Picture the scene: you have just landed after a long business flight or at the start of your well-deserved vacation. You pick up the keys at the car rental counter, head to the parking lot, open the door, and take your seat behind the wheel. Even before fastening your seatbelt or adjusting the mirrors, you perform a gesture that feels entirely natural—almost like an involuntary reflex. It is a modern ritual, an automatic action dictated by our deep reliance on connectivity. Yet, at that very moment, you are entrusting your most intimate secrets to the infotainment system of a vehicle that does not belong to you and that, within a few days, will pass into the hands of complete strangers.
This seemingly harmless act, driven by the pursuit of maximum convenience, now represents one of the most overlooked vulnerabilities in the management of our personal privacy. In an era where we protect our smartphones with facial recognition, fingerprints, and complex passwords, we paradoxically tend to let our guard down precisely when we are inside a vehicle. But what actually happens when we connect our device to the car? And why are security experts sounding increasingly urgent alarms regarding this practice?
The Illusion of Convenience: What Happens Behind the Scenes
The ritual almost always begins with a prompt on the dashboard screen or our phone display: “Do you want to pair this device?” Another question immediately follows—the crucial one: “Do you want to allow access to your contacts and call history?” Most drivers, eager to start their favorite playlist or answer calls hands-free while driving, absentmindedly tap “Allow” without a second thought.
At that moment, a specific Bluetooth protocol known as PBAP (Phone Book Access Protocol) is activated. The technology underlying this standard is designed to rapidly download the entire phonebook , the log of incoming and outgoing calls, and—in many cases—even SMS and messages from major messaging apps directly into the car’s internal memory. This is not merely a temporary read operation: the data is physically copied and stored on the vehicle’s hard drive or flash memory to ensure quick access to the information whenever the phone reconnects.
The fundamental problem is that modern automobiles are no longer merely mechanical modes of transportation; they are, for all intents and purposes, computers on wheels, equipped with processing and storage capabilities comparable to those of a mid-range laptop. When you return the rental car, grab your suitcases, and walk away, your data remains there, silently stored in the dashboard, waiting for the next driver.
The invisible treasure left on the dashboard
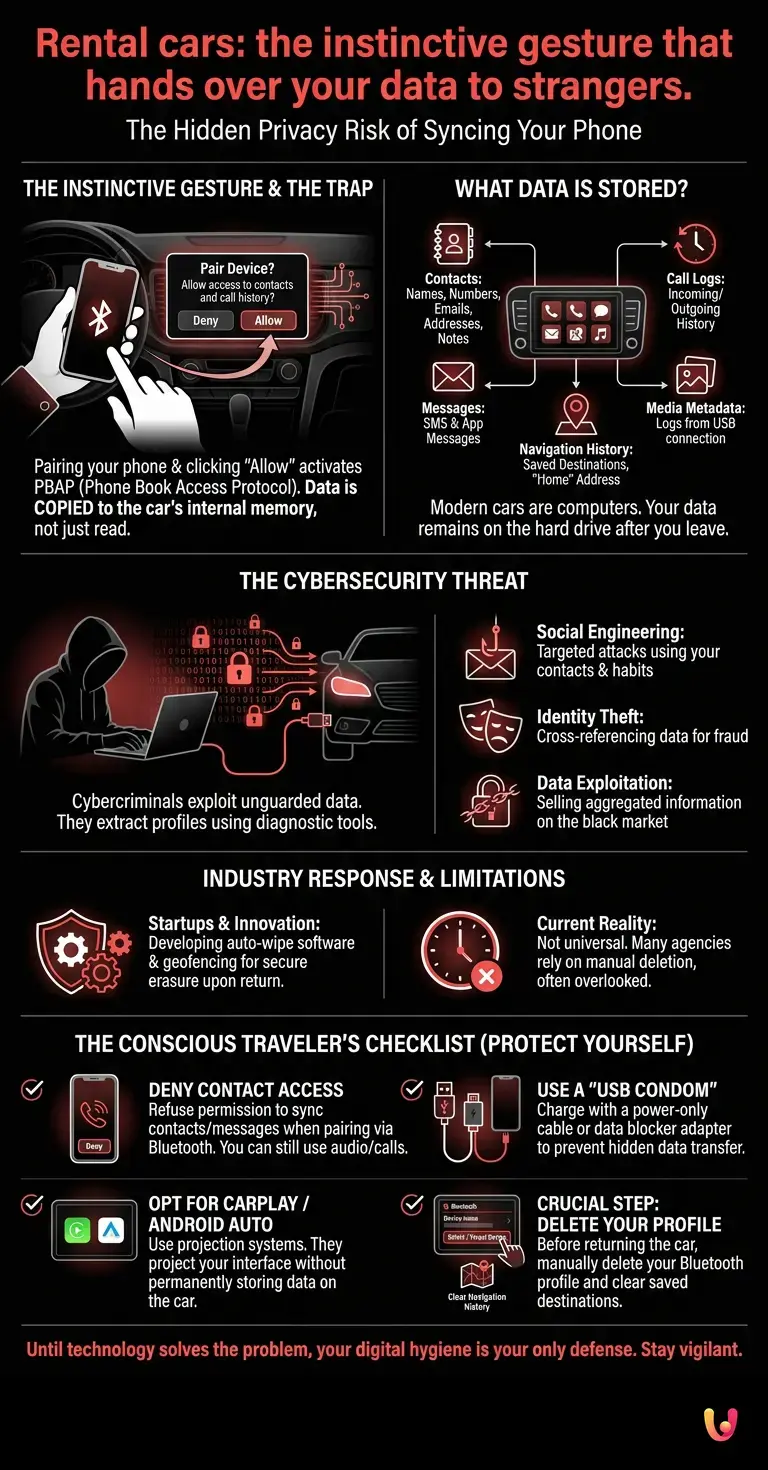
To understand the gravity of this carelessness, we must analyze the nature of the information we leave behind. It is not just a matter of phone numbers. An integrated navigation system, for example, accurately stores your travel history. If you have set the navigator to return to your hotel, or worse, if you rented the car in your own city and saved your address under “Home,” you have just provided a stranger with the exact coordinates of your residence.
