The most widespread myth about cybersecurity is that, in the event of a breach, simply changing your password is enough to immediately return to safety. The reality is brutally different and counter-intuitive: if cybercriminals have exfiltrated your session cookies, your tax code, or your identity card data, updating your credentials is a completely useless action. Your sensitive data now lives a life of its own in the depths of the network. To truly defend yourself, the first step is not to compulsively reset passwords, but to map the exact nature of the compromised information.
The Lifecycle of a Data Breach
To understand how to effectively verify a data breach, it is essential to know the breach lifecycle: from the initial exfiltration of data from company servers, through its sale on dark web forums, to its malicious use for fraud or identity theft.
When a company suffers a cyberattack, user data is not immediately used. The process follows a well-structured criminal chain, which is divided into three main phases:
- Infiltration and Exfiltration: Hackers exploit vulnerabilities (such as software flaws or social engineering attacks) to penetrate databases. Data is copied and exfiltrated to secure servers controlled by the attackers.
- Monetization on the Dark Web: Stolen databases (often called “dumps”) are put up for sale on clandestine forums. The buyers are other criminals specializing in specific frauds.
- Exploitation: The purchased data is used for Credential Stuffing attacks (testing the same credentials on thousands of sites), bank fraud, or highly targeted phishing campaigns (Spear Phishing).
Understanding this time latency is critical: months can pass between the moment a theft occurs and when the data is made public or used. That’s why proactive monitoring is the only real defense.
How to Check if You’ve Been Involved
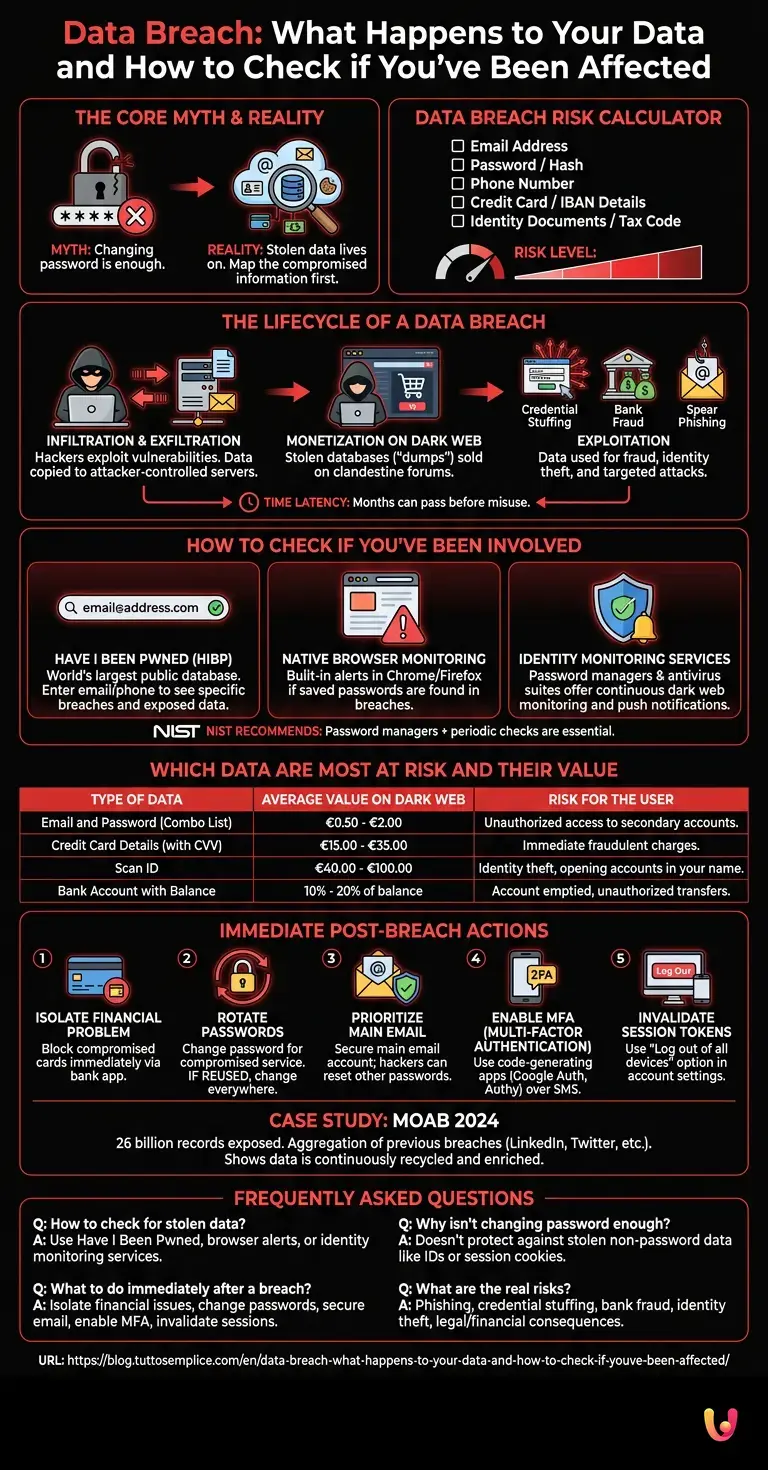
The safest and quickest way to check for data breaches is to use authoritative and free tools like Have I Been Pwned. By entering your email or phone number, the system cross-references the data with publicly released breached databases.
Checking your exposure should not be an occasional operation, but a digital hygiene routine. Here are the most effective tools and methods to find out if your data has fallen into the wrong hands:
- Have I Been Pwned (HIBP): Created by security expert Troy Hunt, this is the world’s largest public database. By entering your email, it will show you exactly which specific breaches you were involved in and what types of data were exposed.
- Native Browser Monitoring: Modern browsers like Google Chrome and Mozilla Firefox have built-in alert systems. If you try to log in to a site with a password that is found in a breached database, the browser will immediately warn you.
- Identity Monitoring Services: Many password managers (such as Bitwarden or 1Password) and antivirus suites offer continuous dark web monitoring, sending push notifications as soon as your data appears in a new dump.
According to official documentation from the NIST (National Institute of Standards and Technology), the use of password managers combined with periodic compromise checks is the basis of modern digital identity security.
Which Data Are Most at Risk and Their Value
When you decide to check for data breaches, you should know that not all data has the same value to criminals. Banking credentials and full identity documents are the most critical and profitable on the dark web’s black market.
To understand the extent of the potential damage, it is useful to look at the average “price list” of stolen data on the black markets. This helps us understand why hackers target specific platforms.
| Type of Data | Average Value on the Dark Web | Risk for the User |
|---|---|---|
| Email and Password (Combo List) | €0.50 – €2.00 | Unauthorized access to secondary accounts. |
| Credit Card Details (with CVV) | €15.00 – €35.00 | Immediate fraudulent charges. |
| Scan ID | €40.00 – €100.00 | Identity theft , opening of current accounts in one’s own name. |
| Bank Account with Balance | 10% – 20% of the balance | Account emptied, unauthorized transfers. |
As can be seen from the table, the compromise of a simple email generates a manageable risk, but the loss of identity documents opens the door to devastating legal and financial consequences that require formal complaints to the authorities.
Immediate Post-Breach Actions
After completing the operation to verify data breaches and discovering a real exposure, immediate actions include blocking cards, activating two-factor authentication (2FA), and rotating compromised passwords.
Panic is the worst enemy in the event of a breach. Follow this damage containment procedure in order of priority:
- Isolate the financial problem: If the breach concerns an e-commerce site or a bank, immediately block the credit cards saved on that portal through your bank’s app.
- Rotate your passwords: Change the password for the compromised service. Warning: if you used the same password on other sites (a practice that should be avoided at all costs), you must change it everywhere. Prioritize your main email account: if that falls, hackers can reset all other passwords.
- Enable MFA (Multi-Factor Authentication): Enable two-factor authentication wherever possible, preferring code-generating apps (such as Google Authenticator or Authy) over classic SMS, which are vulnerable to SIM Swapping attacks.
- Invalidate session tokens: In the security settings of your main accounts (Google, Meta , Microsoft), look for the “Log out of all devices” option. This will invalidate any stolen session cookies.
Case Study: The MOAB (Mother of all Breaches) of 2024
In early 2024, security researchers discovered an open database containing a staggering 26 billion exposed records. This was not a single attack, but a monstrous aggregation of previous breaches (including LinkedIn, Twitter, Tencent, and Adobe). This event demonstrated how stolen data never disappears: it is continuously aggregated, enriched, and resold. Millions of users who thought they were safe found themselves vulnerable to cross-credential stuffing attacks, making the ineffectiveness of old static passwords evident.
Conclusions

