All of us have experienced, at least once, that subtle cold shiver down our spine: the smartphone battery icon that inexorably turns red, the percentage dropping below the critical threshold of 10%, just as we are facing a long train journey, waiting for an intercontinental flight at the airport, or sitting in a waiting room. In those moments of disconnection anxiety, salvation often appears in the form of a convenient and inviting USB socket embedded in the seat in front of us or in a public charging station. We plug in our cable, breathe a sigh of relief seeing the charging symbol activate, and go back to scrolling our feeds or working. Yet, in that precise and seemingly innocuous instant, we could be victims of a silent and sophisticated threat known to experts as Juice Jacking . This phenomenon represents the true, invisible toll we pay for our insatiable hunger for mobile energy. But why does such a daily and trivial gesture hide such a high risk for our privacy?
The psychology of a dead battery and the perfect bait
To fully understand the nature of this trap, we must first analyze the human context. We live in an era where our smartphone is no longer just a phone, but an extension of our identity, the custodian of our bank accounts , our work communications, and our most intimate memories. The fear of being disconnected, clinically defined as nomophobia (no-mobile-phone phobia), drives us to drastically lower our rational defenses. When the battery dies, our primary need becomes to restore power at any cost. Malicious actors are perfectly aware of this psychological vulnerability. A public USB port, strategically placed in a high-traffic area with tired and stressed travelers, represents the perfect bait. It requires no complex interactions, no clicking on suspicious links: it leverages a physical need of our device, transforming a service infrastructure into a potential Trojan horse.
The Anatomy of a Cable: The Dual Track of Technology
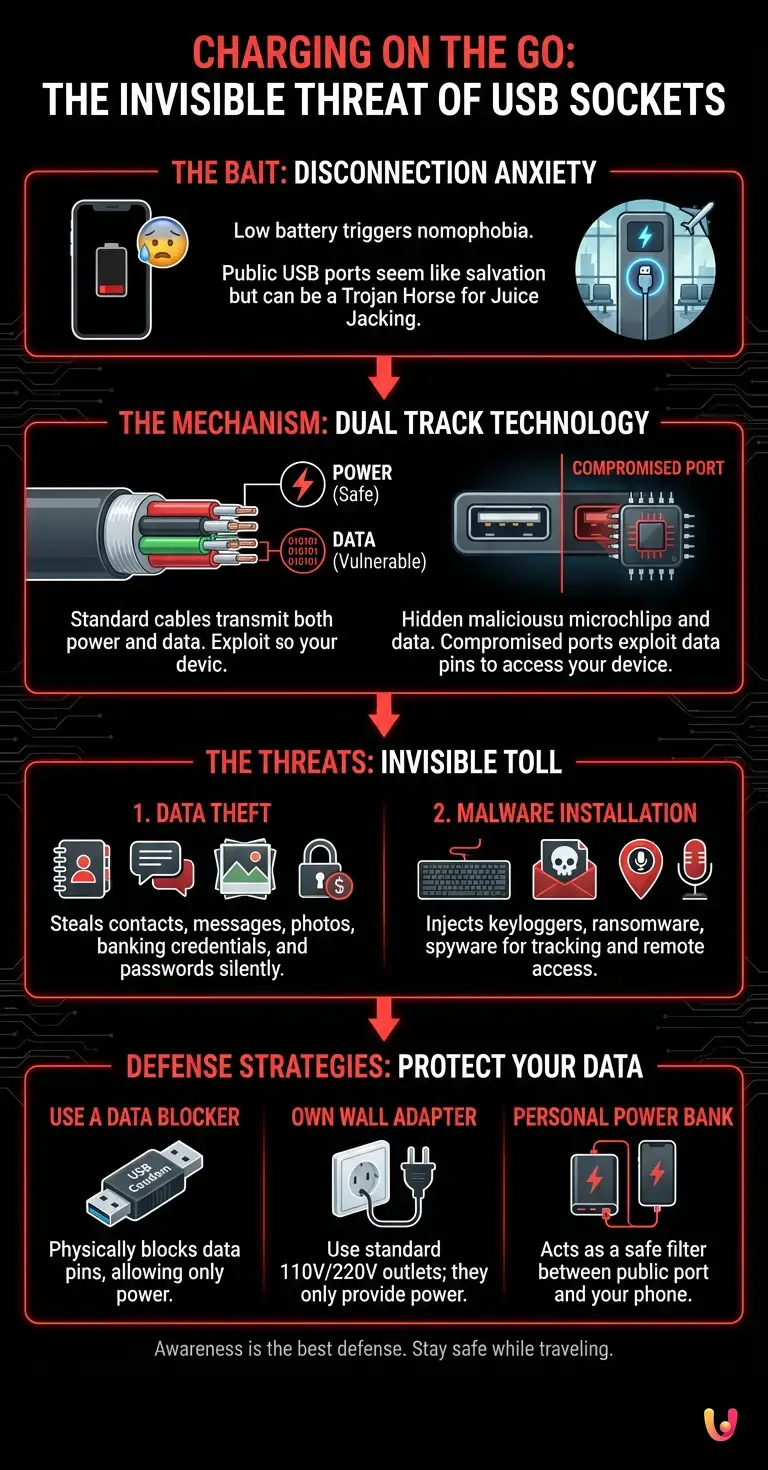
The secret behind this vulnerability lies in the very nature of USB (Universal Serial Bus) technology . When we look at the connector of our charging cable , we tend to think of it as a simple tube through which electricity flows. The engineering reality is quite different. A standard USB cable is made up of several pins (or metal contacts) and internal wires. Some of these are dedicated exclusively to transmitting electrical energy (the power and ground pins), but others are specifically designed for data transfer. It is this “dual track” that makes our devices vulnerable. When we connect our smartphone to our home computer, we use the exact same cable to both charge the battery and transfer photos or sync files. The USB protocol was designed to be plug-and-play , meaning it initiates immediate communication between connected devices. When we plug the cable into a public outlet, we cannot know for sure whether behind that plastic panel there is only a harmless current transformer or a microcomputer programmed to query our device through the data pins.
