How many times, during your daily browsing, have you had to tick a simple box accompanied by the phrase “I am not a robot”? Whether it’s buying tickets for a highly anticipated concert, accessing your bank account, or registering a new account, this step has become a universal routine. Yet, behind that seemingly trivial gesture lies one of the most sophisticated behavioral analysis systems on the modern web: reCAPTCHA . Originally developed by researchers at Carnegie Mellon University and later acquired by Google, this tool represents the main entity in a real invisible war that is fought every millisecond on servers around the world.
The question that plagues many users is simple yet profound: how can a simple mouse click prove to a computer that there is a flesh-and-blood human being on the other side of the screen and not automated software? The short answer is that it is not the click itself that proves it. The click is, to all intents and purposes, an illusion, a stage on which a complex data analysis takes place. To fully understand this mechanism, we must delve into the intricacies of tracking technology and discover what is actually being measured while we believe we are performing a basic action.
The illusion of the checkmark: an analysis of the movement
When the web page loads and the famous checkbox appears on the screen, the security system is already listening . The test doesn’t start when you click the left mouse button, but much earlier. What the system analyzes with extreme precision is the trajectory the cursor makes to reach the box.
Humans are intrinsically imperfect creatures. When we move our mouse toward a target, our movement is never a perfect straight line . We experience micro-tremors, imperceptible hesitations, sudden accelerations followed by asymmetric decelerations as we approach the target. Sometimes we correct our trajectory at the last tenth of a second. All this biomechanical noise is the unmistakable signature of our humanity.
In contrast, a bot (an automated program created to simulate human actions) tends to move the cursor too perfectly. Even when programmers try to insert randomization algorithms to simulate human movement, the mathematics behind these artificial curves often turn out to be too clean, too predictable for the sophisticated machine learning models used in modern cybersecurity . The system analyzes the cursor’s X and Y coordinates, the time spent at each point, and the fluidity of the movement, comparing them with billions of samples of real human behavior.
The invisible fingerprint: the browser context
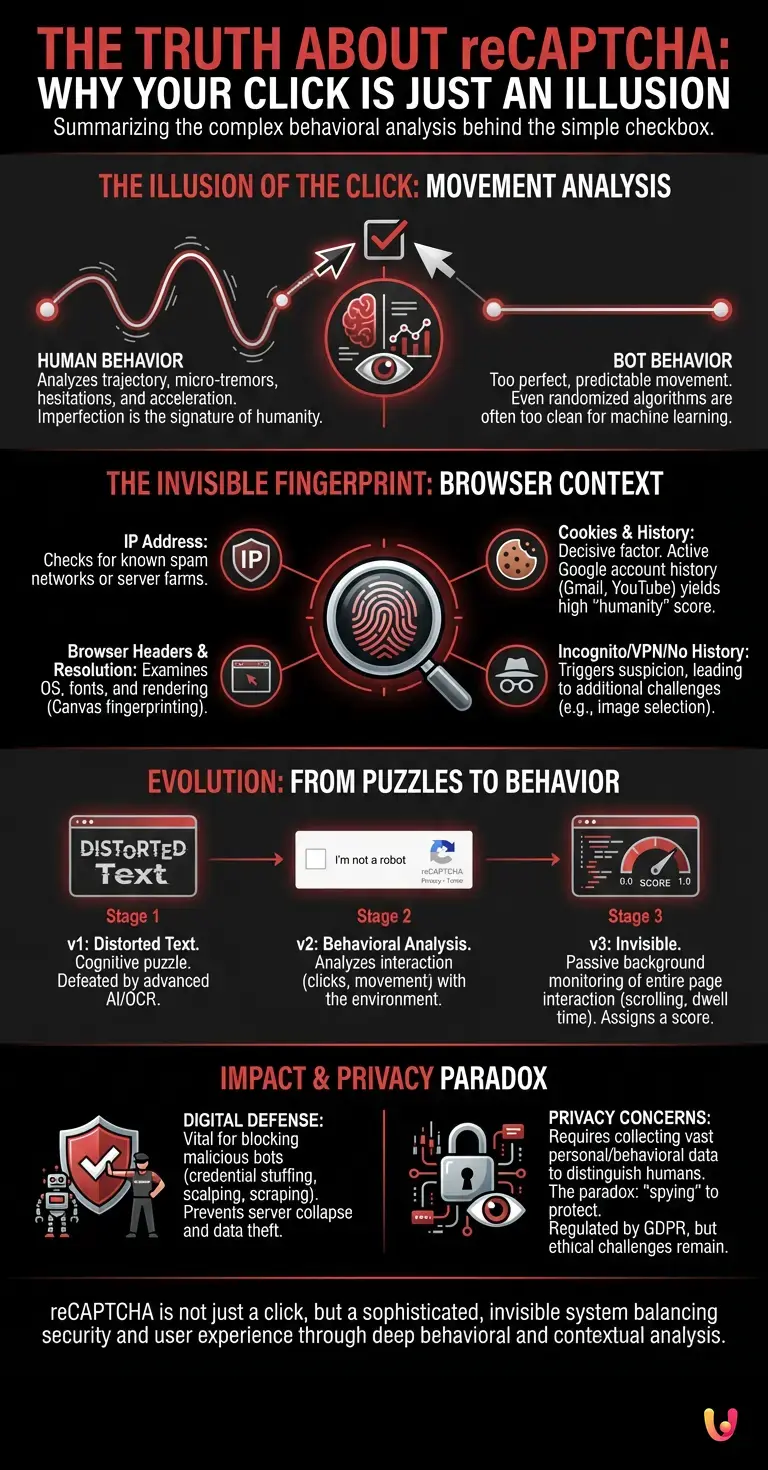
