All of us do it dozens, perhaps hundreds of times a week. We open a website from our smartphone or computer to read urgent news, look for a recipe, or check the price of a product, and we are immediately blocked . A wall of text, often accompanied by brightly colored buttons, prevents us from accessing the content we want. It’s the infamous Cookie Banner , the digital entity with which, willingly or unwillingly, we interact most often in our online lives. Driven by haste, habit, and the desire to immediately get what we are looking for, our finger automatically snaps to the most obvious button, usually labeled “Accept all” or “I agree.” The annoyance disappears instantly, the page unlocks, and we continue our browsing, convinced that we have simply overcome a boring bureaucratic obstacle. But have you ever wondered what the real price of that single, hasty click is? Behind that apparent formality lies a technological and economic ecosystem of colossal proportions, a silent mechanism that transforms our impatience into one of the most precious and traded currencies of the twenty-first century.
The psychological engineering behind the obstacle: Dark Patterns
To fully understand the phenomenon, we must first analyze why we click so easily. It’s not just laziness, but the result of careful psychological design known in the world of interface design as Dark Patterns . Those who design these alerts know perfectly well that the average user has a very low attention span and a specific goal in mind when they land on a web page. Any element that stands between the user and their goal is perceived as a strong disturbance.
Dark Patterns exploit our “decision fatigue.” The “accept all” button is almost always large, positioned in an area easily reachable by the thumb (if on mobile), and colored with reassuring and inviting hues, such as green or blue. In contrast, options to refuse or customize choices are often written in small print, hidden behind gray text links on a light gray background, or require navigating through complex submenus and dozens of switches to be manually deactivated. This visual and functional imbalance is not a design error but a deliberate strategy to make refusal a cognitively expensive and time-consuming operation. The blackmail of haste is based precisely on this: I give you back your time and your smooth browsing experience, but in return, I demand your unconditional consent.
What happens in the millisecond after the click
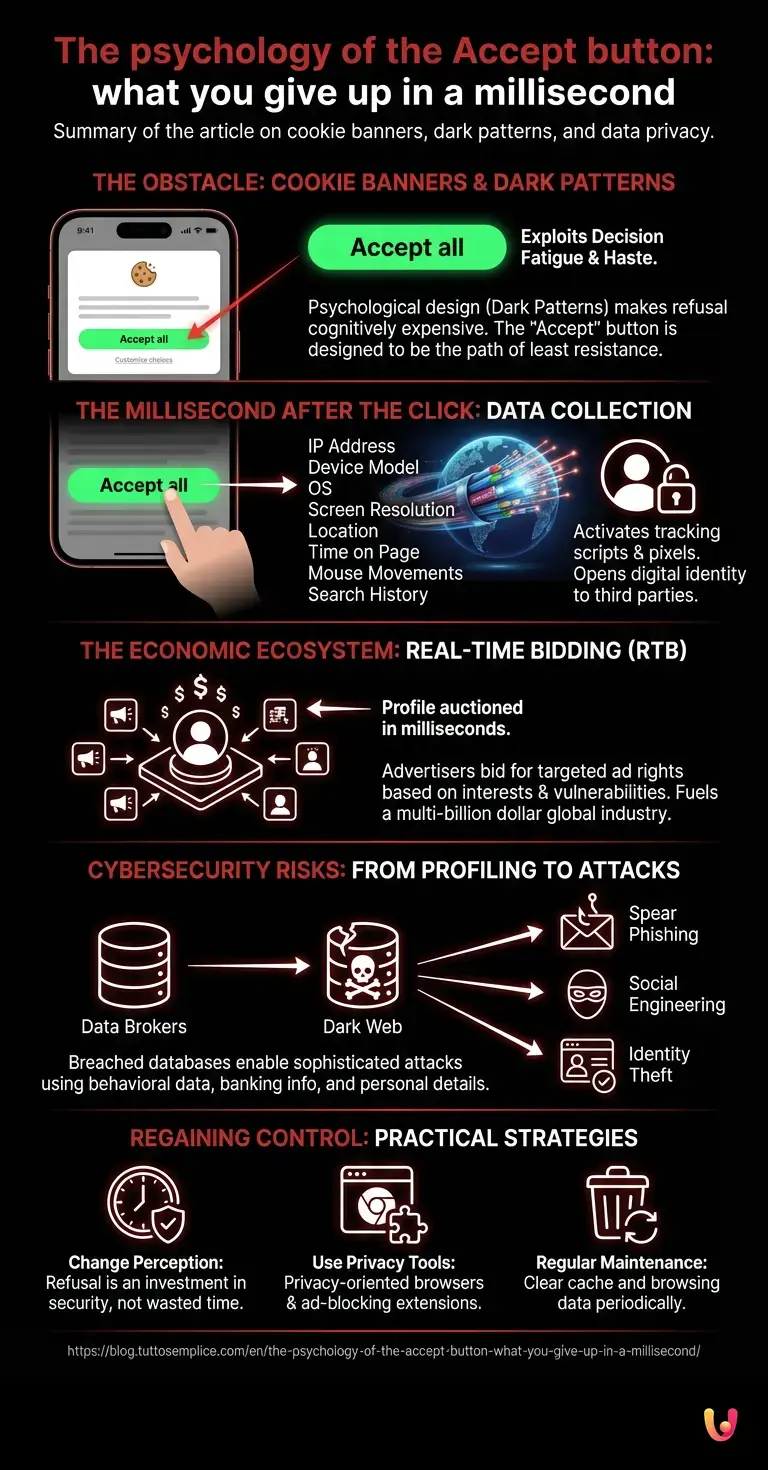
The exact moment your fingertip touches the “Accept All” button, an invisible chain reaction is triggered, traveling at the speed of light through fiber optic cables halfway around the world. We’re not just telling the website, “Okay, remember I was here.” We’re literally opening the doors of our digital identity to dozens, sometimes hundreds, of third-party companies we’ve never even heard of.