The invisible toll: how the attack happens behind the scenes
What exactly happens when the connector enters the compromised port? What is technically called a handshake phase begins. The device and the power source exchange basic information to determine how much power to deliver and whether a data connection can be established. In a Juice Jacking scenario, the public USB port has been secretly modified or replaced by a cybercriminal. Behind the port is malicious hardware, often the size of a matchbox, capable of bypassing normal security checks. Although modern operating systems (both iOS and Android) have introduced protective measures, asking the user if they want to “Trust this computer” or select “Charging only” mode, cybersecurity specialists warn that these defenses are not infallible. Sophisticated exploits exist that can bypass these prompts, exploiting unpatched vulnerabilities in the phone’s USB controller, forcing a data channel open while the user believes they are simply receiving power.
The two faces of the threat: exfiltration and infection
Once the data channel has been compromised, the attack can take two main directions, both devastating for the user’s cybersecurity . The first is Data Theft . In a matter of seconds, the malicious device hidden behind the socket can silently start copying sensitive files. We are talking about contact lists, text messages, photographs, browsing history and, in the worst cases, login credentials saved in plain text or session tokens for banking apps. All this happens in the background, without the phone screen showing any anomaly. The second direction is Malware Installation . Instead of stealing data immediately, the compromised port injects malicious software into the smartphone. This malware can take different forms: from a keylogger that will record every password typed in the following days, to ransomware that will encrypt data and demand a ransom, to spyware designed to track GPS location and remotely activate the microphone and camera. In this scenario, the toll you pay for charging extends well beyond the duration of the trip.
The Evolution of the Threat and the Role of Innovation
The threat landscape is constantly evolving. Recently, researchers have demonstrated how it is possible to exploit USB-C ports and fast charging protocols to conduct even more complex attacks. Fast charging requires continuous data negotiation between the charger and the phone to adjust voltage and amperage; this need for constant communication offers criminals new windows of vulnerability to exploit. However, the world of digital innovation is not standing still. Many companies are developing hardware and software solutions to mitigate these risks. For example, more than one tech startup has launched passive protection devices on the market, demonstrating how ingenuity can counter emerging threats. Smartphone manufacturers are also implementing increasingly strict hardware isolation protocols, trying to physically separate power management from data management at the chip level until the user provides explicit biometric authentication.