If you think mouse movement analysis is fascinating, know that it’s just the tip of the iceberg. The real decision-making engine behind the humanity test is the so-called Risk Analysis Engine . Even before you move your mouse, this engine has already collected an impressive amount of data about your browsing environment, creating a kind of fingerprint of your device.
What exactly is analyzed? The system checks the IP address to see if it comes from a network known for spamming or from a server farm. It examines browser headers, screen resolution, operating system, installed fonts, and even how your browser renders specific graphic elements (Canvas fingerprinting). But perhaps the most decisive factor is the presence of cookies and browsing history.
If you are browsing using a browser in which you are already logged in with an active Google account that has a credible history of searches, YouTube views, and Gmail interactions, the system immediately assigns you a very high “humanity” score. In these cases, clicking the box is a mere formality. If, on the other hand, you are browsing in incognito mode, using a VPN, or if your browser has no history (typical behavior of newly initialized bots), the system will become suspicious and, in all likelihood, will subject you to an additional challenge, such as selecting images containing traffic lights or pedestrian crossings.
From distorted words to behavioral analysis

To appreciate the current level of sophistication, it is useful to take a step back and observe the evolution of these systems, which represents a perfect example of digital innovation . The first CAPTCHAs (Completely Automated Public Turing tests to tell Computers and Humans Apart) consisted of distorted and blurred texts that the user had to decipher and type. The basic idea was that computers would not be able to read such deformed texts.
However, with the advent of Deep Learning and advanced neural networks, optical character recognition (OCR) software has become better than humans at deciphering those images. Cybersecurity therefore had to change its paradigm: it was no longer about asking the user to solve a cognitive puzzle, but about analyzing how the user interacted with the environment. It shifted from verifying ability (being able to read a text) to verifying behavior (moving and navigating like a human).
Today, we have reached version 3 of these systems, which is completely invisible. There is no longer any checkbox to tick. The system works in the background, constantly monitoring user interactions with the entire web page (scrolling, clicks, time spent) and returning a score to the site owner from 0.0 (definitely a bot) to 1.0 (definitely a human). It is the triumph of passive behavioral analysis .
