You lock the door, activate your state-of-the-art alarm system, check that the cameras are running, and set off, convinced that you have secured your home. Yet, as you pull away, there is a seemingly harmless device that continues to transmit valuable and detailed information about you, your family, and your habits. The primary source of this silent data leak is the smart meter , the electronic device that has replaced the old spinning-disk meters in almost every Italian and European home. But what exactly does the power grid reveal when you are not there, and why does this data transmission represent one of the most fascinating and complex challenges of our time?
To understand the scope of this phenomenon, it is necessary to take a step back and analyze the very nature of the energy we consume. Until a few decades ago, electricity consumption was an aggregate figure: a technician would visit once a year to read a cumulative meter reading, from which total consumption was derived. Today, the technology underpinning smart grids requires constant, two-way communication. Modern meters record energy usage at intervals ranging from every fifteen minutes down to—in some advanced systems—fractions of a second. This continuous stream of data is the beating heart of digital innovation in the energy sector, essential for balancing the grid, integrating renewable sources, and preventing blackouts. However, this very granularity transforms the meter into a potential digital eye trained on the privacy of the home.
The Digital Footprint of Household Appliances
The secret behind this profiling capability lies in a technique known to experts as NILM (Non-Intrusive Load Monitoring) . The basic idea is as simple as it is brilliant: every appliance, when switched on, consumes energy in a unique and distinctive way. It is not merely a matter of the number of watts consumed, but of the “shape” that this consumption takes over time.
A refrigerator, for example, has a very regular compressor on-off cycle, featuring an initial inrush peak followed by constant power consumption. A washing machine presents a complex profile, consisting of water heating (high linear consumption) alternating with motor cycles for drum rotation. A modern television, especially an OLED or LED model, varies its electrical consumption based on the brightness of the scenes displayed on the screen. By analyzing a home’s total load curve using machine learning algorithms, it is possible to disaggregate the data and isolate individual “electrical signatures.”
What does this mean in practice? It means that anyone with access to this high-frequency raw data sees more than just how many kilowatt-hours you have consumed. They can see what time you woke up (indicated by the coffee machine or kettle being switched on), whether you took a hot shower (activation of the water heater or electric boiler), what time you left the house (a drastic drop in baseline consumption), when you returned, and even—in scenarios involving extreme analysis—which television channel you were watching. When you leave home to go on vacation, your smart meter records an unmistakable pattern: the absence of human interaction with switches, interrupted only by the automatic cycles of the refrigerator. It is the unmistakable signature of an empty house.