Defense strategies: how to protect your data while traveling
Awareness is the first and most important line of defense. Knowing that the handrail on the train seat or the charging station at the airport could be compromised radically changes our approach. But how can we survive long journeys without sacrificing vital energy for our devices? There are several practical and infallible strategies.
First, use a Data Blocker (often colloquially called a “USB condom”). This is a small adapter, costing just a few euros, that is placed between your cable and the public socket. Its function is as simple as it is ingenious: it lacks the physical pins dedicated to data transfer. It only allows electricity to pass through, making any type of Juice Jacking physically impossible.
Secondly, the golden rule for experienced travelers: always carry your own wall adapter (the traditional “plug”) and use standard 220V or 110V AC power outlets. Traditional electrical outlets have no data transmission capability; they only provide power. Although less common than USB ports in older modes of transport, they are by far the safest option.
Finally, the use of a personal power bank. Recharging your power bank from a public outlet and then, subsequently or simultaneously, recharging your phone from the power bank creates a safety “cushion.” Standard power banks do not have complex operating systems vulnerable to data theft, effectively acting as an impregnable filter between the potentially infected power source and our precious smartphone.
Data Extraction Simulator
Find out how much data can be stolen in the first 60 seconds of connecting to a tampered public USB port.
Intercepted Traffic
In Brief (TL;DR)
The fear of our smartphone running out of battery leads us to use public USB sockets, exposing us to the dangerous phenomenon of Juice Jacking.
The risk stems from the very nature of USB cables, which are designed to simultaneously transfer both electrical power and our most sensitive personal data.
By connecting the device to compromised stations, hidden malicious hardware can quickly steal our private information or infect the system with dangerous viruses.
Conclusions

The hyper-connected world we live in offers unimaginable conveniences compared to just a few decades ago, transforming our means of transport into mobile offices and entertainment rooms. However, this convenience brings with it new responsibilities. The USB port embedded in the train or plane seat is the perfect symbol of this duality: an energy lifeline that can turn into a trap for our privacy. The invisible toll of Juice Jacking reminds us that, in the digital domain, trust should never be blindly granted, not even to a piece of plastic and metal that only promises to recharge our battery. Adopting simple precautions, such as using a data blocker or a traditional power outlet, is not an act of paranoia, but of healthy digital hygiene. The next time your battery drops to 1%, stop for a moment before plugging the cable into the first available port: protecting your data is worth much more than a quick charge.
Frequently Asked Questions

Juice Jacking is a silent cyber threat that occurs when you use a compromised public USB port to charge your smartphone. Cybercriminals physically modify these ports to steal sensitive personal data or install malicious software on the victim’s device. This attack exploits the dual nature of charging cables, which are designed to carry both electrical power and digital information simultaneously.
Public USB ports on trains or in airports may conceal malicious hardware that is invisible from the outside. When you plug in your device, the cable not only transmits electricity but also opens a data communication channel. If the port has been tampered with, hackers can bypass the operating system’s security controls to copy your private files or infect your phone with computer viruses.
To charge your device safely while traveling, it is advisable to use a traditional wall outlet with your own power adapter, as this only transmits power. Alternatively, you can rely on a personal power bank to use as a safe intermediary. If you must use a public USB port, the best solution is to purchase a data blocker, a small adapter that physically blocks the pins dedicated to information transfer.
A data blocker is a small, inexpensive security adapter that plugs in between the charging cable and the public USB port. Its internal structure is designed to allow only electrical current to pass through, physically eliminating the metal contacts necessary for information transfer. Using this tool makes any attempt at intrusion or data theft physically impossible, guaranteeing one hundred percent safe charging.
Through a compromised USB port, malicious actors can exfiltrate a large amount of sensitive information from your device in a matter of seconds. The main targets include your contact list, private messages, photos, web browsing history, and login credentials. In more serious cases, attackers can steal banking passwords or install spyware that can track your location and activate the microphone remotely.
Still have doubts about Charging on the go: the invisible threat of USB sockets?
Type your specific question here to instantly find the official reply from Google.






Did you find this article helpful? Is there another topic you’d like to see me cover?
Write it in the comments below! I take inspiration directly from your suggestions.