We walk the streets of our cities, pass through crowded airports, and sit in cafés, convinced that we are enveloped in a comforting anonymity. We assume that, unless we actively post our location on social media, our movements remain a private matter. Yet, at this very moment, the device in our pocket is literally broadcasting the history of our past travels to the world. The culprit behind this silent data hemorrhage has a precise technical name: the Wi-Fi Probe Request . This mechanism, built into almost all modern devices, is the invisible signal that reveals your past travels, your habits, and, in some cases, even your most intimate secrets to strangers.
The Illusion of Digital Anonymity
Most users believe that to protect their privacy, it is sufficient to disable GPS geolocation or deny tracking permissions to individual applications. This is one of the greatest illusions of the modern era. The technology we use daily is designed to be convenient first and foremost, and secure only secondarily. Our smartphones are programmed to make our lives easier: they aim to connect to the internet as quickly as possible the moment we enter our homes, offices, or favorite cafés. To do so, they do not passively wait for a network to appear, but instead act proactively. This is where a fundamental dynamic comes into play—one that often eludes even the most privacy-conscious users.
The Anatomy of a Signal: How Network Searching Works
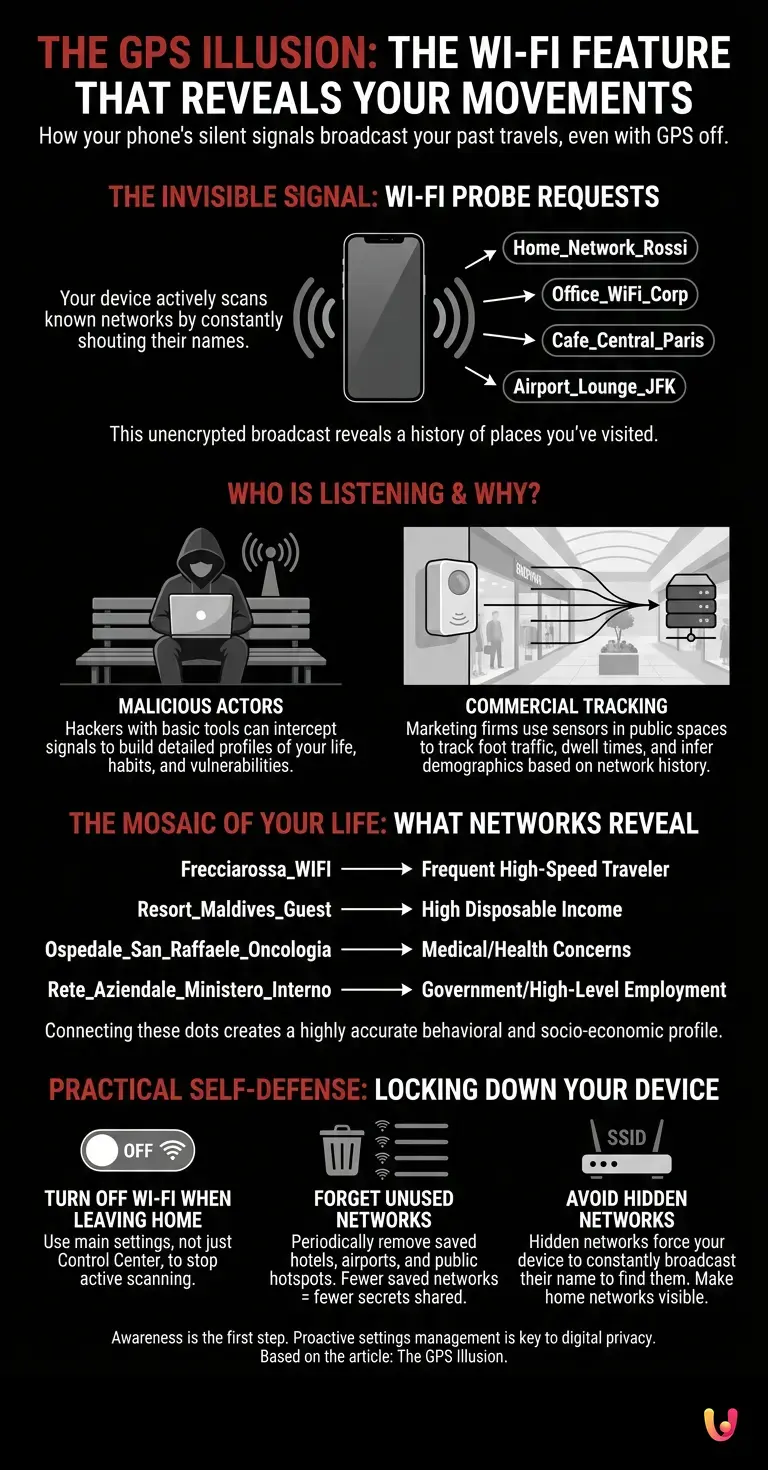
To fully understand this vulnerability, we must ask ourselves: how exactly does our phone’s wireless connection work? When Wi-Fi is enabled but not connected to any network (for example, while we are walking down the street), the device uses an active scanning protocol. In practice, the phone continuously sends unencrypted data packets into the air, known as Wi-Fi Probe Requests. These packets contain a very simple question addressed to the surrounding environment: “Is the ‘Casa_Rossi’ network nearby, by any chance? What about the ‘Hotel_Hilton_Roma’ network? Or perhaps ‘Starbucks_JFK_Airport’?”
Your phone cycles through the entire list of networks you have connected to in the past and calls them out by name, one by one, dozens of times a minute. This happens because hidden networks—those that do not publicly broadcast their names—can only be detected if the device calls out to them first. Consequently, to ensure you can connect instantly to your office’s hidden network, your phone broadcasts in plain text a list of almost every place you have visited and for which you have saved a password.
The Signal Hunter: Who Listens and Why