Then there is contact information. In modern address books, a contact is not just a name and a number. It often includes email addresses, birthdays, personal notes, physical addresses, and even family relationships (e.g., “Mom,” “Wife,” “Lawyer”). Leaving this information in a rental car is akin to forgetting your wallet open on the passenger seat.
Furthermore, if you have used the vehicle’s USB port to charge your phone, you may have inadvertently authorized an even more extensive data transfer. Some older or aggressively configured systems attempt to index all media files on the device, creating logs and caches that remain hidden within the depths of the onboard software.
How cybercriminals exploit these lapses in attention
You might think: “Who would possibly care about my contact list? The next rental car customer will just ignore or delete it.” While this is true in most cases, the world of cybersecurity teaches us that aggregated data holds immense value on the black market. Cybercriminals are fully aware of this unguarded gold mine.
There are individuals who rent vehicles with the specific aim of extracting data from on-board systems. By using diagnostic software or simple hardware interfaces connected to the car’s USB or OBD-II (On-Board Diagnostics) ports, a malicious cybersecurity expert can download dozens of user profiles left behind by previous drivers in just a few minutes.
What do they do with this data? The applications are numerous, and all of them are harmful. The first is Social Engineering . By knowing your contacts, travel habits, and family members, scammers can orchestrate highly targeted and credible phishing attacks. They might send a message to your wife posing as you, or contact your colleagues with fraudulent requests, exploiting the inherent trust found in interpersonal relationships. Furthermore, cross-referencing this data with other information available online makes identity theft significantly easier.
The Role of Startups and Digital Innovation
Faced with this silent threat, the automotive industry and the tech sector are scrambling to take countermeasures. In recent years, digital innovation has led to the emergence of several startups specializing exclusively in data security within the automotive ecosystem.
These young companies are developing advanced software solutions for car rental fleets. The goal is to create systems that, upon the conclusion of the rental agreement, perform an automatic and irreversible “wipe” (secure erasure) of all user personal data as soon as the vehicle is registered as returned in the company’s management system. Some of these technologies utilize geofencing: when the car enters the agency’s parking lot, a wireless command resets the infotainment system to factory settings.