Technically, our consent activates a series of tracking scripts and pixels. These small pieces of code begin to collect an impressive amount of metadata: our IP address, the exact model of the device we are using, the operating system, the screen resolution, our approximate geographical location, the time we spend on the page, mouse movements , and, of course, our search history and previously visited pages. All this information is packaged into an anonymized (but highly specific) user profile and instantly sent to data exchange platforms.
This is where a mechanism called Real-Time Bidding (RTB) comes into play. In a fraction of a second, while the web page finishes loading on our screen, our profile is put up for auction. Advertisers make automatic bids to secure the right to show us targeted advertising, based exactly on our interests, our vulnerabilities, or our latent desires, deduced from the data just collected. Our haste has just fueled a global industry worth hundreds of billions of dollars.
From profiling to cybersecurity risks

Many users tend to downplay the problem, adopting the classic “I have nothing to hide, let them show me targeted ads” mentality. However, the issue goes far beyond simple marketing. The massive and uncontrolled accumulation of personal data by third parties (so-called Data Brokers) represents one of the most critical challenges for modern cybersecurity .
The databases of these companies, which aggregate billions of detailed profiles, are high-value targets for cybercriminals. When one of these databases is breached (an unfortunately increasingly frequent event), our behavioral data ends up on the Dark Web. Here, the information collected through our hasty consents is not used to sell us a pair of shoes, but to orchestrate extremely sophisticated social engineering attacks.
Personal cybersecurity is compromised when an attacker knows our browsing habits, the banks we use, the symptoms of diseases we have searched for, or our political preferences. This information allows for the creation of highly personalized phishing campaigns (spear phishing), where the bait is so credible and contextualized that it can deceive even the most experienced user. Today’s hasty click could turn into tomorrow’s critical vulnerability, providing hackers with the missing pieces to steal our identity or access our accounts.
The data market and the new frontiers of defense
The entire infrastructure of modern web technology has developed around this model of monetizing attention and data . However, awareness is slowly growing. International regulations, such as GDPR in Europe, have tried to curb the phenomenon by imposing transparency, but as we have seen, the industry has responded by refining psychological persuasion techniques.
