There’s a very dangerous false myth that continues to circulate in 2026: believing that receiving a code via SMS protects you from hackers. The raw, counter-intuitive truth is that using SMS for two-factor authentication is almost as good as having no authentication at all. It offers a false sense of security that cybercriminals exploit daily through trivial but devastating techniques. If you’re still waiting for a text message to access your bank, email, or crypto wallets, you’re the easiest target on the net. It’s time to evolve.
Find out the security level of your accounts in real time based on the authentication method used.
Real-World Case Study: The Attack on the SEC (January 2024)
In January 2024, the X (formerly Twitter) account of the U.S. Securities and Exchange Commission (SEC) was compromised. Hackers posted a false announcement about the approval of Bitcoin ETFs, causing extreme volatility in the financial markets. The official investigation revealed that the attack occurred via SIM swapping and that the account had not enabled robust two-factor authentication. This case demonstrates how the absence of adequate cryptographic protocols can have catastrophic global consequences.
How the SIM Swapping Vulnerability Works
SMS-based two-factor authentication is weak because criminals can clone your phone card through SIM swapping. By deceiving the phone operator, they transfer your number to their own SIM, intercepting all access codes.
The fundamental problem with SMS is that they were not designed for cybersecurity . They are plain text messages that travel over cellular networks (SS7) known for their structural vulnerabilities. When you set up an SMS as a second factor, you are entrusting the security of your account to your phone operator's identity verification procedures, which are often based on call centers that can be easily manipulated through Social Engineering .
According to official documentation from NIST (National Institute of Standards and Technology), the use of SMS for two-factor authentication has been strongly discouraged (and deprecated) for several years. An attacker does not need to physically hack your phone; they just need to convince a complacent or distracted phone operator that they have lost their SIM card to have your number activated on a new card in their possession. From that moment on, every OTP (One-Time Password) code sent by your bank will go directly into the hands of the hacker.
App Authenticator compared for maximum security
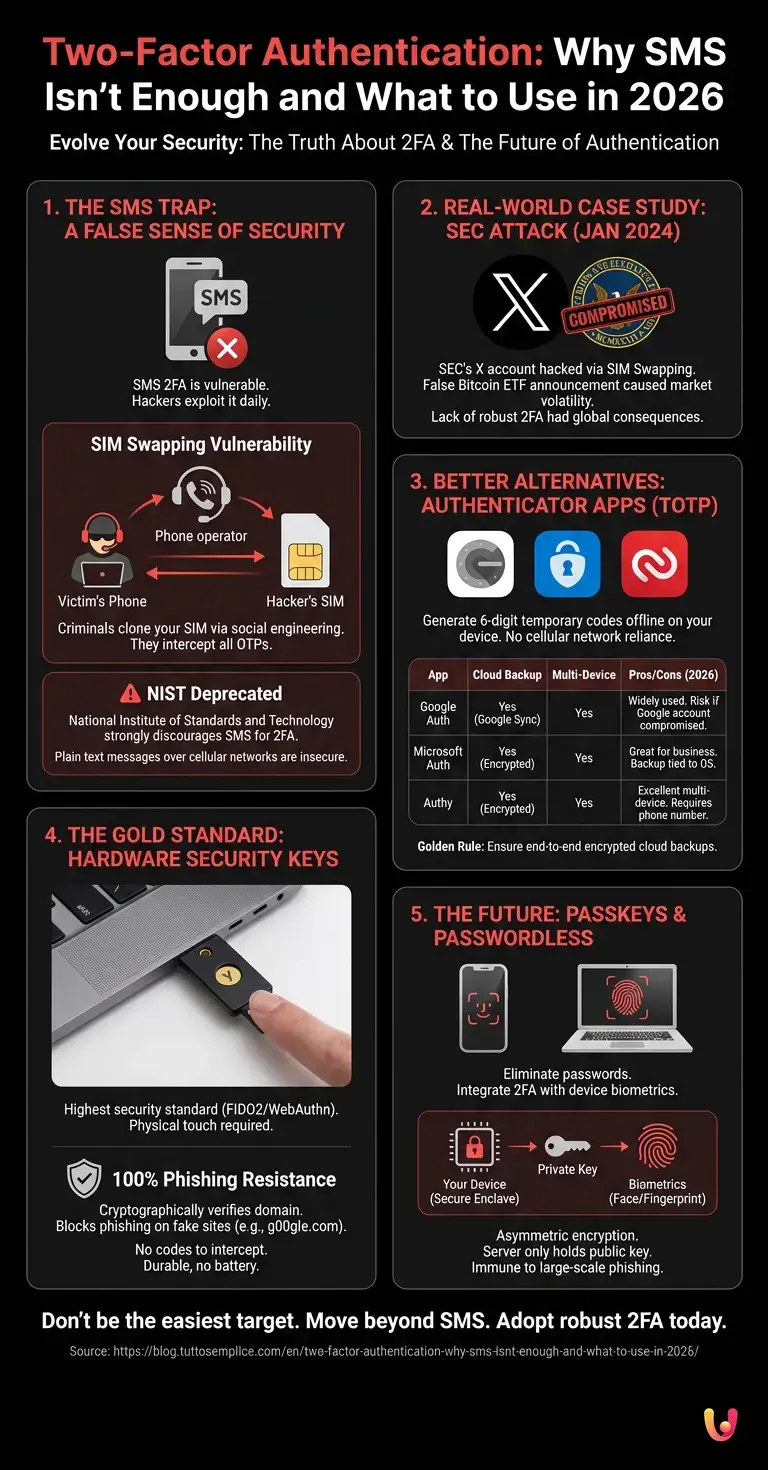
For robust two-factor authentication, Authenticator apps generate temporary codes locally on the device, without relying on the cellular network. Google Authenticator, Authy, and Microsoft Authenticator offer different levels of cloud backup and advanced security against interception.
The next logical step after abandoning SMS is to adopt an application based on the TOTP (Time-based One-Time Password) standard. These apps use a shared secret (the QR code you scan during setup) and your smartphone's internal clock to generate a 6-digit code that is valid for only 30 seconds. Since the generation happens offline, there is no message that can be intercepted in transit.
However, in 2026, not all apps are created equal. Here's a comparison of the most popular solutions:
| App Authenticator | Cloud Backup | Multi-Device | Pros and Cons (2026) |
|---|---|---|---|
| Google Authenticator | Yes (Google Account Sync) | Yes | Pros: Widely used, clean interface. Cons: If the Google account is compromised, the codes are at risk. |
| Microsoft Authenticator | Yes (Encrypted) | Yes | Pros: Excellent for the business ecosystem, supports push notifications. Cons: Backup is strictly tied to the OS (iOS/Android). |
| Authy (Twilio) | Yes (Encrypted with a local password) | Yes | Pros: Excellent multi-device management. Cons: Requires a phone number for initial registration. |
The best choice depends on your ecosystem, but the golden rule is to ensure that cloud backups of your TOTP codes are protected by end-to-end encryption , so that not even the app provider can read them.
Hardware security keys and advanced encryption