What happens if someone decides to start listening? In the vast and complex world of cybersecurity , intercepting these signals is a trivial task. It requires neither equipment worth millions of euros nor the skills of a government hacker. Any computer science student with a laptop costing a few hundred euros, a compatible network card, and free “packet sniffing” software (such as Wireshark) can sit on a bench and capture all the Probe Requests emitted by the phones of passersby within a radius of tens of meters.
But it is not just malicious actors who are listening. In recent years, various startups and marketing firms have developed commercial sensors based on this exact principle. These sensors are installed in shopping malls, on shopping streets, and in airports. Their purpose? To track the flow of people. Even though they do not know your full name, by picking up your phone’s unique signal (the MAC address) and the networks you search for, they can determine how long you linger in front of a shop window, whether you are a regular customer, and—by cross-referencing the names of the networks your phone seeks—they can even deduce your income bracket or geographic origin.
The Mosaic of Your Life: What Network Names Reveal
Let’s look at a practical example to understand the severity of the situation. Imagine that a cybersecurity analyst intercepts your smartphone’s Probe Requests while you are waiting for the bus. Your phone transmits the following list of network names (SSIDs): “Frecciarossa_WIFI”, “Resort_Maldives_Guest”, “Ospedale_San_Raffaele_Oncologia”, “Rete_Aziendale_Ministero_Interno” .
Without ever having seen your face or known your name, a stranger has just discovered that: you frequently travel by high-speed train, you have the financial means to afford vacations in the Maldives, you or a loved one have had dealings with an oncology department at a specific hospital, and you likely work for a high-level government agency. By connecting these dots, a malicious actor can create an extremely accurate profile of your private life, your habits, your medical vulnerabilities, and your socio-economic status. It is a level of psychological and behavioral profiling that makes traditional website cookies pale in comparison.
Industry Countermeasures and Digital Innovation
Faced with this blatant violation of structural privacy, digital innovation has sought to take corrective action. In recent years, tech giants such as Apple and Google have introduced a feature called “MAC Randomization.” In practice, when your phone sends out these search requests, it uses a fake, temporary identifier address, changing it frequently. This prevents retailers from tracking your physical movements from one day to the next using your phone’s hardware identifier.