The Dark Side of Digital Innovation
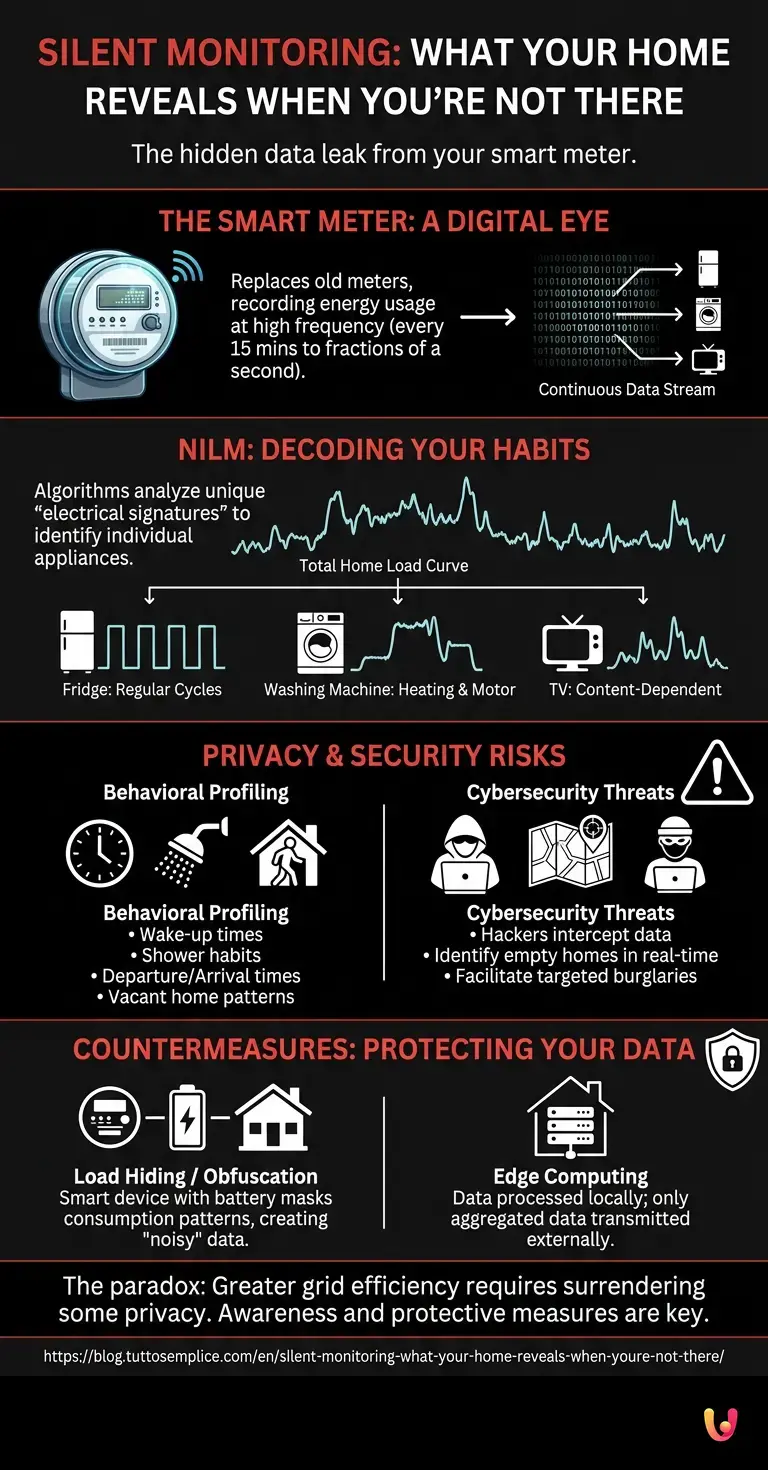
While the analysis of energy data enables providers to offer users more accurate bills and personalized energy-saving advice, it simultaneously creates gaping vulnerabilities regarding privacy. The paradox is evident: to make the grid more efficient and eco-friendly, we must surrender a significant portion of our privacy. When cross-referenced with other information, consumption data allows for the creation of highly precise behavioral profiles.
Consider the commercial implications. A company could deduce from your energy usage that you own an old, inefficient refrigerator and bombard you with targeted advertisements for a new appliance. Insurance companies could assess your lifestyle: do you stay up late? Do you frequently leave hazardous appliances running when you are away? This data could theoretically influence your insurance premiums. Although current European regulations, such as the GDPR, provide a robust shield against the indiscriminate use of this information for commercial profiling without explicit consent, the risk of misuse or data breaches remains a central theme in today’s technological debate.
A target for crime and cybersecurity
The issue takes on even more critical dimensions when we shift our focus from marketing to cybersecurity . Smart meters are, for all intents and purposes, IoT (Internet of Things) devices connected to a network. They transmit data to transformer substations using Power Line Communication (PLC) or cellular networks, and from there to the servers of energy distributors. Although the encryption protocols employed by national operators are generally of the highest standard, the history of cybersecurity teaches us that no system is inviolable.
What happens if a group of hackers manages to intercept or breach databases containing real-time consumption data? The consequences go far beyond identity theft. Malicious actors could create a real-time map of vacant homes in a specific neighborhood. Burglars would no longer need to stake out a location for days to study their victims’ habits; they would simply need to query a database to know with mathematical certainty that the Rossi family has gone on vacation, as their electricity consumption has remained flat for 48 hours.
Furthermore, the vulnerability lies not only in the meter itself but within the home ecosystem. Many users connect their meters to third-party home automation devices to monitor consumption via apps on their smartphones. If these apps or the servers managing them are not adequately protected, they become an ideal entry point for cybercriminals, effectively bypassing the defenses established by the energy distributor.