However, the adoption of these technologies is not yet universal. Many rental agencies, especially smaller ones or those operating in less regulated markets, still rely on the diligence of cleaning staff to manually delete Bluetooth profiles—a task that is systematically overlooked due to a lack of time or specific training.
How to Protect Yourself: The Conscious Traveler’s Checklist
Until technology resolves the problem at its root, the responsibility for data protection rests entirely with the user. Fortunately, avoiding this major mistake is simple, provided you practice rigorous digital hygiene. Here are the essential steps to follow every time you get into a rental car:
- Deny access to your contacts: When you connect your phone via Bluetooth to listen to music, the system will ask for permission to sync your contacts and messages. Refuse outright. You will still be able to play audio and answer calls, but you will see only the number on the car’s display instead of the contact’s name. A small price to pay for your privacy.
- Use a “USB Condom”: If you need to charge your phone via your car’s USB port, use a “power-only” cable (which does not transmit data) or an adapter known in industry jargon as a “USB condom .” This small device blocks the data pins of the USB port, allowing only electrical current to pass through and preventing any hidden file transfers.
- Opt for Apple CarPlay or Android Auto: If your car supports them, use these projection systems. Unlike the car’s native Bluetooth connection, CarPlay and Android Auto project your phone’s interface onto the screen without permanently transferring data to the vehicle’s hard drive. When you unplug the cable or disconnect the wireless connection, your data goes with you.
- The crucial step: delete your profile. If you had to synchronize your data, or if you did so by mistake, take two minutes before handing back the keys. Go to the Bluetooth settings on the infotainment system, find your device, select “Delete” or “Forget device,” and make sure to also clear any destinations saved in the satellite navigation system.
In Brief (TL;DR)
Connecting your smartphone to a rental car to listen to music or make calls is a common practice that conceals serious risks to personal privacy.
By accepting synchronization, on-board systems copy and store your contact list, messages, and GPS history, making this information available to future drivers.
Cybercriminals exploit these oversights to easily extract personal data stored in vehicles, reselling it or using it for illicit purposes on the black market.
Conclusions

The ritual of connecting one’s smartphone to a rental car is emblematic of how technological convenience can often blind our common sense regarding privacy. In a hyper-connected world, our personal data is our most precious currency and, at the same time, our most coveted target. Leaving your contact list, messages, and travel history at the mercy of the next driver is a risk that no one should take.
Awareness is the first and most effective line of defense. Taking simple precautions—such as declining automatic synchronization or remembering to delete your profile before finally exiting the vehicle—takes only a few seconds, yet provides invaluable protection against invisible but extremely real threats. The next time you take the driver’s seat of a rental car, remember: the journey truly begins only when your data is secure.
Frequently Asked Questions

When you connect your phone via Bluetooth, the system downloads and stores your contacts, call logs, and messages in the vehicle’s internal memory. This information remains stored in the onboard computer even after the car is returned, becoming accessible to the strangers who drive it next.
To protect your information, you must deny the multimedia system permission to synchronize contacts when connecting via Bluetooth. Furthermore, it is advisable to use temporary screen projection systems and always remember to manually delete your profile from the settings before returning the keys to the staff.
These systems simply project your device’s screen onto the dashboard monitor without transferring or permanently saving files to the vehicle’s hard drive. As soon as you disconnect the cable or terminate the wireless connection, all your personal information immediately disappears from the vehicle’s memory.
Cybercriminals can easily extract your data from your dashboard to orchestrate targeted scams and cyberattacks. By knowing your movements, your family members’ phone numbers, and your habits, malicious actors can exploit this information for identity theft or to deceive your professional and personal contacts.
The safest method is to use a cable that transmits only electrical power, or a specialized adapter that blocks the data transfer contacts of the USB port. This measure prevents the device’s software from analyzing media files and creating hidden copies of your personal information while the battery is charging.
Still have doubts about Rental cars: the instinctive gesture that hands over your data to strangers.?
Type your specific question here to instantly find the official reply from Google.







Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.