Picture the scene: it is the dead of night, the house is silent, and you are fast asleep. Outside, in the driveway or parked along the street, your car sits at rest, seemingly safe. The doors are locked, and the alarm is set. Yet, at this very moment, a trivial mistake you make every evening is about to cost you dearly. The object in question lies just a few centimeters away from you, resting innocently on your nightstand or bedroom shelf: it is your keyless entry fob . This compact marvel of convenience, designed to unlock your doors without you even having to take it out of your pocket, has become the primary target of a new generation of car thieves. But how is it possible for an object inside your home, meters away from the vehicle, to unlock the doors of a car parked outside?
The Illusion of Home Security
For decades, we have been accustomed to thinking of security in physical terms: thick walls, armored doors, and complex locks. When we lock our front door, we feel protected. However, modern technology operates on an invisible plane, consisting of radio waves and frequencies that recognize no traditional physical obstacles. Leaving your car keys on the nightstand—especially if your bedroom faces the street or is located above the garage—creates an invisible bridge between the interior of your home and the outside world .
The problem stems from the very nature of smart entry systems. These devices are constantly listening, ready to pick up the vehicle’s signal to unlock the doors as soon as you approach. They do not require mechanical action, but instead rely on a continuous, silent dialogue between the vehicle and the key fob. It is precisely within this invisible conversation that one of the most sophisticated threats in modern automotive cybersecurity takes hold.
How the “Relay” Attack Works: The Physics of the Theft
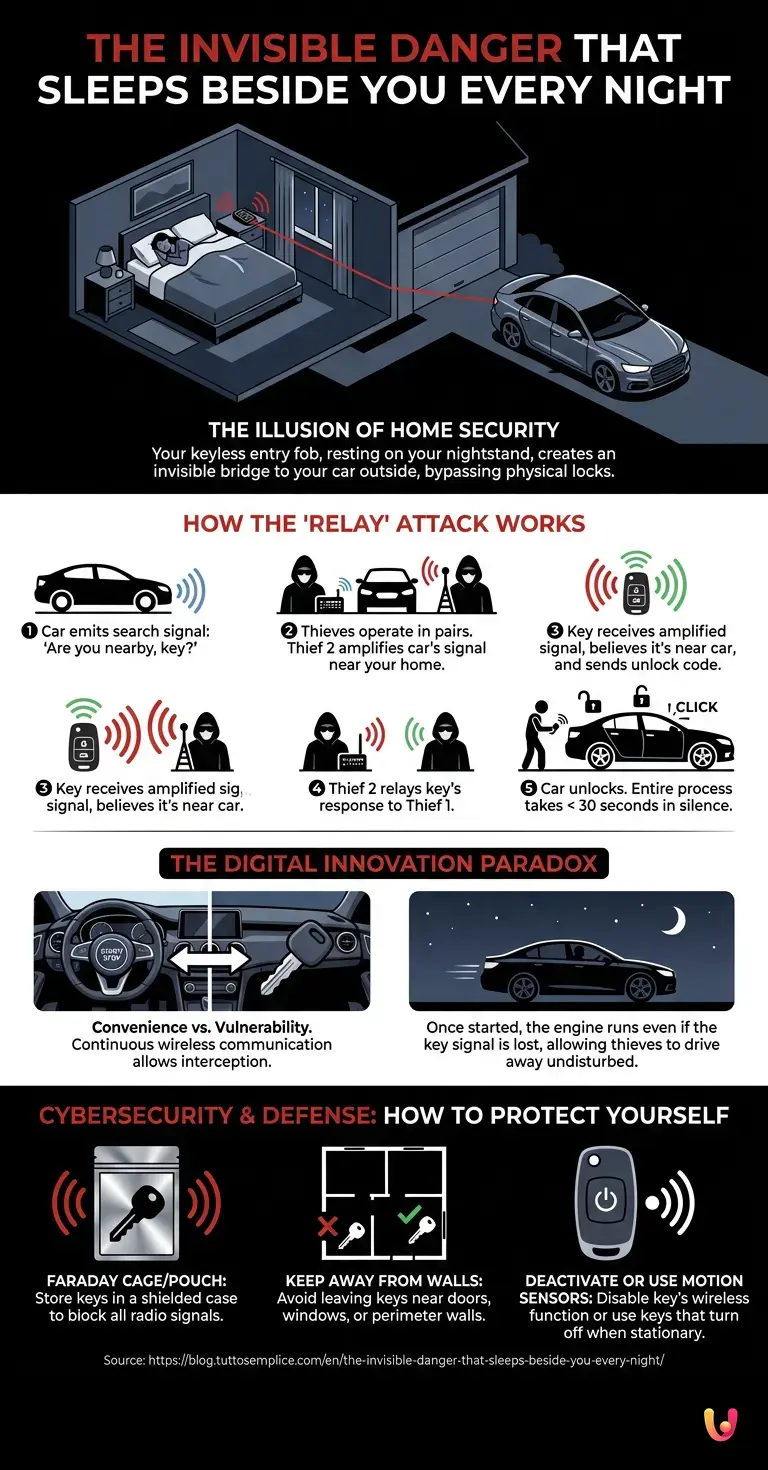
The method used by criminals to exploit this nightly habit is known as a “Relay Attack.” To understand how it works, we must delve into the basic mechanisms of this technology. The car regularly emits a low-frequency signal—a sort of “ping”—asking: “Are you nearby, key? ” If the key is within a range of a couple of meters, it responds with an ultra-high frequency (UHF) signal that authorizes the unlocking of the doors and the starting of the engine.
At night, thieves operate in pairs. The first perpetrator positions himself near the car with a transmitter device. The second stealthily approaches the exterior walls of your home—right near your bedroom or the entryway—holding an amplifying antenna. This second device picks up the weak search signal emitted by the car (via the accomplice) and amplifies it, causing it to penetrate the walls of the house until it reaches your nightstand.
Your key, unaware of the deception, receives the amplified signal. Believing that you are physically standing next to the door, it responds by sending the unlock code. The thief’s antenna near the house picks up this response and instantly transmits it to the accomplice near the car. Click. The doors unlock. The entire process takes less than thirty seconds, in absolute silence, with no broken glass or sounding alarms.
The Digital Innovation Paradox