However, this solution addresses only half of the problem. Although the phone’s identifier is masked, the network names (SSIDs) that the phone continues to broadcast often remain in plain text. If your phone keeps shouting “Mario_Rossi_Home_Network_Via_Roma_10,” the fact that it is using a fake identifier becomes irrelevant: the very content of the message reveals your identity and location. Furthermore, many older devices or IoT (Internet of Things) devices, such as smartwatches and tablets, do not correctly implement these safeguards, leaving them completely exposed.
Practical Guide to Self-Defense
How can we defend ourselves against this invisible data leak? Awareness is the first step, but practical action is required. Here are the golden rules for locking down your device:
1. Turn off Wi-Fi when leaving the house: This is the simplest and most effective solution. If you do not need to connect to a wireless network, disable the Wi-Fi antenna via the settings menu (note: on modern iPhones, disabling it from the Control Center only pauses it; you must turn it off in General Settings).
2. Clean up saved networks: Periodically, go into your phone’s Wi-Fi settings and select “Forget this network” for all the hotels, airports, restaurants, and public networks you have connected to in the past but do not use on a daily basis. The fewer networks your phone remembers, the fewer secrets it will have to share.
3. Avoid hidden networks: If you are setting up your home Wi-Fi network, do not hide the network name (SSID). Contrary to what was previously thought, hiding the network does not increase security; instead, it forces your devices to broadcast your network name wherever you go in the world in an attempt to find it.
In Brief (TL;DR)
Even if you turn off GPS, your smartphone continuously broadcasts the names of the Wi-Fi networks you have connected to in the past.
These invisible signals, called Probe Requests, can be easily intercepted by hackers or marketing companies to track your daily movements.
By analyzing the list of your past connections, anyone can reconstruct an incredibly detailed profile of your habits, revealing your most intimate secrets.
Conclusions

We live in an era where our devices are extensions of our minds and memories. The invisible signal of Wi-Fi Probe Requests is the perfect example of how technological convenience can turn into a double-edged sword against our privacy. It is not a matter of succumbing to paranoia, but of developing healthy digital hygiene. Understanding the invisible mechanisms that govern our smartphones restores our control over our data. The next time you walk down the street, remember that your phone is a tireless chatterbox: it is up to you to decide when it is time to silence it.
Frequently Asked Questions

This is an invisible signal that your smartphone continuously broadcasts to the surrounding area to search for wireless networks you have connected to in the past. This automatic mechanism is designed to ensure a quick connection, but it transmits the names of all the places you have visited in plain text. Consequently, anyone listening can track your habits and movements without using GPS.
Many users believe that turning off geolocation is sufficient, but modern devices continue to reveal their location by scanning for wireless networks. Even without GPS, the phone publicly broadcasts the networks saved in its memory, allowing malicious actors or marketing companies to deduce your movements and create a detailed behavioral profile.
Anyone with a laptop and free network analysis software can intercept the signals emitted by your phone as you walk down the street. By capturing the names of the networks your device automatically searches for, a stranger can discover which hospitals, hotels, or businesses you frequent. This makes it easy to deduce your lifestyle, income bracket, and personal vulnerabilities.
MAC address randomization is a security feature introduced by Apple and Google that assigns a fake, temporary identifier to your phone while it searches for networks. However, this measure only partially addresses the privacy issue. If the device continues to broadcast the specific names of saved networks, the content of the message itself will still reveal your identity and the places you habitually frequent.
To protect your data, it is essential to completely turn off the Wi-Fi connection via your phone’s main settings when leaving home. Furthermore, it is imperative to periodically remove public networks saved in memory by using the “forget network” feature. Finally, setting up hidden home networks is strongly discouraged, as they force your device to broadcast their name wherever you go.
Still have doubts about The GPS Illusion: The Wi-Fi Feature That Reveals Your Movements?
Type your specific question here to instantly find the official reply from Google.






Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.