It is time to say goodbye. You have closed your suitcase, checked the drawers one last time, and headed toward the lobby. Upon reaching the reception desk, the ritual plays out exactly as it always does: you settle the bill, smile, and hand over your hotel key card . As the receptionist takes it and absent-mindedly places it on a reader or in a drawer, a question naturally arises in the minds of many travelers: what is actually written on that small piece of plastic? What fragments of our identity, our payments, or our habits remain trapped within the microchip or magnetic strip of that electronic key?
For years, a persistent urban legend has fueled the fears of tourists worldwide. It was rumored that hotel key cards contained credit card numbers, home addresses, phone numbers, and even details of minibar consumption—a treasure trove of sensitive information ready to fall into the wrong hands should the card be lost or stolen. But how much truth is there to this narrative? To fully understand the secret of the room, we must embark on a fascinating journey into the intricacies of hotel technology , debunking false myths and analyzing the real risks to our privacy.
Anatomy of a Myth: Are Personal Data at Risk?
Let’s start by reassuring the most anxious travelers: the vast majority of hotel key cards, whether equipped with a magnetic stripe or an RFID (Radio Frequency Identification) chip, do not contain your personal data. No name, no address, and, above all, no trace of your credit card information. This urban legend originated in the early 2000s, when an American police detective issued a warning—which later proved to be inaccurate and based on a single, misinterpreted case—claiming that criminals could extract financial data from lost hotel key cards.
The technical reality is much more pragmatic and, fortunately, more secure. The storage space on a typical magnetic key card or a basic RFID tag is extremely limited, often measurable in just a few bytes or kilobytes. Storing complex and sensitive data on a medium that is so easily lost would be not only cybersecurity suicide but also a needless waste of resources for the hotelier. But then, if our data isn’t there, how does the door know it is us and open?
How your room’s “brain” really works
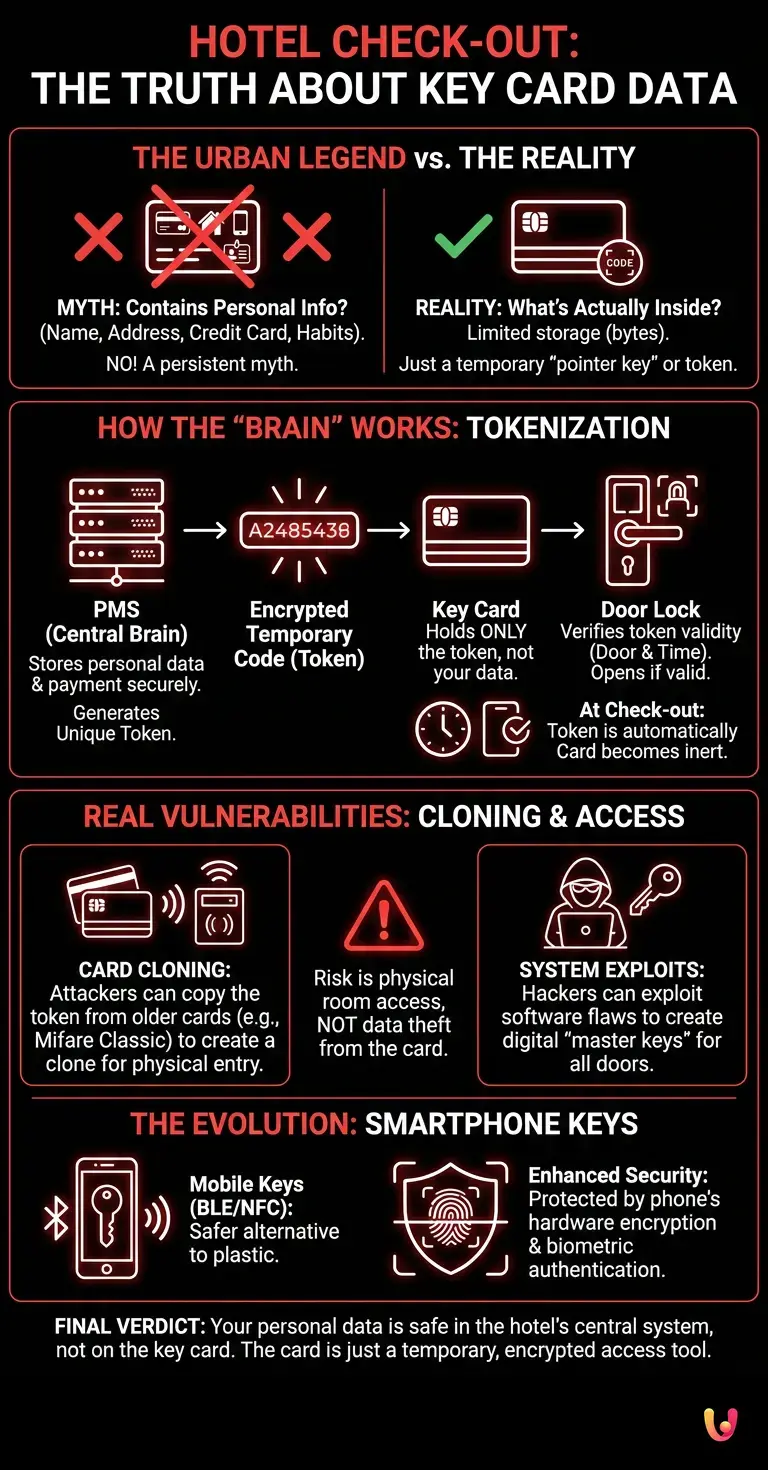
The secret behind how hotel key cards work lies in a fundamental concept of modern computing: tokenization . The card you hold in your hand is not a container for information, but simply a “pointer key”—a temporary token. When you check in, the receptionist uses central software called a PMS (Property Management System). This system is the true brain of the hotel: it is where your personal data, payment details, and the dates of your stay are stored.
The PMS generates a unique code string—a temporary, encrypted serial number—and associates it with your room for the exact duration of your reservation. This code is then written onto the key card. When you hold the card up to your room lock, the door does not read your name. It simply reads that code and verifies two fundamental parameters: “Is this code authorized for this specific door?” and “Do the current date and time fall within the validity window?” If the answer to both is yes, the mechanism engages and the door opens.
At the time of check-out, or upon the arrival of the deadline on the day of departure, the system automatically invalidates that code. The card becomes an inert piece of plastic, incapable of opening any door, until it is reprogrammed for the next guest with a completely new and different code.
The Real Vulnerabilities: Clones and Ghost Access