Digital innovation has transformed our vehicles into veritable computers on wheels, offering levels of comfort unimaginable just a decade ago. However, this very convenience has introduced new and concerning vulnerabilities. The automotive sector has suddenly found itself facing challenges that previously belonged exclusively to the world of information technology.
The convenience of not having to search for your keys in your bag while standing in the rain comes at a price: the continuous transmission of data. Whenever a wireless device is active and listening , there is a possibility that someone could intercept or manipulate that communication . It is the classic trade-off between usability and security. While car manufacturers work to implement increasingly complex cryptographic protocols, criminals are upgrading their equipment, which can often be purchased for a few hundred euros on unregulated online marketplaces.
What happens once you are on board?
The severity of this nighttime lapse is not limited to the unlocking of the doors. Modern keyless systems also control engine ignition via the “Start/Stop” button. Since the car believes the legitimate key is inside the cabin (thanks to the signal continuously relayed by the thieves), the criminal simply needs to press the button, shift into gear, and slip silently away into the night.
Once the engine is running, most vehicles will not shut off even if the key signal is lost. This is a safety mechanism designed to prevent a car from suddenly stalling on the highway should the remote key fob battery die. Thieves can then drive undisturbed to a safe hideout, where they will have ample time to dismantle the vehicle to resell its parts or reprogram the control unit with a new, blank key.
Cybersecurity and Defense: How to Protect Yourself
Fortunately, cybersecurity is not the exclusive domain of engineers and programmers; there are practical and immediate steps anyone can take to neutralize this threat. The solution to the problem of this bedside habit is surprisingly analog and is based on a physical principle discovered in the 19th century: the Faraday cage.
Storing your keys inside a shielded case (often called a Faraday pouch or RFID bag) completely blocks the transmission and reception of radio waves. When the key is enclosed in this container, it becomes invisible to thieves’ scanners, making relay attacks impossible. Many companies, and even a few innovative startups , have started producing stylish, designer boxes for home use that act as veritable safes for radio signals.
Other solutions include:
1. Keep keys away from perimeter walls: Avoid leaving keys near doors, windows , or on nightstands in rooms that face directly onto the parking area.
2. Deactivate the signal: Some car manufacturers now allow you to temporarily disable the key’s wireless function by pressing a specific combination of buttons.
3. Motion sensors: The latest generation of keys feature built-in accelerometers that disable radio transmission when the key remains motionless for a few minutes (for example, when placed on a nightstand).
In Brief (TL;DR)
Leaving your electronic car key on the nightstand overnight exposes your vehicle to a serious and silent risk of theft.
Criminals carry out a relay attack using signal-amplifying antennas to pick up the key’s signal through the walls of your home.
The smart entry system becomes a dangerous vulnerability, allowing criminals to start the engine and flee undisturbed in silence.
Conclusions

Technological convenience has accustomed us to taking our security for granted, leading us to perform automatic actions without considering their invisible consequences. The habit of emptying our pockets and leaving car keys on a nightstand or in the entryway is a relic of an era when keys were merely shaped pieces of metal. Today, we possess powerful and sophisticated radio transmitters that require a new level of awareness. Understanding the mechanisms by which this technology operates and the vulnerabilities that arise from it is the first, fundamental step toward protecting our belongings. A simple change to our evening routine—such as using a shielded pouch—is all it takes to sleep truly soundly and ensure that our car is still there waiting for us the next morning.
Frequently Asked Questions

Criminals use a technique called a relay attack to amplify the radio signal between the vehicle and the electronic key located inside a house. One thief positions themselves near the residence to capture the key’s signal, while an accomplice near the vehicle receives the transmission and unlocks the doors. This method allows them to open and start the car in a matter of seconds without forcing any locks.
Leaving the remote control near perimeter walls or windows allows criminals to easily intercept the radio frequencies emitted by the device. Thieves’ equipment can penetrate household walls and establish an invisible connection with the vehicle parked on the street. Placing the device away from the outer boundaries of the home drastically reduces the risk of interception.
Once the engine is started via the ignition button, most modern vehicles continue to run even if they lose radio contact with the original remote key. This feature was designed for road safety reasons, preventing sudden engine shutdowns while driving in the event of a dead battery. Criminals can therefore drive undisturbed to a safe location to dismantle the vehicle.
The most effective method is to place the remote control inside a shielded case, known as a Faraday cage, which is capable of completely blocking radio waves. Alternatively, it is possible to temporarily disable the device’s wireless function using a specific key combination. Furthermore, the latest models feature motion sensors that turn off transmission when the device remains stationary for a few minutes.
To isolate radio frequencies, it is advisable to use specialized pouches or boxes lined with metallic materials capable of creating an impenetrable barrier. These containers prevent criminals’ scanners from communicating with the vehicle’s remote control. Many companies offer elegantly designed solutions that can be conveniently kept in the home, serving as veritable safes for wireless signals.
Still have doubts about The invisible danger that sleeps beside you every night?
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading







Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.