Hardware keys like YubiKey represent the highest standard for two-factor authentication. Based on asymmetric cryptography and FIDO2 protocols, they make phishing physically impossible as they require human touch on the device to authorize access.
While Authenticator apps solve the SIM Swapping problem, they do not solve the real-time Phishing (AiTM - Adversary-in-the-Middle) problem. If a hacker tricks you into entering the 6-digit code on a fake site, they can capture it and use it immediately on the real site. This is where hardware security keys like Yubico's YubiKey or Google's Titan Security Key come into play.
These small USB/NFC devices use the FIDO2 / WebAuthn standard. When you register a hardware key, a cryptographic key pair (public and private) is created. The private key never leaves the secure chip of the hardware device. During login, the browser cryptographically verifies that the domain you are on exactly matches the one registered. If you are on g00gle.com instead of google.com , the hardware key will simply refuse to provide the cryptographic signature, blocking the phishing attack at its root.
- Phishing Resistance: 100%. No code to type or intercept.
- Physical requirement: They require a physical touch on the capacitive sensor to confirm human presence, preventing automated remote attacks.
- Durability: They have no batteries, do not require an internet connection, and are water-resistant.
Passkeys and the future of passwordless authentication
In 2026, Passkeys are replacing traditional passwords, integrating two-factor authentication directly into the device's biometrics. Using the WebAuthn standard, they offer instant, encrypted access that is completely immune to large-scale phishing attacks.
The ultimate evolution of two-factor authentication is, paradoxically, the elimination of the password itself. Passkeys are the industry's answer (led by the FIDO Alliance, Apple, Google, and Microsoft) to the inherent weakness of human passwords.
A Passkey works with the exact same asymmetric encryption as hardware keys, but instead of residing on an external USB stick, it resides in the Secure Enclave (the security chip) of your smartphone or computer. When you log in to a service, the device asks you to unlock the Passkey using biometrics (Face ID, Touch ID, or Windows Hello).
In this scenario, two-factor authentication is intrinsic in a single gesture: 1. Something you possess: Your smartphone (which contains the encrypted private key). 2. Something you are: Your fingerprint or your face (necessary to unlock the use of the key).
Passkeys eliminate the very concept of credentials being stolen from company databases, as the server only stores the public key, which is useless to hackers without the corresponding private key stored on your device.
Conclusions

Maintaining SMS as a two-factor authentication method in 2026 is an unacceptable risk, comparable to leaving your front door unlocked with the key in the lock. SIM swapping and automated phishing have rendered old OTP codes obsolete. To protect your digital identity and financial assets, transitioning to Authenticator Apps is the absolute minimum requirement. However, for those seeking true peace of mind, adopting FIDO2 hardware keys or making the definitive transition to Passkeys represents the only impenetrable shield against modern cyber threats. Cybersecurity is no longer a matter of convenience, but of digital survival.
Frequently Asked Questions

Receiving the code on your phone exposes you to the risk of SIM swapping, a technique where criminals clone your SIM by deceiving the phone operator. Furthermore, text messages travel in plain text over vulnerable cellular networks, allowing hackers to easily intercept your banking or social media access codes.
This type of cyber fraud occurs when a malicious actor convinces your phone provider to transfer your number to a new SIM card in their possession. From that moment on, the criminal will receive all your temporary access codes, making it easy to breach your accounts that are only protected by traditional messaging.
The minimum recommended security level involves using dedicated applications like Google Authenticator or Authy, which generate temporary offline codes. For complete protection against online scams, the ideal choice is physical security keys or modern Passkeys, which link access to your device's biometrics.
These applications use a cryptographic standard to generate six-digit codes that are valid for only thirty seconds, working directly within the smartphone without the need for an internet connection. Since the generation takes place offline, there is no message in transit that a cybercriminal can intercept on the cellular network.
Passkeys represent the evolution of digital authentication because they completely eliminate the need to remember text-based credentials. They leverage a security chip integrated into your smartphone or computer and are unlocked solely through facial recognition or fingerprint scanning, making it physically impossible to steal data through fake websites.
Still have doubts about Two-Factor Authentication: Why SMS Isn't Enough and What to Use in 2026?
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading







Did you find this article helpful? Is there another topic you'd like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.