In this scenario of constant digital cat-and-mouse, we are witnessing a real wave of privacy-oriented digital innovation . Several startups are developing advanced technological solutions to combat the blackmail of haste on equal terms. We are talking about AI-based browser extensions that can automatically read, interpret, and reject all non-essential background tracking, without the user having to lift a finger or waste a second of their time. These technologies act as a personal digital lawyer, negotiating terms of service in milliseconds while we enjoy uninterrupted browsing.
Furthermore, major browsers are beginning to integrate increasingly aggressive tracking-blocking systems, shifting the paradigm from a web based on explicit (often coerced) consent to a web where privacy is the default setting (Privacy by Design). It is a full-blown technological battle between those who seek to extract value from our data and those who build shields to protect it.
How to regain control without wasting time
While we wait for technology to fully automate our defense, there are practical strategies to avoid giving in to the blackmail of haste. The first rule is to change your perception: those three seconds needed to find the “Reject all” or “Technical cookies only” button are not wasted time, but a direct investment in your security and privacy. Many sites, to comply with the latest privacy regulations, are finally placing the global rejection button at the same visual level as the acceptance button.
Another fundamental habit is to use privacy-oriented browsers or install reliable extensions that block trackers upstream, often making interaction with the notice itself unnecessary. Finally, it is good practice to regularly clear your device’s cache and browsing data to periodically reset the digital identity that various advertising networks painstakingly try to build on us.
In Brief (TL;DR)
Cookie banners use psychological dark patterns to exploit our haste and instinctively push us to click the accept button.
Hasty consent triggers a massive collection of personal data, which is immediately sold through digital auctions to finance highly targeted advertising campaigns.
In addition to invasive marketing, this uncontrolled accumulation of sensitive information at third-party companies exposes users to very serious cybersecurity risks.
Conclusions

The blackmail of haste is perhaps the most striking example of how the modern digital economy exploits the vulnerabilities of human psychology. That annoying banner that blocks our reading is not a simple technical obstacle, but a real binding contract that we sign dozens of times a day without reading its clauses. The real price we pay to make that notice disappear is not measured in money, but in fragments of our identity, our privacy and, ultimately, our security. Developing awareness of what happens behind the scenes is the first, fundamental step to stop being the unwitting commodity of the web and to regain control of our digital space. The next time you find yourself in front of that wall of gray text, take a deep breath, invest three seconds of your time and look for the button to refuse: your future self will thank you.
Frequently Asked Questions

Dark patterns are psychological design strategies used to manipulate users. In cookie banners, they exploit decision fatigue by highlighting the accept button with bright colors while hiding options to refuse tracking. This makes refusal a long and arduous process, pushing people to give up their data out of haste.
By clicking the accept button, tracking scripts and pixels are activated, which immediately collect your metadata, such as geographic location and browsing history. This information creates a specific user profile that is sold through real-time auctions to advertisers. In a fraction of a second, your digital identity is shared with dozens of third-party companies.
The massive collection of personal data by third-party companies creates huge databases that often become the target of cybercriminals. If this information ends up on the digital black market, hackers can use it to create highly personalized phishing attacks. By knowing your browsing habits and interests, scammers can more easily trick you and steal your identity or access your bank accounts.
To quickly protect your data, it is advisable to use privacy-oriented browsers or install specific extensions that automatically block tracking. In addition, many recent regulations require websites to include a clearly visible global opt-out button. Taking a few seconds to look for the opt-out option and regularly clearing your device’s memory are fundamental habits for protecting your digital identity.
The real-time bidding mechanism comes into play the moment a web page loads on your screen. Your behavioral profile is put up for sale, and advertisers make automatic bids to show you targeted ads based on your interests. This system transforms your browsing data into a highly valuable commodity for the global advertising market.
Still have doubts about The psychology of the Accept button: what you give up in a millisecond?
Type your specific question here to instantly find the official reply from Google.







Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.