Absolute cybersecurity doesn’t exist. In the digital age, the question isn’t if your data will be involved in a breach, but when . Learning how to methodically check for data breaches and knowing exactly how to react makes the difference between a minor digital annoyance and a financial disaster.
Abandon the idea that a complex password is enough to be invulnerable. Adopt a password manager to generate unique credentials for each service, always activate two-factor authentication, and set up automatic alerts to monitor your digital identity. Proactivity is the only real shield against the criminal data industry.
Frequently Asked Questions

The quickest and most effective method is to use free and secure tools like Have I Been Pwned. By entering your email address or phone number, the system will show you which breaches you have been involved in. Additionally, you can take advantage of the alert systems integrated into modern browsers or the monitoring services offered by password managers to receive real-time notifications.
The first fundamental action is to isolate the problem by blocking any credit cards linked to the compromised service. Next, you need to change the breached password and make sure to change it on other sites as well if you were reusing it. It is crucial to secure your main email account, activate two-factor authentication via specific apps, and disconnect all devices to invalidate active sessions.
Updating credentials is useless if cybercriminals have stolen sensitive information that does not depend on a password, such as a tax identification number, identity documents, or session cookies. This personal data continues to circulate and can be sold on the dark web to commit fraud or identity theft. For this reason, it is essential to map exactly what information has been exposed.
After being exfiltrated from company servers, the information is usually put up for sale on clandestine forums on the dark web. Buyers then use these databases to launch targeted phishing attacks, test credentials on thousands of other sites, or commit bank fraud. The process can take months, which is why proactive monitoring of your digital identity is the best defense.
The most critical and profitable information on the black market is banking credentials and scans of complete identity documents. While compromising a simple email entails manageable risks, the theft of a document opens the door to serious legal and financial consequences, such as the unauthorized opening of current accounts, often requiring formal complaints to the competent authorities.
Still have doubts about Data Breach: What Happens to Your Data and How to Check if You’ve Been Affected?
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading






Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.