The impact on companies and the defense of the digital perimeter
This technology is not a mere engineering exercise, but a vital necessity for the digital economy. Every day, the web is swept by billions of malicious bots. Some try to force user passwords (credential stuffing), others try to exhaust the inventory of limited edition products (scalping bots), and still others scrape sensitive data from websites (scraping).
For any company, from large multinationals to small, newly launched startups , protecting their public interfaces from this automated traffic is critical. An unmitigated bot attack can lead to server collapse, compromised customer data, and incalculable economic damage. Humanity verification systems act as a silent, tireless bouncer, capable of distinguishing legitimate customers from hostile scripts in fractions of a second, ensuring that server resources are dedicated only to real users.
The delicate balance between security and privacy.
Of course, this deep behavioral analysis raises legitimate questions about privacy. In order to distinguish a human from a bot with a high degree of accuracy, the companies providing these security services must collect and analyze a vast amount of personal and behavioral data. The paradox of modern security is that, in order to protect the user from fraud, the system must first “spy” on them to confirm their biological identity.
International regulations, such as the GDPR in Europe, are attempting to regulate this aspect by imposing transparency on the use of cookies and the data collected for security purposes. However, the line between what is strictly necessary to prevent cyberattacks and what constitutes excessive user profiling remains one of the most debated legal and ethical challenges in today’s technological landscape.
In Brief (TL;DR)
Simply clicking on the security box is an illusion, as reCAPTCHA analyzes biomechanical imperfections and the exact trajectory of your mouse.
A sophisticated analysis engine silently evaluates your digital fingerprint, examining your history, cookies, and your entire browser environment.
Moving beyond outdated, easily manipulated texts, modern security leverages artificial intelligence for in-depth behavioral analysis capable of unmasking any automated software.
Conclusions

The next time you encounter the “I’m not a robot” box, you’ll know that your click is just the final act of a complex digital symphony. You’re not just checking a box; you’re providing an artificial intelligence with a sample of your biomechanical behavior, proof of your browsing history, and your device’s fingerprint.
The illusion of the click is perhaps one of the most fascinating psychological compromises of the modern web: it offers the user a simple and reassuring action to perform, while hiding under the hood an infrastructure of surveillance and analysis of astonishing complexity. In an age where machines are becoming increasingly adept at mimicking human intelligence, the true test of our humanity no longer lies in our ability to solve problems, but in our imperfections, our tremors, and our unique, chaotic digital fingerprint.
Frequently Asked Questions

The system does not evaluate a simple click, but analyzes human behavior before and during navigation. It measures imperfections in mouse movement, such as tremors and speed variations, which characterize people compared to the artificial precision of bots. In addition, it examines web history and browser data to confirm your biological identity.
This verification is essential to protect digital platforms from automated cyberattacks. Security systems block malicious software that attempts to steal passwords, deplete limited edition products, or steal sensitive data. In this way, companies ensure that server resources are used exclusively by real and legitimate users.
The analysis engine examines various pieces of information to create a true digital fingerprint of the device. It checks your IP address, operating system, screen resolution, and the presence of cookies. If you have an active and credible browsing history, the system will easily recognize you as human; otherwise, it may require additional visual tests.
The third version of this security tool operates completely in the background without requiring any direct interaction. It constantly monitors actions on the web page, such as scrolling and dwell times, assigning a reliability score. This approach based on passive behavioral analysis eliminates the need to solve annoying visual puzzles.
Tests based on reading blurred text have been passed because modern artificial intelligence has become more skilled than humans at deciphering them. Cybersecurity has therefore changed its strategy, moving from verifying cognitive abilities to analyzing physical movements and browsing habits. These elements are much more difficult for an automated program to fake.
Still have doubts about The truth about reCAPTCHA: why your click is just an illusion?
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading








Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.