The Shadow Market for Personal Information
Why would anyone bother to devise these invisible capture systems? The answer is simple: data is the most valuable currency in the digital economy. Every piece of information about you contributes to creating an extremely detailed digital profile, which is then sold, traded, or used for purposes ranging from hyper-targeted marketing to outright scams.
In the digital innovation landscape, there are countless companies, from web giants to small emerging startups in the AdTech (Advertising Technology) sector, whose entire business model is based on data aggregation. An email address associated with a phone number and a physical address is worth much more than a simple isolated email. It allows for cross-referencing databases, tracking your online and offline movements, and predicting your purchasing behavior with disturbing accuracy.
Even more alarming is the use that cybercriminals make of them. Data stolen through deceptive forms often ends up on the black markets of the dark web. Here, packages containing thousands of complete profiles are purchased by scammers who will use them for targeted phishing campaigns (spear phishing), identity theft, or to attempt to access your bank accounts . When you receive a fraudulent email that strangely knows your home address or phone number, it is very likely that this information was obtained through one of these invisible traps.
Cybersecurity: How to Defend Yourself Against This Silent Threat
Faced with such a hostile web ecosystem designed to surreptitiously extract information, personal cybersecurity can no longer be considered an optional extra. Fortunately, there are effective countermeasures that anyone can take to neutralize these threats without having to give up the convenience of modern browsing.
The first and most important line of defense is to disable your browser’s native autofill feature. Although convenient, as we have seen, it is inherently vulnerable because it does not distinguish between visible and hidden fields. To do this, simply access your browser’s settings (Chrome, Firefox, Safari, etc.), look for the privacy or autofill section, and disable the saving of addresses, phone numbers, and payment methods.
But how can you avoid having to type everything manually every time? The solution lies in using a dedicated and reliable password manager. Professional tools of this type are designed with a superior security architecture. Unlike browsers, the best password managers do not automatically fill in pages upon loading, but require explicit action from the user (such as a click on the extension icon or a keyboard shortcut). Furthermore, many of them are programmed to ignore hidden fields or to warn the user if they detect anomalies in the form structure, effectively blocking Autofill Phishing attacks.
Another fundamental practice is the use of privacy-oriented browser extensions that can block invisible tracking scripts. These tools prevent websites from running JavaScript code that records keystrokes or sends data before the “Send” button is pressed. Finally, awareness remains the most powerful weapon: always be wary of unknown websites that offer disproportionate rewards or discounts in exchange for “a little data,” as the real price to pay is often your privacy.
In Brief (TL;DR)
The automatic completion function of browsers, while extremely convenient, hides serious pitfalls for the security of your personal data online.
When you use this convenience, the browser also automatically fills in the hidden fields in the code, delivering your sensitive information to complete strangers.
Thanks to advanced scripts, this confidential information can be transmitted to malicious servers in real time, even before you press the send button.
Conclusions

The web is an extraordinary environment, an inexhaustible engine of knowledge and opportunity, but it is also a complex ecosystem where appearances are often deceiving. The trap of online forms teaches us a fundamental lesson: in the digital age, the visual interface is just the tip of the iceberg. Beneath the surface, invisible mechanisms are at work, designed to maximize the extraction of value from our daily interactions.
Understanding how these technologies work is not just a matter of technical curiosity, but an essential requirement for our digital self-defense. Taking back control of our data means giving up some minor conveniences, such as indiscriminate autocompletion, in favor of more secure tools and a more critical approach to browsing. Only by transforming our naivety into awareness can we continue to exploit the potential of the internet without unknowingly becoming the product for sale.
Frequently Asked Questions

This is a computer technique in which malicious actors exploit the browser’s autocomplete function to steal personal data. By inserting invisible sections into a normal online form, the system automatically inserts sensitive information such as addresses or phone numbers without you noticing. This allows criminals to build a complete profile of your digital identity.
Malicious website creators insert text boxes into the page code that are not visible on the screen. When you use the autocomplete function to enter your name or email, the browser also automatically fills in these invisible sections with your previously saved private data. In this way, you unknowingly hand over intimate details to unknown servers.
Many modern portals use advanced scripts that record every keystroke or cursor movement on the page in real time. This means that your information can be transmitted to the website’s servers while you are still typing it, long before you confirm your action. Closing the browser tab is not enough to stop this information leak.
The best solution is to disable the native autofill function in your browser’s settings. It is also very useful to use an external password manager that requires your explicit action to fill in the fields. Finally, we suggest you install privacy-dedicated extensions that block invisible tracking codes during your daily browsing.
Digital marketing companies use this practice to acquire your contact information even if you decide not to complete the initial registration. Their main goal is to be able to contact you later to convince you to complete the purchase or subscription process. This strategy often operates in a gray area for personal protection as it acquires information without your definitive consent.
Still have doubts about The Autofill Deception: How Hidden Fields Steal Your Data?
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading







Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.