While our personal and financial data are secure within the hotel’s central database—which is protected by firewalls and security protocols far more robust than a plastic card—the cybersecurity of electronic locks is not without flaws. The real risk is not that someone will steal your identity from the card, but that someone will clone the card to physically enter your room while you are inside, or while your valuables are there.
Many hotels, especially those that have not updated their systems recently, still use outdated RFID standards, such as the Mifare Classic protocol. These systems have been extensively studied by security researchers, and their cryptographic keys can be cracked in a matter of seconds using devices that are easily available online . A malicious actor passing near you with a hidden reader could, in theory, copy your card’s unique code and transfer it onto a blank card, creating a perfect clone of your key.
Furthermore, in recent years, the hacker community has brought to light far more serious system-level vulnerabilities. Researchers have demonstrated how, starting with any expired hotel key, it is possible to exploit flaws in the code-generation software to create a digital “passe-partout”—a master key capable of opening every door in the building. These incidents have compelled major hotel lock manufacturers to release massive firmware updates, demonstrating how physical and digital security are now inextricably linked.
The Evolution: From Smartphones to Startup Solutions
To address these challenges and enhance the user experience, the hospitality industry is embracing rapid digital innovation . The plastic card is slowly giving way to smartphones. Many international hotel chains now allow guests to check in via an app and use their phones as room keys, leveraging Bluetooth Low Energy (BLE) or Near Field Communication (NFC) technology.
This shift is not merely a matter of convenience; it represents a quantum leap in security. The digital keys stored in our smartphone wallets are protected by the phone’s own cryptographic hardware (such as Apple’s Secure Enclave or Google’s Titan chip) and require biometric authentication (fingerprint or facial recognition) to be used. Furthermore, several startups are developing access systems based on blockchain and decentralized identity, in which the access token is unequivocally linked to the user’s device and cannot be intercepted or cloned by third parties.
These new technologies also allow hotels to manage access in a much more granular way. For example, it is possible to send a temporary digital key to a cleaner that is valid for only 15 minutes, or to instantly revoke a guest’s access in the event of any issues—all remotely and without having to deal with physical locks or lost key cards.
In Brief (TL;DR)
Contrary to a widespread urban legend, hotel key cards do not contain your personal or financial data, ensuring the privacy of travelers.
These cards utilize tokenization, employing an encrypted temporary code that allows the door to be opened exclusively during the dates of your reservation.
The real security risk is not identity theft, but the potential cloning of your key card to gain physical access to your room.
Conclusions

The next time you hand over your electronic key at the reception desk, you can do so with the peace of mind of someone who knows the room’s secret. That small rectangle of plastic is not a secret diary safeguarding your banking details or personal information, but a simple, temporary digital pass. The true guardian of your privacy is the hotel’s central computer system, the defenses of which depend on the establishment’s seriousness and investment in data protection.
However, awareness must not turn into complacency. Although your data may be secure, the physical security of your room still depends on the robustness of the technology used for the locks. Always using the manual deadbolt or security chain while inside your room remains a timeless golden rule. Technology evolves, systems become smarter, and keys are dematerializing into our smartphones, but a traveler’s common sense remains—today just as in the past—the first and most effective line of defense.
Frequently Asked Questions

Hotel key cards do not contain personal data, addresses, or credit card numbers. They simply store a temporary, encrypted code that signals to the room lock whether you are authorized to enter at that specific moment. Your sensitive data remains secure within the hotel’s central computer system, making the card a simple temporary pass.
The primary risk is not the theft of personal data, but the potential cloning of the key card to gain physical access to the room. Outdated systems can be compromised by malicious individuals to create copies of the key. For this reason, it is always advisable to use the manual deadbolt or security chain when inside your room.
Upon your departure or at the expiration of the time limit for your stay, the central system automatically invalidates the code associated with your room. From that moment on, the key card becomes inactive and unable to open any doors. It will only function again once it has been reprogrammed by the reception with a completely new code for the next guest.
Many establishments allow guests to use their phones as keys via advanced wireless technologies. This solution offers significantly higher security compared to plastic cards, as digital keys are protected by the mobile device’s encryption systems. Furthermore, they require unlocking via fingerprint or facial recognition, making unauthorized entry into the room by third parties nearly impossible.
Customers’ financial information and personal details are stored exclusively in the central management software. This database is protected by firewalls and very strict cybersecurity protocols. None of this sensitive information is ever transferred or copied onto the key card issued to you upon your arrival at the facility.
Still have doubts about Hotel Check-Out: The Truth About the Data on Your Key Card?
Type your specific question here to instantly find the official reply from Google.







Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.