Countermeasures: Encryption and the Role of Startups
Faced with these threats, the research and industrial sectors have not stood idly by. The protection of energy data has become an absolute priority. At the infrastructural level, constant work is underway to update cryptographic protocols and implement zero-trust network architectures, in which every single data packet must be authenticated before being processed.
However, the most interesting aspect concerns solutions developed to protect privacy directly at the source. In recent years, several technology startups have begun proposing “Load Hiding” or load obfuscation solutions. How do they work? The idea is to install a smart device—often equipped with a small storage battery—between the meter and the home electrical system. This system acts as a filter: when you turn on an appliance, energy is drawn partly from the grid and partly from the battery, either in a completely random manner or by following specific algorithms. The result is that the smart meter registers a “noisy” and constant level of electricity consumption, devoid of the peaks and valleys that allow individual appliances to be identified. Your home’s electrical signature is thus masked, making it impossible for anyone—from the grid operator to a hacker—to deduce your habits or determine whether you are at home.
Other solutions rely on Edge Computing: data processing takes place locally, within a secure home hub. In this scenario, the system analyzes consumption to provide you with savings recommendations, but transmits only highly aggregated data externally (for example, total daily consumption), while keeping the high-frequency data required for NILM disaggregation within the home.
In Brief (TL;DR)
Smart meters constantly record electricity consumption, transforming into devices capable of silently monitoring our every daily domestic habit.
Current technology analyzes the energy signatures of household appliances to reveal our daily habits and prolonged absences from home with great precision.
This massive collection of data optimizes energy management but exposes users to serious risks related to privacy, profiling, and cybersecurity.
Conclusions

The transition to smart grids is an essential step toward ensuring a sustainable and efficient energy future capable of supporting the renewable energy revolution. However, this evolution brings with it unprecedented challenges that redefine the very concept of domestic privacy . The smart meter, once a simple measuring device, has transformed into an extremely powerful environmental sensor capable of translating our behaviors into bytes.
Being aware of what our electrical grid reveals about us when we leave home is the first step toward protecting ourselves. While the regulations and cybersecurity infrastructures of major distributors offer significant safeguards, it is equally crucial for end users to understand the value of their energy data. The integration of new obfuscation technologies and the careful management of connected smart home devices will become increasingly vital. In the delicate balance between digital innovation and the right to privacy, the true challenge of the coming years will not merely be producing clean energy, but ensuring that the way we consume it remains, should we so desire, a strictly private matter.
Frequently Asked Questions

A state-of-the-art meter monitors electricity consumption with extremely high frequency, recording variations every quarter of an hour or even within fractions of a second. This continuous stream of data serves to balance the national power grid and integrate renewable sources, but it also creates a highly detailed profile of each user’s household habits.
Identification is achieved through a technique called non-intrusive load monitoring. Each electrical appliance has its own unique energy signature, based on the amount of energy consumed and variations over time. By analyzing these consumption peaks, advanced algorithms can determine whether a person has turned on a washing machine, a refrigerator, or a television.
Information regarding electricity consumption reveals intimate details of daily life, such as the times you wake up or leave the house. If intercepted by malicious actors, this data clearly indicates when a home is left vacant, increasing the risk of burglary. Furthermore, there is a danger of unauthorized commercial profiling based on your lifestyle.
To protect privacy, load obfuscation systems can be used; these employ small batteries to keep electricity consumption constant and mask the operation of individual appliances. An alternative solution involves processing data locally by analyzing information within the home network and transmitting only generic, aggregated statistics to the utility provider.
Cybercriminals target connected devices to access real-time consumption databases. By obtaining this information, they can create precise maps of homes that are unoccupied at any given time, facilitating burglaries without the need for physical surveillance. Poorly secured third-party applications are often the preferred entry point for bypassing defenses.
Still have doubts about Silent Monitoring: What Your Home Reveals When You’re Not There?
Type your specific question here to instantly find the official reply from Google.
Sources and Further Reading







Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.